Abstract
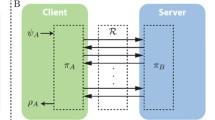
We study quantum protocols among two distrustful parties. Under the sole assumption of correctness—guaranteeing that honest players obtain their correct outcomes—we show that every protocol implementing a non-trivial primitive necessarily leaks information to a dishonest player. This extends known impossibility results to all non-trivial primitives. We provide a framework for quantifying this leakage and argue that leakage is a good measure for the privacy provided to the players by a given protocol. Our framework also covers the case where the two players are helped by a trusted third party. We show that despite the help of a trusted third party, the players cannot amplify the cryptographic power of any primitive. All our results hold even against quantum honest-but-curious adversaries who honestly follow the protocol but purify their actions and apply a different measurement at the end of the protocol. As concrete examples, we establish lower bounds on the leakage of standard universal two-party primitives such as oblivious transfer.
Chapter PDF
Similar content being viewed by others
References
Ambainis, A.: personal communication (2005)
Ariano, G.M.D., Kretschmann, D., Schlingemann, D., Werner, R.F.: Reexamination of quantum bit commitment: The possible and the impossible. Physical Review A (Atomic, Molecular, and Optical Physics) 76(3), 032328 (2007)
Barrett, J., Linden, N., Massar, S., Pironio, S., Popescu, S., Roberts, D.: Nonlocal correlations as an information-theoretic resource. Physical Review A 71, 022101 (2005)
Bennett, C.H., Brassard, G.: Quantum cryptography: Public key distribution and coin tossing. In: Proceedings of IEEE International Conference on Computers, Systems, and Signal Processing, pp. 175–179 (1984)
Berta, M.: Single-shot quantum state merging. Master’s thesis, ETH Zurich (2008)
Buhrman, H., Christandl, M., Hayden, P., Lo, H.-K., Wehner, S.: Possibility, impossibility and cheat-sensitivity of quantum bit string commitments. Physical Review A 78, 022316 (2008)
Buhrman, H., Christandl, M., Schaffner, C.: Impossibility of two-party secure function evaluation (in preparation, 2009)
Chailloux, A., Kerenidis, I.: Optimal quantum strong coin flipping (2009), http://arxiv.org/abs/0904.1511
Chor, B., Kushilevitz, E.: A zero-one law for boolean privacy. SIAM J. Discrete Math. 4(1), 36–47 (1991)
Colbeck, R.: The impossibility of secure two-party classical computation (August 2007), http://arxiv.org/abs/0708.2843
Damgård, I.B., Fehr, S., Salvail, L., Schaffner, C.: Secure identification and QKD in the bounded-quantum-storage model. In: Menezes, A. (ed.) CRYPTO 2007. LNCS, vol. 4622, pp. 342–359. Springer, Heidelberg (2007)
Fehr, S., Schaffner, C.: Composing quantum protocols in a classical environment. In: Reingold, O. (ed.) TCC 2009. LNCS, vol. 5444, pp. 350–367. Springer, Heidelberg (2009)
Fitzi, M., Wolf, S., Wullschleger, J.: Pseudo-signatures, broadcast, and multi-party computation from correlated randomness. In: Franklin, M. (ed.) CRYPTO 2004. LNCS, vol. 3152, pp. 562–579. Springer, Heidelberg (2004)
Holevo, A.S.: Information-theoretical aspects of quantum measurement. Problemy Peredači Informacii 9(2), 31–42 (1973)
Imai, H., Müller-Quade, J., Nascimento, A., Winter, A.: Rates for bit commitment and coin tossing from noisy correlation. In: Proceedings of 2004 IEEE International Symposium on Information Theory, p. 47 (June 2004)
Jozsa, R., Schlienz, J.: Distinguishability of states and von neumann entropy. Phys. Rev. A 62(1), 012301 (2000)
Kent, A.: Promising the impossible: Classical certification in a quantum world (2004), http://arxiv.org/abs/quant-ph/0409029
Kitaev, A.: Quantum coin-flipping. presented at QIP 2003. A review of this technique can be found in (2003), http://lightlike.com/~carlosm/publ
Klauck, H.: On quantum and approximate privacy. Theory of Computing Systems 37(1), 221–246 (2004); http://arxiv.org/abs/quant-ph/0110038 , also in the Proceedings of STACS (2002)
Künzler, R., Müller-Quade, J., Raub, D.: Secure computability of functions in the it setting with dishonest majority and applications to long-term security. In: Reingold, O. (ed.) TCC 2009. LNCS, vol. 5444, pp. 238–255. Springer, Heidelberg (2009)
Kushilevitz, E.: Privacy and communication complexity. SIAM J. Discrete Math. 5(2), 273–284 (1992)
Lo, H.-K.: Insecurity of quantum secure computations. Physical Review A 56(2), 1154–1162 (1997)
Lo, H.-K., Chau, H.F.: Is quantum bit commitment really possible? Physical Review Letters 78(17), 3410–3413 (1997)
Mayers, D.: Unconditionally secure quantum bit commitment is impossible. Physical Review Letters 78(17), 3414–3417 (1997)
Mochon, C.: Quantum weak coin-flipping with bias of 0.192. In: 45th Annual IEEE Symposium on Foundations of Computer Science (FOCS), pp. 2–11 (2004)
Mochon, C.: A large family of quantum weak coin-flipping protocols. Phys. Rev. A 72, 022341 (2005)
Mochon, C.: Quantum weak coin flipping with arbitrarily small bias (2007), http://arxiv.org/abs/0711.4114
Nielsen, M.A., Chuang, I.L.: Quantum Computation and Quantum Information. Cambridge University Press, Cambridge (2000)
Popescu, S., Rohrlich, D.: Quantum nonlocality as an axiom. Foundations of Physics 24(3), 379–385 (1994)
Renner, R., Wolf, S.: Simple and tight bounds for information reconciliation and privacy amplification. In: Roy, B. (ed.) ASIACRYPT 2005. LNCS, vol. 3788, pp. 199–216. Springer, Heidelberg (2005)
Renner, R., Wolf, S., Wullschleger, J.: The single-serving channel capacity. In: Proceedings of the International Symposium on Information Theory (ISIT). IEEE, Los Alamitos (July 2006), http://arxiv.org/abs/cs.IT/0608018
Ruskai, M.B.: Inequalities for quantum entropy: A review with conditions for equality. Journal of Mathematical Physics 43(9), 4358–4375 (2002)
Salvail, L., Sotáková, M., Schaffner, C.: On the power of two-party quantum cryptography (2009), http://arxiv.org/abs/0902.4036
Spekkens, R.W., Rudolph, T.: Degrees of concealment and bindingness in quantum bit commitment protocols. Phys. Rev. A 65(1), 012310 (2001)
Winter, A., Renner, R.: Single-shot state merging (2007) (unpublished note)
Wolf, S., Wullschleger, J.: Zero-error information and applications in cryptography. In: IEEE Information Theory Workshop (ITW), San Antonio, Texas (October 2004)
Wolf, S., Wullschleger, J.: New monotones and lower bounds in unconditional two-party computation. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 467–477. Springer, Heidelberg (2005)
Wolf, S., Wullschleger, J.: Oblivious transfer and quantum non-locality. In: International Symposium on Information Theory (ISIT 2005), pp. 1745–1748 (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Salvail, L., Schaffner, C., Sotáková, M. (2009). On the Power of Two-Party Quantum Cryptography. In: Matsui, M. (eds) Advances in Cryptology – ASIACRYPT 2009. ASIACRYPT 2009. Lecture Notes in Computer Science, vol 5912. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-10366-7_5
Download citation
DOI: https://doi.org/10.1007/978-3-642-10366-7_5
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-10365-0
Online ISBN: 978-3-642-10366-7
eBook Packages: Computer ScienceComputer Science (R0)