Abstract
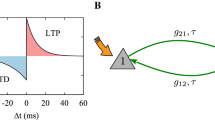
The phenomenon of neural networks synchronization by mutual learning can be used to construct key exchange protocol on an open channel. For security of this protocol it is important to minimize knowledge about synchronizing networks available to the potential attacker. The method presented herein permits evaluating the level of synchronization before it terminates. Subsequently, this research enables to assess the synchronizations, which are likely to be considered as long-time synchronizations. Once that occurs, it is preferable to launch another synchronization with the new selected weights as there is a high probability (as previously shown) that a new synchronization belongs to the short one.
Chapter PDF
Similar content being viewed by others
References
Menezes, A., Vanstone, S., Van Oorschot, P.: Handbook of Applied Cryptography. CRC Press (1996)
Stokłosa, J., Bilski, T., Pankowski, T.: Data Security in Informatical Systems, PWN (2001) (in Polish)
Stinson, D.R.: Cryptography, Theory and Practice. CRC Press (1995)
Kanter, I., Kinzel, W., Kanter, E.: Secure Exchange of Information by Synchronization of Neural Networks. Europhys. Lett. 57, 141–147 (2002)
Klein, E., Mislovaty, R., Kanter, I., Ruttor, A., Kinzel, W.: Synchronization of Neural Networks by Mutual Learning and its Application to Cryptography. In: Advances in Neural Information Processing Systems, vol. 17, pp. 689–696. MIT Press, Cambridge (2005)
Klimov, A., Mityagin, A., Shamir, A.: Analysis of Neural Cryptography. In: Zheng, Y. (ed.) ASIACRYPT 2002. LNCS, vol. 2501, pp. 288–298. Springer, Heidelberg (2002)
Ruttor, A.: Neural Synchronization and Cryptography, Ph.D. thesis, Würzburg (2006)
Ruttor, A., Kinzel, W., Naeh, R., Kanter, I.: Genetic Attack on Neural Cryptography. Phys. Rev. E 73(3), 036121–036129 (2006)
Dourlens, S.: Neuro-Cryptography. MSc Thesis, Dept. of Microcomputers and Microelectronics, University of Paris, France (1995)
Kotlarz, P., Kotulski, Z.: On Application of Neural Networks for S-Boxes Design. In: Szczepaniak, P.S., Kacprzyk, J., Niewiadomski, A. (eds.) AWIC 2005. LNCS (LNAI), vol. 3528, pp. 243–248. Springer, Heidelberg (2005)
Kanter, I., Kinzel, W.: Neural Cryptography, cond-mat/0208453 (2002)
Hassoun, M.: Fundamentals of Artificial Neural Networks. MIT Press (1995)
Osowski, S.: Neural Networks in Algorithmic Approach, WNT (1996) (in Polish)
Rutkowski, L.: Methods and Technics of Artificial Intelligence, PWN, Warsaw (2006) (in Polish)
Kanter, I., Kinzel, W.: The Theory of Neural Networks and Cryptography. In: Proceeding of the XXII Solvay Conference on Physics, The Physics of Communication, pp. 631–644 (2003)
Rosen-Zvi, M., Klein, E., Kanter, I., Kinzel, W.: Mutual Learning in a Tree Parity Machine and its Application to Cryptography. Phys. Rev. E 66, 066135 (2002)
Huntsberger, D.V.: Elements of Statistical Inference. Allyn and Bacon (1961)
Dolecki, M.: Tree Parity Machine Synchronization Time – Statistical Analysis. Mathematics, Physics and Informatics Series, Minsk 6(153), 149–151 (2012)
Dolecki, M., Kozera, R., Lenik, K.: The Evaluation of the TPM Synchronization on the Basis of their Outputs. Journal of Achievements in Materials and Manufacturing Engineering 57(2), 91–98 (2013)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 IFIP International Federation for Information Processing
About this paper
Cite this paper
Dolecki, M., Kozera, R. (2013). Threshold Method of Detecting Long-Time TPM Synchronization. In: Saeed, K., Chaki, R., Cortesi, A., Wierzchoń, S. (eds) Computer Information Systems and Industrial Management. CISIM 2013. Lecture Notes in Computer Science, vol 8104. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-40925-7_23
Download citation
DOI: https://doi.org/10.1007/978-3-642-40925-7_23
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-40924-0
Online ISBN: 978-3-642-40925-7
eBook Packages: Computer ScienceComputer Science (R0)