Abstract
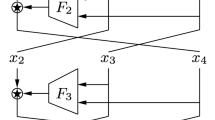
In this paper, we describe generic attacks on unbalanced Feistel schemes with contracting functions. These schemes are used to construct pseudo-random permutations from kn bits to kn bits by using d pseudo-random functions from (k–1)n bits to n bits. We describe known plaintext attacks (KPA) and non-adaptive chosen plaintext attacks (CPA-1) against these schemes with less than 2kn plaintext/ciphertext pairs and complexity strictly less than O(2kn) for a number of rounds d ≤2k –1. Consequently at least 2k rounds are necessary to avoid generic attacks. For k=3, we found attacks up to 6 rounds, so 7 rounds are required. When d ≥2k, we also describe some attacks on schemes with generators, (i.e. schemes where the d pseudo-random functions are generated) and where more than one permutation is required.
Chapter PDF
Similar content being viewed by others
Keywords
References
Aiello, W., Venkatesan, R.: Foiling Birthday Attacks in Length-Doubling Transformations. In: Maurer, U.M. (ed.) EUROCRYPT 1996. LNCS, vol. 1070, pp. 307–320. Springer, Heidelberg (1996)
Coppersmith, D.: Luby-Rackoff: Four rounds is not enough. Technical Report RC20674, IBM Research Report (December 1996)
Even, S., Goldreich, O.: Des-like functions can generate the alternating group. IEEE Transactions on Information Theory 29(6), 863–865 (1983)
Jutla, C.S.: Generalized Birthday Attacks on Unbalanced Feistel Networks. In: Krawczyk, H. (ed.) CRYPTO 1998. LNCS, vol. 1462, pp. 186–199. Springer, Heidelberg (1998)
Knudsen, L.R.: DEAL - A 128-bit Block Cipher. Technical Report 151, University of Bergen, Department of Informatics, Norway (February 1998)
Knudsen, L.R., Rijmen, V.: On the Decorrelated Fast Cipher (DFC) and Its Theory. In: Knudsen, L.R. (ed.) FSE 1999. LNCS, vol. 1636, pp. 81–94. Springer, Heidelberg (1999)
Luby, M., Rackoff, C.: How to Construct Pseudorandom Permutations from Pseudorandom Functions. SIAM J. Comput. 17(2), 373–386 (1988)
Lucks, S.: Faster Luby-Rackoff Ciphers. In: Gollmann, D. (ed.) FSE 1996. LNCS, vol. 1039, pp. 189–203. Springer, Heidelberg (1996)
Naor, M., Reingold, O.: On the Construction of Pseudorandom Permutations: Luby-Rackoff Revisited. J. Cryptology 12(1), 29–66 (1999)
Patarin, J.: New Results on Pseudorandom Permutation Generators Based on the DES Scheme. In: Feigenbaum, J. (ed.) CRYPTO 1991. LNCS, vol. 576, pp. 301–312. Springer, Heidelberg (1992)
Patarin, J.: Generic Attacks on Feistel Schemes. In: Boyd, C. (ed.) ASIACRYPT 2001. LNCS, vol. 2248, pp. 222–238. Springer, Heidelberg (2001)
Patarin, J.: Security of Random Feistel Schemes with 5 or More Rounds. In: Franklin, M. (ed.) CRYPTO 2004. LNCS, vol. 3152, pp. 106–122. Springer, Heidelberg (2004)
Patarin, J., Nachef, V., Berbain, C.: Generic Attacks on Unbalanced Feistel Schemes with Contracting Functions, Extended Version. Available from the authors (2006)
Patarin, J., Nachef, V., Berbain, C.: Generic Attacks on Unbalanced Feistel Schemes with Expanding Functions. Available from the authors (2006)
Schneier, B., Kelsey, J.: Unbalanced Feistel Networks and Block Cipher Design. In: Gollmann, D. (ed.) FSE 1996. LNCS, vol. 1039, pp. 121–144. Springer, Heidelberg (1996)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Patarin, J., Nachef, V., Berbain, C. (2006). Generic Attacks on Unbalanced Feistel Schemes with Contracting Functions. In: Lai, X., Chen, K. (eds) Advances in Cryptology – ASIACRYPT 2006. ASIACRYPT 2006. Lecture Notes in Computer Science, vol 4284. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11935230_26
Download citation
DOI: https://doi.org/10.1007/11935230_26
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-49475-1
Online ISBN: 978-3-540-49476-8
eBook Packages: Computer ScienceComputer Science (R0)