Abstract
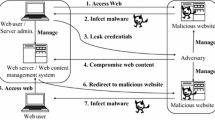
Client-based attacks on internet users with malicious web pages represent a serious and rising threat. Internet Browsers with enabled active content technologies such as JavaScript are vulnerable to so-called drive-by downloads. Drive-by downloads are able to automatically infect a victim’s system during a single visit of a crafted web page testing various vulnerabilities and installing e.g. malware files or illegal content without user interaction. In this paper we present MonkeyWrench, a low-interaction web-honeyclient allowing automatic identification of malicious web pages by performing static analysis of the HTML-objects in a web page as well as dynamic analysis of scripts by execution in an emulated browser environment. Using this hybrid approach MonkeyWrench overcomes shortcomings of existing low-interaction web-honeyclients in dealing with obfuscated JavaScript while outperforming high-interaction systems. Further MonkeyWrench is able to identify the exact vulnerability triggered by a malicious page and to extract payloads from within obfuscated scripts which are valuable information to security analysts and researchers. Results of an examination of several hundred thousand web pages demonstrate MonkeyWrench’s ability to expose rising threats of the web, and to collect malware and JavaScript exploit samples.
Chapter PDF
Similar content being viewed by others
References
The Honeynet Project CaptureHPC, https://projects.honeynet.org/capture-hpc/
Common Vulnerabilities and Exposures (CVE), http://cve.mitre.org/
libcurl, http://curl.haxx.se/libcurl/
MITRE Honeyclient Project, http://www.honeyclient.org/trac
Mozilla SpiderMonkey (JavaScript-C) Engine, http://www.mozilla.org/js/spidermonkey/
Seifert, C., Welch, I., Komisarczuk, P.: HoneyC - The Low-Interaction Client Honeypot. In: Proc. of the 2007 NZCSRCS. Waikato University, Hamilton (April 2007)
Seifert, C., Steenson, R., Holz, T., Yuan, B., Davis, M.A.: Know Your Enemy: Malicious Web Servers (August 2007), http://www.honeynet.org/papers/mws/
Provos, N., Mavrommatis, P., Rajab, M., Monrose, F.: All Your iFrames Point to Us. In: Proc. of the 17th USENIX Security Symposium (July 2008)
Provos, N., Holz, T.: Virtual Honeypots: From Botnet Tracking to Intrusion Detection. Addison-Wesley Professional, Reading (2007)
Wang, Y., Beck, D., Jiang, X., Roussev, R., Verbowski, C., Chen, S., King, S.: Automated Web Patrol with Strider HoneyMonkeys. In: Proc. of NDSS 2006 (2006)
Alexa the Web Information Company - Top Sites, http://www.alexa.com/topsites
CWSandbox – Automated Malware Analysis, http://www.cwsandbox.org/
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Büscher, A., Meier, M., Benzmüller, R. (2010). Throwing a MonkeyWrench into Web Attackers Plans. In: De Decker, B., Schaumüller-Bichl, I. (eds) Communications and Multimedia Security. CMS 2010. Lecture Notes in Computer Science, vol 6109. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-13241-4_4
Download citation
DOI: https://doi.org/10.1007/978-3-642-13241-4_4
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-13240-7
Online ISBN: 978-3-642-13241-4
eBook Packages: Computer ScienceComputer Science (R0)