Abstract
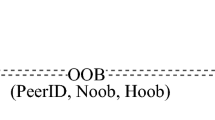
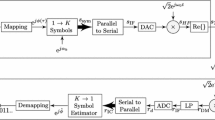
Protocols for bootstrapping security in ad hoc mobile device interactions rely on users’ ability to perform specific tasks such as transferring or comparing fingerprints of information between devices. The size of fingerprints depends on the level of technical security required by a given application but, at the same time, is limited by users’ inability to deal with large amounts of data with high levels of accuracy. Large fingerprints provide high technical security but potentially reduce usability of protocols which may result in users making mistakes that compromise security. This conflict between technical security and usability requires methods for transferring fingerprints between devices that maximise both to achieve acceptable effective security. In this paper, we propose two methods for transferring fingerprints between devices. We conducted a usability and security evaluation of the methods and our results show that, in contrast to previous proposals, our methods are both usable and resistant to security failures.
Chapter PDF
Similar content being viewed by others
References
Balfanz, D., Smetters, D.K., Stewart, P., Wong, H.C.: Talking to strangers: Authentication in ad-hoc wireless networks. In: Symposium on Network and Distributed Systems Security (NDSS 2002), San Diego, California (2002)
Feeney, L.M., Ahlgren, B., Westerlund, A.: Demonstration abstract: Spontaneous networking for secure collaborative applications in an infrastructureless environment. In: International conference on pervasive computing, Pervasive 2002 (2002)
Mayrhofer, R., Welch, M.: A human-verifiable authentication protocol using visible laser light. In: ARES 2007: Proceedings of the The Second International Conference on Availability, Reliability and Security, Washington, DC, USA, pp. 1143–1148. IEEE Computer Society, Los Alamitos (2007)
Saxena, N., Ekberg, J.E., Kostiainen, K., Asokan, N.: Secure Device Pairing based on a Visual Channel (Short Paper). In: SP 2006: Proceedings of the 2006 IEEE Symposium on Security and Privacy, Washington, DC, USA, pp. 306–313. IEEE Computer Society, Los Alamitos (2006)
Mayrhofer, R., Gellersen, H.: Shake well before use: Authentication based on Accelerometer Data. In: LaMarca, A., Langheinrich, M., Truong, K.N. (eds.) Pervasive 2007. LNCS, vol. 4480, pp. 144–161. Springer, Heidelberg (2007)
Saxena, N., Uddin, B., Jonathan, V.: Universal Device Pairing Using an Auxiliary Device. In: Symposium on Usable Privacy and Security (SOUPS) (July 2008)
Kainda, R., Flechais, I., Roscoe, A.: Usability and Security of Out-of-Band Channels in Secure Device Pairing Protocols. In: SOUPS 2009: Proceedings of the 5th symposium on Usable privacy and security (2009)
Kobsa, A., Sonawalla, R., Tsudik, G., Uzun, E., Wang, Y.: Serial Hook-ups: A Comparative Usability Study of Secure Device Pairing Methods. In: SOUPS 2009: Proceedings of the 5th symposium on Usable privacy and security (2009)
Soriente, C., Tsudik, G., Uzun, E.: BEDA: Button-Enabled Device Association. In: International Workshop on Security for Spontaneous Interaction, IWSSI (2007)
Juola, P.: Whole-word Phonetic Distance and the PGPfone Alphabet. In: Proceedings of Fourth International Conference on Spoken Language, ICSLP 1996, October 1996, vol. 1, pp. 98–101 (1996)
Haller, N.M.: The S/KEY one-time password system. In: Proceedings of the Symposium on Network and Distributed System Security, pp. 151–157 (1994)
Lewis, J.R.: IBM Computer Usability Satisfaction Questionnaires: Psychometric Evaluation and Instructions for Use. Int. J. Hum. -Comput. Interact. 7(1), 57–78 (1995)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 IFIP International Federation for Information Processing
About this paper
Cite this paper
Kainda, R., Flechais, I., Roscoe, A.W. (2010). Secure and Usable Out-Of-Band Channels for Ad Hoc Mobile Device Interactions. In: Samarati, P., Tunstall, M., Posegga, J., Markantonakis, K., Sauveron, D. (eds) Information Security Theory and Practices. Security and Privacy of Pervasive Systems and Smart Devices. WISTP 2010. Lecture Notes in Computer Science, vol 6033. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-12368-9_24
Download citation
DOI: https://doi.org/10.1007/978-3-642-12368-9_24
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-12367-2
Online ISBN: 978-3-642-12368-9
eBook Packages: Computer ScienceComputer Science (R0)