Abstract
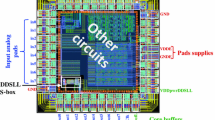
In a recent work from Eurocrypt 2011, Renauld et al. discussed the impact of the increased variability in nanoscale CMOS devices on their evaluation against side-channel attacks. In this paper, we complement this work by analyzing an implementation of the AES S-box, in the DDSLL dual-rail logic style, using the same 65-nanometer technology. For this purpose, we first compare the performance results of the static CMOS and dual-rail S-boxes. We show that full custom design allows to nicely mitigate the performance drawbacks that are usually reported for dual-rail circuits. Next, we evaluate the side-channel leakages of these S-boxes, using both simulations and actual measurements. We take advantage of state-of-the-art evaluation tools, and discuss the quantity and nature (e.g. linearity) of the physical information they provide. Our results show that the security improvement of the DDSLL S-box is typically in the range of one order of magnitude (in terms of “number of traces to recover the key”). They also confirm the importance of a profiled information theoretic analysis for the worst-case security evaluation of leaking devices. They finally raise the important question whether dual-rail logic styles remain a promising approach for reducing the side-channel information leakages in front of technology scaling, as hardware constraints such as balanced routing may become increasingly challenging to fulfill, as circuit sizes tend towards the nanometer scale.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Allam, M., Elmasry, M.: Dynamic current mode logic: a new low-power high-performance logic style. Journal of Solid State Circuits 36, 550–558 (2001)
Brier, E., Clavier, C., Olivier, F.: Correlation power analysis with a leakage model. In: Joye, M., Quisquater, J.-J. (eds.) CHES 2004. LNCS, vol. 3156, pp. 16–29. Springer, Heidelberg (2004)
Chari, S., Rao, J.R., Rohatgi, P.: Template attacks. In: Kaliski Jr., B.S., Koç, Ç.K., Paar, C. (eds.) CHES 2002. LNCS, vol. 2523, pp. 13–28. Springer, Heidelberg (2003)
Deniz, Z.T., Leblebici, Y.: Low-power current mode logic for improved dpa-resistance in embedded systems. In: ISCAS (2), pp. 1059–1062. IEEE, Los Alamitos (2005)
Doget, J., Prouff, E., Rivain, M., Standaert, F.-X.: Univariate side channel attacks and leakage modeling. Journal of Cryptographic Engineering (to appear)
Gierlichs, B., Batina, L., Tuyls, P., Preneel, B.: Mutual information analysis. In: Oswald, E., Rohatgi, P. (eds.) CHES 2008. LNCS, vol. 5154, pp. 426–442. Springer, Heidelberg (2008)
Gierlichs, B., Lemke-Rust, K., Paar, C.: Templates vs. Stochastic methods. In: Goubin, L., Matsui, M. (eds.) CHES 2006. LNCS, vol. 4249, pp. 15–29. Springer, Heidelberg (2006)
Hassoune, I., Macé, F., Flandre, D., Legat, J.-D.: Dynamic differential self-timed logic for robust and low-power security ics. Integration 40(3), 355–364 (2007)
Hwang, D.D., Tiri, K., Hodjat, A., Lai, B.-C., Yang, S., Schaumont, P., Verbauwhede, I.: Aes-based security coprocessor ic in 0.18um cmos with resistance to differential power analysis side-channel attacks. IEEE Journal of Solid-State Circuits 41(4), 781–792 (2006)
Kocher, P.C., Jaffe, J., Jun, B.: Differential power analysis. In: Wiener, M.J. (ed.) CRYPTO 1999. LNCS, vol. 1666, pp. 388–397. Springer, Heidelberg (1999)
Lemke-Rust, K.: Models and algorithms for physical cryptanalysis. PhD dissertation, University of Bochum (January 2007)
Lin, L., Burleson, W.P.: Analysis and mitigation of process variation impacts on power-attack tolerance. In: DAC, pp. 238–243. ACM, New York (2009)
Macé, F., Standaert, F.-X., Hassoune, I., Legat, J.-D.: A dynamic current mode logic to counteract power analysis attacks. In: DCIS, pp. 186–191 (2004)
Macé, F., Standaert, F.-X., Quisquater, J.-J.: Information theoretic evaluation of side-channel resistant logic styles. In: Paillier, P., Verbauwhede, I. (eds.) CHES 2007. LNCS, vol. 4727, pp. 427–442. Springer, Heidelberg (2007)
Macé, F., Standaert, F.-X., Quisquater, J.-J., Legat, J.-D.: A design methodology for secured iCs using dynamic current mode logic. In: Paliouras, V., Vounckx, J., Verkest, D. (eds.) PATMOS 2005. LNCS, vol. 3728, pp. 550–560. Springer, Heidelberg (2005)
Mangard, S., Oswald, E., Standaert, F.-X.: One for all - all for one: Unifying standard dpa attacks. IEEE Information Security 5(2), 100–110 (2011)
Mentens, N., Batina, L., Preneel, B., Verbauwhede, I.: A systematic evaluation of compact hardware implementations for the rijndael S-box. In: Menezes, A. (ed.) CT-RSA 2005. LNCS, vol. 3376, pp. 323–333. Springer, Heidelberg (2005)
Popp, T., Kirschbaum, M., Zefferer, T., Mangard, S.: Evaluation of the masked logic style mdpl on a prototype chip. In: CHES 2007 [19], pp. 81–94
Popp, T., Mangard, S.: Masked dual-rail pre-charge logic: Dpa-resistance without routing constraints. In: Rao and Sunar [20], pp. 172–186
Rao, J.R., Sunar, B. (eds.): CHES 2005. LNCS, vol. 3659. Springer, Heidelberg (2005)
Regazzoni, F., Eisenbarth, T., Poschmann, A., Großschädl, J., Gürkaynak, F.K., Macchetti, M., Deniz, Z.T., Pozzi, L., Paar, C., Leblebici, Y., Ienne, P.: Evaluating resistance of mcml technology to power analysis attacks using a simulation-based methodology. Transactions on Computational Science 4, 230–243 (2009)
Renauld, M., Standaert, F.-X., Veyrat-Charvillon, N., Kamel, D., Flandre, D.: A formal study of power variability issues and side-channel attacks for nanoscale devices. In: Paterson, K.G. (ed.) EUROCRYPT 2011. LNCS, vol. 6632, pp. 109–128. Springer, Heidelberg (2011)
Schindler, W., Lemke, K., Paar, C.: A stochastic model for differential side channel cryptanalysis. In: Rao and Sunar [20], pp. 30–46
Standaert, F.-X., Koeune, F., Schindler, W.: How to Compare Profiled Side-Channel Attacks? In: Abdalla, M., Pointcheval, D., Fouque, P.-A., Vergnaud, D. (eds.) ACNS 2009. LNCS, vol. 5536, pp. 485–498. Springer, Heidelberg (2009)
Standaert, F.-X., Malkin, T., Yung, M.: A unified framework for the analysis of side-channel key recovery attacks. In: Joux, A. (ed.) EUROCRYPT 2009. LNCS, vol. 5479, pp. 443–461. Springer, Heidelberg (2009)
Tiri, K., Verbauwhede, I.: A dynamic and differential cmos logic with signal indipendent power consumption to withstand differential power on smart cards. In: Proceedings of the 28th European Solid-State Circuits Conference (ESSCIRC 2002), Florence, Italy, pp. 403–406 (September 2002)
Tiri, K., Verbauwhede, I.: A logic level design methodology for a secure dpa resistant asic or fpga implementation. In: DATE, pp. 246–251 (2004)
Veyrat-Charvillon, N., Standaert, F.-X.: Generic side-channel distinguishers: Improvements and limitations. In: Rogaway, P. (ed.) CRYPTO 2011. LNCS, vol. 6841, pp. 354–372. Springer, Heidelberg (2011)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2011 International Association for Cryptologic Research
About this paper
Cite this paper
Renauld, M., Kamel, D., Standaert, FX., Flandre, D. (2011). Information Theoretic and Security Analysis of a 65-Nanometer DDSLL AES S-Box. In: Preneel, B., Takagi, T. (eds) Cryptographic Hardware and Embedded Systems – CHES 2011. CHES 2011. Lecture Notes in Computer Science, vol 6917. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-23951-9_15
Download citation
DOI: https://doi.org/10.1007/978-3-642-23951-9_15
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-23950-2
Online ISBN: 978-3-642-23951-9
eBook Packages: Computer ScienceComputer Science (R0)