Abstract
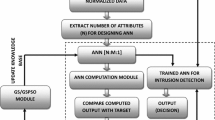
The aim of intrusion detection systems (IDSs) is to detect the malicious traffic and dynamic traffic which changes according to network characteristics, so intrusion detection system should be adaptive in nature. Many of IDS have been developed based on machine learning approaches. In proposed approach, experiment have been carried out on KDD-99 dataset with three classes DoS attack, other attacks and normal (without any attack). Paper checks the potential capability of optimization-based features with artificial neural network (ANN) classifier for the different types of intrusion attacks. A comparative analysis with ANN and other optimizer with ANN has been carried out. The experimental results show that the accuracy of intrusion detection using particle swarm optimization with genetic algorithm (PSO_GA) improves the results significantly by reducing false positive alarms and also improve individual class detection.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Ashfaq, R.A.R., et al.: Fuzziness based semi-supervised learning approach for intrusion detection system. Inf. Sci. 378, 484–497 (2017)
Lin, W.C., Ke, S.W., Tsai, C.F.: CANN: An intrusion detection system based on combining cluster centers and nearest neighbors. Knowl. Based Syst. 78, 13–21 (2015)
Harendra, V., Mirza, S., Mali, N.: Intrusion detection system. Int. J. Adv. Res. Eng. Sci. Technol. 3 (2016)
Ahmed, M., Mahmood, A.N., Jiankun, H.: A survey of network anomaly detection techniques. J. Netw. Comput. Appl. 60, 19–31 (2016)
Ashfaq, R.A.R., et al.: Fuzziness based semi-supervised learning approach for intrusion detection system. Inf. Sci. 378: 484–497 (2017)
Kang, M.J., Kang, J.W.: Intrusion detection system using deep neural network for in-vehicle network security. PLoS ONE 11(6), e0155781 (2016)
Ambusaidi, M.A., et al.: Building an intrusion detection system using a filter-based feature selection algorithm. IEEE Trans. Comput. 65(10): 2986–2998 (2016)
Erin Liong, V., et al.: Deep hashing for compact binary codes learning. In: Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition, pp. 2475–2483 (2015)
Patel, N.J., Jhaveri, R.H.: Detecting packet dropping nodes using machine learning techniques in Mobile ad-hoc network: A survey. In: International Conference on 2015 Signal Processing and Communication Engineering Systems (SPACES), pp. 468–472. IEEE (2015)
Alom, MZ., Taha, T.M.: Network intrusion detection for cyber security on neuromorphic computing system. In: International Joint Conference on 2017 Neural Networks (IJCNN), IEEE (2017)
Tavallaee, M., et al.: A detailed analysis of the KDD CUP 99 data set. In: IEEE Symposium on 2009 Computational Intelligence for Security and Defense Applications, CISDA 2009. IEEE (2009)
Sierra, M.R., Coello, C.A.C.: Improving PSO-based multi-objective optimization using crowding, mutation and e-dominance. In: Evolutionary Multi-criterion Optimization, vol. 3410, Springer, Berlin, Germany (2005)
Kim, Kyoung-jae, Han, Ingoo: Genetic algorithms approach to feature discretization in artificial neural networks for the prediction of stock price index. Expert Syst. Appl. 19(2), 125–132 (2000)
Lipowski, A., Lipowska, D.: Roulette-wheel selection via stochastic acceptance. Physica A: Stat. Mech. Appl. 391(6), 2193–2196 (2012)
Vassiliadis, S., et al.: Artificial neural networks and their applications in the engineering of fabrics. In: Woven Fabric Engineering, InTech (2010)
Paliwal, S., Gupta, R.: Denial-of-service, probing and remote to user (R2L) attack detection using genetic algorithm. Int. J. Comput. Appl. 60(19), 57–62 (2012)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Sachin, Rama Krishna, C. (2019). A Hybrid Approach to Mitigate False Positive Alarms in Intrusion Detection System. In: Smys, S., Bestak, R., Chen, JZ., Kotuliak, I. (eds) International Conference on Computer Networks and Communication Technologies. Lecture Notes on Data Engineering and Communications Technologies, vol 15. Springer, Singapore. https://doi.org/10.1007/978-981-10-8681-6_77
Download citation
DOI: https://doi.org/10.1007/978-981-10-8681-6_77
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-10-8680-9
Online ISBN: 978-981-10-8681-6
eBook Packages: EngineeringEngineering (R0)