Abstract
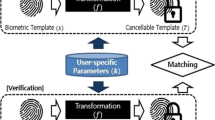
Binary biometric representations have great significance for data compression and template protection. In this paper, we introduce pairwise polar quantization. Furthermore, aiming to optimize the discrimination between the genuine Hamming distance (GHD) and the imposter Hamming distance (IHD), we propose two feature pairing strategies: the long-short (LS) strategy for phase quantization, as well as the long-long (LL) strategy for magnitude quantization. Experimental results for the FRGC face database and the FVC2000 fingerprint database show that phase bits provide reasonably good performance, whereas magnitude bits obtain poor performance.
Chapter PDF
Similar content being viewed by others
References
Jain, A.K., Nandakumar, K., Nagar, A.: Biometric template security. EURASIP Journal on Advances in Signal Processing 8(2) (2008)
Vielhauer, C., Steinmetz, R., Mayerhofer, A.: Biometric hash based on statistical features of online signatures. In: Proc. 16th International Conference on Pattern Recognition (ICPR 2002), Quebec, Canada, vol. 1, pp. 123–126 (2002)
Hao, F., Wah, C.C.: Private key generation from on-line handwritten signatures. Information Management & Computer Security 10(4), 159–164 (2002)
Chang, Y., Zhang, W., Chen, T.: Biometrics-based cryptographic key generation. In: Proc. IEEE International Conference on Multimedia and Expo. (ICME 2004), Taipei, Taiwan, vol. 3, pp. 2203–2206 (2004)
Tuyls, P., Akkermans, A.H.M., Kevenaar, T.A.M., Schrijen, G.J., Bazen, A.M., Veldhuis, R.N.J.: Practical biometric authentication with template protection. In: Kanade, T., Jain, A., Ratha, N.K. (eds.) AVBPA 2005. LNCS, vol. 3546, pp. 436–446. Springer, Heidelberg (2005)
Kevenaar, T.A.M., Schrijen, G.J., van der Veen, M., Akkermans, A.H.M., Zuo, F.: Face recognition with renewable and privacy preserving binary templates. In: Proc. IEEE Workshop on Automatic Identification Advanced Technologies (AutoID 2005), NY, USA, pp. 21–26 (2005)
Chen, C., Veldhuis, R.N.J., Kevenaar, T.A.M., Akkermans, A.H.M.: Multi-bits biometric string generation based on the likelihood ratio. In: Proc. IEEE Conference on Biometrics: Theory, Applications and Systems (BTAS 2007) (2007)
Chen, C., Veldhuis, R.N.J., Kevenaar, T.A.M., Akkermans, A.H.M.: Biometric binary string generation with detection rate optimized bit allocation. In: IEEE Computer Society Conference on Computer Vision and Pattern Recognition Workshops (CVPR 2008) (2008)
Pobloth, H., Vafin, R., Kleijn, W.B.: Multivariate block polar quantization. IEEE Transactions on Communications 53(12), 2043–2053 (2005)
Phillips, P.J., Flynn, P.J., Scruggs, W.T., Bowyer, K.W., Chang, J., Hoffman, K., Marques, J., Min, J., Worek, W.J.: Overview of the face recognition grand challenge. In: Proc. IEEE Computer Society Conference on Computer Vision and Pattern Recognition (CVPR 2005), MD, USA, pp. 947–954 (2005)
Maio, D., Maltoni, D., Cappelli, R., Wayman, J.L., Jain, A.K.: FVC 2000: Fingerprint verification competition. IEEE Transactions on Pattern Analysis and Machine Intelligence 24(3), 402–412 (2002)
Veldhuis, R.N.J., Bazen, A., Kauffman, J., Hartel, P.: Biometric verification based on grip-pattern recognition. In: Proc. SPIE Security, Steganography, and Watermarking of Multimedia Contents VI (SSWMC 2004), CA, USA, vol. 5306, pp. 634–641 (2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Chen, C., Veldhuis, R. (2009). Binary Biometric Representation through Pairwise Polar Quantization. In: Tistarelli, M., Nixon, M.S. (eds) Advances in Biometrics. ICB 2009. Lecture Notes in Computer Science, vol 5558. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-01793-3_8
Download citation
DOI: https://doi.org/10.1007/978-3-642-01793-3_8
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-01792-6
Online ISBN: 978-3-642-01793-3
eBook Packages: Computer ScienceComputer Science (R0)