Abstract
Recently, Yu et al. (Quantum Inf Process 13(6):1457–1465, 2014) proposed the first semi-quantum scheme without the need of a classical channel to generate a secret key, while employing a “master key” and the entanglement properties of Bell states. This study points out a vulnerability that allows a malicious person to recover a partial master key and to launch a successful Man-In-The-Middle attack. Accordingly, we present the most likely leakage information scenarios where an outside attacker affects the security of the proposed protocol.
Similar content being viewed by others
References
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: Proceedings of IEEE Int. Conf. on Computers, Systems, and Signal Processing, Bangalore, (IEEE, New York), pp. 175–179 (1984)
Bennett, C.H., Bessette, F., Brassard, G., salvail, L., Smolin, J.: Experimental quantum cryptography. J. Cryptol. 5, 3–28 (1992)
Bennett, C.H.: Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 68, 3121 (1992)
Ekert, A.K.: Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67, 661 (1992)
Boyer, M., Gelles, R., Kenigsberg, D., Mor, T.: Quantum key distribution with classical Bob. Phys. Rev. Lett. 99, 140501 (2007)
Boyer, M., Gelles, R., Kenigsberg, D., Mor, T.: Semiquantum key distribution. Phys. Rev. A 79, 032341 (2009)
Yu, K.F., Yang, C.W., Liao, C.H., Hwang, T.: Authenticated semi-quantum key distribution protocol using Bell states. Quantum Inf. Process. 13(6), 1457–1465 (2014)
Barbieri, M., De Martini, F., Di Nepi, G., Mataloni, P., D’Ariano, G.M., Macchiavello, C.: Detection of entanglement with polarized photons: experimental realization of an entanglement witness. Phys. Rev. Lett. 91, 227901 (2003)
Gühne, O., Lütkenhaus, N.: Nonlinear entanglement witnesses. Phys. Rev. Lett. 96, 170502 (2006)
Kahn, D.: The Story of Secrete Writing, in the Codebreakers. Scribner, New York (1996)
Wright, P.: Spycatcher: the Candid Autobiography of a Senior Intelligence Officer. Viking, New York (1987)
Benson, R.L., Warner, M.: Introduction to Venona: Soviet Espionage and The American Response. Central Intelligence Agency, Washington, DC (1996)
Author information
Authors and Affiliations
Corresponding author
Appendices
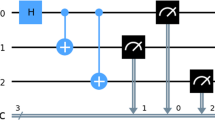
Appendix 1: The cracking algorithm in action
In this section, we run an example, based on our algorithm given in Sect. 3.2, in order to prove how we can recover the secret key \(K_3\). For that, we shorten Alice, Bob and Eve as A, B and E, respectively. We consider also, that E has recovered \(K_2\) and the communication protocol is in the second verification stage. We recall \(S_{1}\) are the measurement results that E captured and A have to broadcast publicly the MC sequence to B in order to perform the second check.
We tack the following measurement value for our example:
where the subset ”1” design the first run. According to our attack context, E possesses both \(S_{1}\) and \(MC_{1}\). Then, she starts the algorithm as follow:
-
\({\textcircled {1}}: \, {mrc}_{1}=?s_{1}\)
$$\begin{aligned} \left\{ \begin{array}{l l} {mrc}_{1}=s_{1}=1 \quad \Rightarrow (k_{3,1}=1 \quad \text {go to} \,{\textcircled {2}}) \end{array} \right. \end{aligned}$$ -
\({\textcircled {2}}: \, {mrc}_2=?s_2\)
$$\begin{aligned} \left\{ \begin{array}{l l} {mrc}_2=s_2=0 \quad \Rightarrow (k_{3,2}=1 \quad \text {go to}\, {\textcircled {e}}) \end{array} \right. \end{aligned}$$
after reaching the step \({\textcircled {e}}\), E constructs \(K_3\) respecting the rule given by:
-
Firstable, she concatenates the guessed values to form the first part.
-
Then she completes the rest by ”0” until reaching the correct \(K_3\) length.
Accordingly, the first potential key is \(K_3=1100\).
Then, E has to execute the discovery algorithm for a second time by shifting the last position when we have \({mrc}_2=?s_2\) by \({mrc}_2=?s_3\) and \(k_{3,2}=0\). In other words, E has to look for all next positions \(i+1\) which satisfy the condition \({mrc}=?s_{j>i}\) given that in the position i we had previously \({mrc}=s_i\) (we fix the position of \(\frac{n-1}{2}\) ”1” and we look for the other position that satisfy the condition \({mrc}=?s_{j>i}\)). Thus, we have:
-
\({\textcircled {1}}: \, {mrc}_{1}=?s_2\)
$$\begin{aligned} \left\{ \begin{array}{l l} {mrc}_{1}=s_{1}=1 \quad \Rightarrow (k_{3,1}=1 \quad \text {go to} {\textcircled {2}}) \end{array} \right. \end{aligned}$$ -
\({\textcircled {2}}: \,{mrc}_2=?s_3\)
$$\begin{aligned} \left\{ \begin{array}{ll} {mrc}_2\ne s_3=0 \quad \Rightarrow (k_{3,2}=k_{3,3}=0 \quad \text {go to next} s_4) \\ \end{array} \right. \left\{ \begin{array}{ll} {mrc}_2=s_4=1 \quad \Rightarrow (k_{3,4}=1 \quad \text {go to} {\textcircled {e}}) \end{array} \right. \end{aligned}$$
As before, when reaching the step \({\textcircled {e}}\), E constructs \(K_3\) respecting the rule given by:
-
Firstable, she concatenates the guessed values to form the first part.
-
Then she completes the rest by ”0” until reaching the correct \(K_3\) length.
Accordingly, the second potential key is \(K_3=1001\).
The previous process have to be conducted by fixing the first position to ”0” and the second one to ”1” and we look for the other position that satisfy the condition \({mrc}=?s_{j>2}\) and we continue so on. Thus, in our example we can see that all keys having this form \(K_3=01??\) can not lead to \(MC=10\). So we skip this step to the next form \(K_3=001?\). Therefore, When E runs the discovery algorithm against this form, we found that \(K_3=0011\) is also a potential key. Finally, E groups all those keys in set \({\mathcal {K}}_{1}=\left\{ [1100];[1001];[0011]\right\} \) representing all candidates key satisfying:
where \(\oplus \) is a mask operation defined in Eqs. (3) and (5).
Appendix 2: Example implementing the described attack
In order to recover the \(K_3\) key and implement a full Man-In-The-Middle attack, E has to record as many as possible the measurements sequences \(S_i\) and the correspondent \(MC_i\). For that, we consider two sequences \(S_{1}=1010\) and \(S_2=1001\) and two check sequences \(MC_{1}=10\) and \(MC_2=10\). According to the process described in the previous section, E possesses two sets \({\mathcal {K}}_{1}=\left\{ [1100];[1001];[0011]\right\} \) and \({\mathcal {K}}_2=\left\{ [1010];[0011]\right\} \). Thus, it is straightforward to see that:
however, as we constat that only \({\mathcal {K}}^{1}\cap {\mathcal {K}}^2=\left\{ [0011]\right\} \) will satisfy simultaneously the two tests. Then, we conclude that the real \(K_3\) is trivially [0011].
Rights and permissions
About this article
Cite this article
Meslouhi, A., Hassouni, Y. Cryptanalysis on authenticated semi-quantum key distribution protocol using Bell states. Quantum Inf Process 16, 18 (2017). https://doi.org/10.1007/s11128-016-1468-8
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-016-1468-8