Abstract
The notion of the proposed methodology is to optimize multidimensional nonlinear problem of conflicting nature that exists among imperceptibility and robustness in image watermarking. The methodology exploits the potentiality of Multi-Objective Genetic Algorithm (MOGA) in searching multiple non-dominated solutions lying on the Pareto front. The characteristics curve of the image are then analyzed and the most appropriate solution is selected using a merit function defined over evaluation measures. The efficacy of the suggested method is demonstrated by reporting the resultant watermarked images and restored watermarks extracted from their mean and median filtered versions.
Chapter PDF
Similar content being viewed by others
References
Ruanaidh, J.J.K.Ó., Pun, T.: Rotation, translation and scale invariant digital image watermarking. In: Proceedings of the International Conference on Image Processing, Santa Barbara, California, October 1997, vol. 1, pp. 536–539 (1997)
Bhandari, D., Murthy, C.A., Pal, S.K.: Image enhancement using multi-objective genetic algorithms. In: Chaudhury, S., Mitra, S., Murthy, C.A., Sastry, P.S., Pal, S.K. (eds.) PReMI 2009. LNCS, vol. 5909, pp. 309–314. Springer, Heidelberg (2009)
Ekstrom, M.P.: Digital image processing techniques. Academic Press, New York (1984)
Hansen, M.P., Jaszkiewicz, A.: Evaluating the quality of approximations to the non-dominated set. Technical Report Technical Report IMM-REP-1998-7, Institute of Mathematical Modelling, Technical University of Denmark (1998)
Huang, H.C., Pan, J.S., Huamg, Y.H., Huang, K.C.: Progressive watermarking techniques using genetic algorithms. Circuits, Systems and Signal Processing 8, 58–68 (2007)
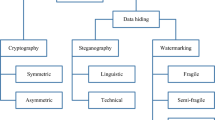
Katzenbeisser, S., Petitcolas, F.A.P.: Information hiding techniques for steganography and digital watermarking. Artech House Publishers (2000)
Maity, S.P., Kundu, M.K.: Genetic algorithms for optimality of data hiding in digital images. Soft Computing 13(4), 361–373 (2009)
Schilling, D.L., Pickholtz, R.L., Millstein, L.B.: Theory of spread spectrum communications-a tutorial. IEEE Transactions on Communications 30(5), 855–884 (1982)
Srinivas, N., Deb, K.: Multiobjective function optimization using nondominated sorting genetic algorithms. Evolutionary Computation 2(3), 221–248 (1995)
Gruhl, D., Bender, W., Morimoto, N.: Techniques for data hiding. In: Proceedings of the SPIE 2420, Storage and Retrieval for Image and Video Databases III, pp. 164–173 (1995)
Wang, Z., Bovik, A.C., Sheikh, H.R., Simoncelli, E.P.: Image quality assessment: From error visibility to structural similarity. IEEE Transactions on image processing 13(4), 600–612 (2004)
Xia, X.G., Boncelet, C.G., Arce, G.R.: A robust digital image watermarking method using wavelet-based fusion. In: Wavelet Transform Based Watermark for Digital Images, vol. 3, pp. 497–511. Optics Express (1998)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2011 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Bhandari, D., Kundu, L., Pal, S.K. (2011). Optimal Parameter Selection for Image Watermarking Using MOGA . In: Kuznetsov, S.O., Mandal, D.P., Kundu, M.K., Pal, S.K. (eds) Pattern Recognition and Machine Intelligence. PReMI 2011. Lecture Notes in Computer Science, vol 6744. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-21786-9_46
Download citation
DOI: https://doi.org/10.1007/978-3-642-21786-9_46
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-21785-2
Online ISBN: 978-3-642-21786-9
eBook Packages: Computer ScienceComputer Science (R0)