Abstract
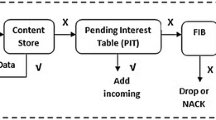
Content Centric Networking (CCN) [1] is a new network paradigm designed to satisfy user needs considering the growth of data demand. Named Data Networking (NDN) [2] is a research project that is developing the future Internet architecture using the principles behind CCN. In this novel architecture, the contents are addressed by their name and not by their location. Thus, the attention is shifted from user to content, resulting in a caching network that is more efficient and flexible than an IP network for content distribution and management with beneficial effects on timely delivery. In NDN, the content objects are divided into chunks, each digitally signed by its producer, and most papers assume that verification is made only by the content consumer. In order to perform signature verification, a node needs the signer’s key, which can be easily retrieved by issuing a standard interest message. Although content verification at the end node prevents disruptive attacks in which false data is delivered to applications, the verification of key validity is also necessary. Otherwise, false data would be cached and forwarded instead of correct data resulting in a denial of service and paving the way for more sophisticated attacks.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Jacobson, V., et al.: Networking named content. In: Proceedings of the 5th CoNEXT 2009, pp. 1–12. ACM, New York (2009)
Zhang, L., et al.: Named data networking (ndn) project. University of California and Arizona, Palo Alto Research Center and others, Tech. Rep. (October 2010)
Cooper, D., et al.: Internet x.509 public key infrastructure certificate and certificate revocation list (crl) profile. RFC 5280 (May 2008)
Myers, M., et al.: X.509 internet public key infrastructure,online certificate status protocol - ocsp. RFC 2560 (June 1999)
Afanasyev, A., et al.: ndnsim: Ndn simulator for ns-3. UCLA, Tech. Rep. (2012)
Bian, C., et al.: Deploying key management on ndn testbed. UCLA, Peking University and PARC, Tech. Rep. (February 2013)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 IFIP International Federation for Information Processing
About this paper
Cite this paper
Mauri, G., Verticale, G. (2013). Distributing Key Revocation Status in Named Data Networking. In: Bauschert, T. (eds) Advances in Communication Networking. EUNICE 2013. Lecture Notes in Computer Science, vol 8115. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-40552-5_31
Download citation
DOI: https://doi.org/10.1007/978-3-642-40552-5_31
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-40551-8
Online ISBN: 978-3-642-40552-5
eBook Packages: Computer ScienceComputer Science (R0)