Abstract
In this paper we show how to engineer proofs of security for software implementations of leakage-resilient cryptosystems on execution platforms with concurrency and caches. The proofs we derive are based on binary executables of the cryptosystem and on simple but realistic models of microprocessors.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Intel Advanced Encryption Standard (AES) Instructions Set, http://software.intel.com/file/24917
PolarSSL, http://polarssl.org/
Acıiçmez, O., Koç, Ç.K., Seifert, J.-P.: Predicting secret keys via branch prediction. In: Abe, M. (ed.) CT-RSA 2007. LNCS, vol. 4377, pp. 225–242. Springer, Heidelberg (2006)
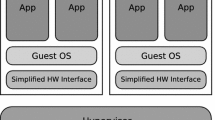
Barthe, G., Betarte, G., Campo, J.D., Luna, C.: Cache-Leakage Resilient OS Isolation in an Idealized Model of Virtualization. In: CSF. IEEE (2012)
Barthe, G., Grégoire, B., Heraud, S., Béguelin, S.Z.: Computer-aided security proofs for the working cryptographer. In: Rogaway, P. (ed.) CRYPTO 2011. LNCS, vol. 6841, pp. 71–90. Springer, Heidelberg (2011)
Bernstein, D.: Salsa20, http://cr.yp.to/snuffle.html
Bernstein, D.J.: Cache-timing attacks on AES. Technical report (2005)
Cousot, P., Cousot, R.: Abstract interpretation: a unified lattice model for static analysis of programs by construction of approximation of fixpoints. In: ACM (ed.) POPL (1977)
Doychev, G., Feld, D., Köpf, B., Mauborgne, L., Reineke, J.: CacheAudit: A Tool for the Static Analysis of Cache Side Channels. In: USENIX Security Symposium (2013)
Dziembowski, S., Pietrzak, K.: Leakage-Resilient Cryptography. In: FOCS. IEEE (2008)
Ferdinand, C., Martin, F., Wilhelm, R., Alt, M.: Cache behavior prediction by abstract interpretation. Science of Computer Programming 35(2), 163–189 (1999)
Grund, D.: Static Cache Analysis for Real-Time Systems – LRU, FIFO, PLRU. PhD thesis, Saarland University (2012)
Gullasch, D., Bangerter, E., Krenn, S.: Cache Games - Bringing Access-Based Cache Attacks on AES to Practice. In: S&P. IEEE (2011)
Jana, S., Shmatikov, V.: Memento: Learning secrets from process footprints. In: S&P. IEEE (2012)
Käsper, E., Schwabe, P.: Faster and timing-attack resistant AES-GCM. In: Clavier, C., Gaj, K. (eds.) CHES 2009. LNCS, vol. 5747, pp. 1–17. Springer, Heidelberg (2009)
Kim, T., Peinado, M., Mainar-Ruiz, G.: StealthMem: System-level protection against cache-based side channel attacks in the cloud. In: 19th USENIX Security Symposium. USENIX (2012)
Köpf, B., Mauborgne, L., Ochoa, M.: Automatic Quantification of Cache Side-Channels. In: Madhusudan, P., Seshia, S.A. (eds.) CAV 2012. LNCS, vol. 7358, pp. 564–580. Springer, Heidelberg (2012)
Köpf, B., Rybalchenko, A.: Approximation and Randomization for Quantitative Information-Flow Analysis. In: CSF. IEEE (2010)
Micali, S., Reyzin, L.: Physically observable cryptography. In: Naor, M. (ed.) TCC 2004. LNCS, vol. 2951, pp. 278–296. Springer, Heidelberg (2004)
Osvik, D.A., Shamir, A., Tromer, E.: Cache Attacks and Countermeasures: The Case of AES. In: Pointcheval, D. (ed.) CT-RSA 2006. LNCS, vol. 3860, pp. 1–20. Springer, Heidelberg (2006)
Pietrzak, K.: A leakage-resilient mode of operation. In: Joux, A. (ed.) EUROCRYPT 2009. LNCS, vol. 5479, pp. 462–482. Springer, Heidelberg (2009)
Ristenpart, T., Tromer, E., Shacham, H., Savage, S.: Hey, you, get off of my cloud: exploring information leakage in third-party compute clouds. In: CCS. ACM (2009)
Shoup, V.: Sequences of games: a tool for taming complexity in security proofs. Cryptology ePrint Archive, Report 2004/332 (2004)
Stefan, D., Buiras, P., Yang, E.Z., Levy, A., Terei, D., Russo, A., Mazières, D.: Eliminating cache-based timing attacks with instruction-based scheduling. In: Crampton, J., Jajodia, S., Mayes, K. (eds.) ESORICS 2013. LNCS, vol. 8134, pp. 718–735. Springer, Heidelberg (2013)
Yu, Y., Standaert, F.-X.: Practical leakage-resilient pseudorandom objects with minimum public randomness. In: Dawson, E. (ed.) CT-RSA 2013. LNCS, vol. 7779, pp. 223–238. Springer, Heidelberg (2013)
Yu, Y., Standaert, F.-X., Pereira, O., Yung, M.: Practical leakage-resilient pseudorandom generators. In: CCS. ACM (2010)
Zhang, D., Askarov, A., Myers, A.C.: Language-based control and mitigation of timing channels. In: PLDI. ACM (2012)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Barthe, G., Köpf, B., Mauborgne, L., Ochoa, M. (2014). Leakage Resilience against Concurrent Cache Attacks. In: Abadi, M., Kremer, S. (eds) Principles of Security and Trust. POST 2014. Lecture Notes in Computer Science, vol 8414. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-54792-8_8
Download citation
DOI: https://doi.org/10.1007/978-3-642-54792-8_8
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-54791-1
Online ISBN: 978-3-642-54792-8
eBook Packages: Computer ScienceComputer Science (R0)