Abstract
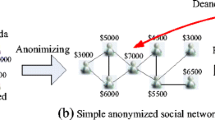
Social networks allow their users to mark their profile attributes, relationships as private in order to guarantee privacy, although private information get occasionally published within sanitized datasets offered to third parties, such as business partners. Today, powerful de-anonymization attacks exist that enable the finding of corresponding nodes within these datasets and public network data (e.g., crawls of other networks) solely by considering structural information. In this paper, we propose an identity management technique, namely identity separation, as a tool for hiding information from attacks aiming to achieve large-scale re-identification. By simulation experiments we compare the protective strength of identity management to the state-of-the-art attack. We show that while a large fraction of participating users are required to repel the attack, with the proper settings it is possible to effectively hide information, even for a handful of users. In addition, we propose a user-controllable method based on decoy nodes, which turn out to be successful for information hiding as at most 3.33% of hidden nodes are revealed in our experiments.
Chapter PDF
Similar content being viewed by others
References
Narayanan, A., Shmatikov, V.: De-anonymizing social networks. In: 30th IEEE Symposium on Security and Privacy, pp. 173–187. IEEE Press, New York (2009)
Narayanan, A., Shi, E., Rubinstein, B.I.P.: Link prediction by de-anonymization: How we won the kaggle social network challenge. In: The 2011 International Joint Conference on Neural Networks, pp. 1825–1834. IEEE Press, New York (2011)
Peng, W., Li, F., Zou, X., Wu, J.: Seed and Grow: An attack against anonymized social networks. In: 9th Annual IEEE Communications Society Conference on Sensor, Mesh and Ad Hoc Communications and Networks, pp. 587–595. IEEE Press, New York (2012)
Srivatsa, M., Hicks, M.: Deanonymizing mobility traces: Using social network as a side-channel. In: 2012 ACM Conference on Computer and Communications Security, pp. 628–637. ACM Press, New York (2012)
Gulyás, G.G., Imre, S.: Analysis of Identity Separation Against a Passive Clique-Based De-anonymization Attack. Infocommunications Journal III(4), 11–20 (2011)
Cutillo, L.A., Molva, R., Strufe, T.: Safebook: a Privacy Preserving Online Social Network Leveraging on Real-Life Trust. IEEE Communications Magazine 47(12), 94–101 (2009)
Beato, F., Conti, M., Preneel, B.: Friend in the Middle (FiM): Tackling De-Anonymization in Social Networks. In: 5th IEEE International Workshop on Security and Social Networking (2013)
Clauß, S., Kesdogan, D., Kölsch, T.: Privacy enhancing identity management: protection against re-identification and profiling. In: 2005 Workshop on Digital Identity Management, pp. 83–94. ACM Press, New York (2005)
Gulyás, G.G., Imre, S.: Measuring Local Topological Anonymity in Social Networks. In: 12th International Conference on Data Mining Workshops, pp. 563–570. IEEE Press, New York (2012)
Stanford Large Network Dataset Collection, http://snap.stanford.edu/data/index.html
Backstrom, L., Dwork, C., Kleinberg, J.: Wherefore art thou r3579x?: anonymized social networks, hidden patterns, and structural steganography. In: 16th International Conference on World Wide Web, pp. 181–190. ACM Press, New York (2007)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 IFIP International Federation for Information Processing
About this paper
Cite this paper
Gulyás, G.G., Imre, S. (2013). Hiding Information in Social Networks from De-anonymization Attacks by Using Identity Separation. In: De Decker, B., Dittmann, J., Kraetzer, C., Vielhauer, C. (eds) Communications and Multimedia Security. CMS 2013. Lecture Notes in Computer Science, vol 8099. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-40779-6_15
Download citation
DOI: https://doi.org/10.1007/978-3-642-40779-6_15
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-40778-9
Online ISBN: 978-3-642-40779-6
eBook Packages: Computer ScienceComputer Science (R0)