Abstract
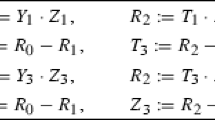
We present a new methodology to derive faster composite operations of the form dP + Q, where d is a small integer ≥ 2, for generic ECC scalar multiplications over prime fields. In particular, we present an efficient Doubling-Addition (DA) operation that can be exploited to accelerate most scalar multiplication methods, including multiscalar variants. We also present a new precomputation scheme useful for window-based scalar multiplication that is shown to achieve the lowest cost among all known methods using only one inversion. In comparison to the remaining approaches that use none or several inversions, our scheme offers higher performance for most common I/M ratios. By combining the benefits of our precomputation scheme and the new DA operation, we can save up to 6.2% on the scalar multiplication using fractional wNAF.
Chapter PDF
Similar content being viewed by others
Keywords
References
Avanzi, R., Cohen, H., Doche, C., Frey, G., Lange, T., Nguyen, K., Vercauteren, F.: Handbook of Elliptic and Hyperelliptic Curve Cryptography. CRC Press, Boca Raton (2005)
Brown, M., Hankerson, D., Lopez, J., Menezes, A.: Software Implementation of the NIST elliptic curves over prime fields. In: Naccache, D. (ed.) CT-RSA 2001. LNCS, vol. 2020, pp. 250–265. Springer, Heidelberg (2001)
Billet, O., Joye, M.: Fast Point Multiplication on Elliptic Curves through Isogenies. In: Fossorier, M.P.C., Høholdt, T., Poli, A. (eds.) AAECC 2003. LNCS, vol. 2643, pp. 43–50. Springer, Heidelberg (2003)
Ciet, M., Joye, M., Lauter, K., Montgomery, P.L.: Trading Inversions for Multiplications in Elliptic Curve Cryptography. Designs, Codes and Cryptography 39(2), 189–206 (2006)
Cohen, H., Miyaji, A., Ono, T.: Efficient Elliptic Curve Exponentiation using Mixed Coordinates. In: Ohta, K., Pei, D. (eds.) ASIACRYPT 1998. LNCS, vol. 1514, pp. 51–65. Springer, Heidelberg (1998)
Dahmen, E., Okeya, K., Schepers, D.: Affine Precomputation with Sole Inversion in Elliptic Curve Cryptography. In: Pieprzyk, J., Ghodosi, H., Dawson, E. (eds.) ACISP 2007. LNCS, vol. 4586, pp. 245–258. Springer, Heidelberg (2007)
Dimitrov, V., Imbert, L., Mishra, P.K.: Efficient and Secure Elliptic Curve Point Multiplication using Double-Base Chains. In: Roy, B. (ed.) ASIACRYPT 2005. LNCS, vol. 3788, pp. 59–78. Springer, Heidelberg (2005)
Doche, C., Icart, T., Kohel, D.: Efficient Scalar Multiplication by Isogeny Decompositions. In: Yung, M., Dodis, Y., Kiayias, A., Malkin, T.G. (eds.) PKC 2006. LNCS, vol. 3958, pp. 191–206. Springer, Heidelberg (2006)
Eisentraeger, K., Lauter, K., Montgomery, P.: Fast Elliptic Curve Arithmetic and Improved Weil Pairing Evaluation. In: Joye, M. (ed.) CT-RSA 2003. LNCS, vol. 2612, pp. 343–354. Springer, Heidelberg (2003)
Elmegaard-Fessel, L.: Efficient Scalar Multiplication and Security against Power Analysis in Cryptosystems based on the NIST Elliptic Curves over Prime Fields, Master Thesis, University of Copenhagen (2006)
FIPS PUB 186-2. Digital Signature Standard (DSS). National Institute of Standards and Technology (NIST) (2000)
Hankerson, D., Menezes, A., Vanstone, S.: Guide to Elliptic Curve Cryptography. Springer, Heidelberg (2004)
IEEE Std 1363-2000. IEEE Standard Specifications for Public-Key Cryptography. The Institute of Electrical and Electronics Engineers (IEEE) (2000)
Itoh, K., Takenaka, M., Torii, N., Temma, S., Kurihara, Y.: Fast Implementation of Public-Key Cryptography on a DSP TMS320C6201. In: Koç, Ç.K., Paar, C. (eds.) CHES 1999. LNCS, vol. 1717, pp. 61–72. Springer, Heidelberg (1999)
Lim, C.H., Hwang, H.S.: Fast implementation of Elliptic Curve Arithmetic in GF(pn). In: Imai, H., Zheng, Y. (eds.) PKC 2000. LNCS, vol. 1751, pp. 405–421. Springer, Heidelberg (2000)
Longa, P.: Accelerating the Scalar Multiplication on Elliptic Curve Cryptosystems over Prime Fields, Master’s Thesis, University of Ottawa (June 2007)
Longa, P., Miri, A.: Fast and Flexible Elliptic Curve Point Arithmetic over Prime Fields. IEEE Transactions on Computers (to appear, 2007), http://doi.ieeecomputersociety.org/10.1109/TC.2007.70815
Longa, P., Miri, A.: New Multibase Non-Adjacent Form Scalar Multiplication and its Application to Elliptic Curve Cryptosystems (submitted, 2007)
Meloni, N.: Fast and Secure Elliptic Curve Scalar Multiplication over Prime Fields using Special Addition Chains. Cryptology ePrint Archive, Report 2006/216 (2006)
Mishra, P.: Scalar Multiplication in Elliptic Curve Cryptosystems: Pipelining with Precomputations. Cryptology ePrint Archive, Report 2004/191 (2004)
Mishra, P., Dimitrov, V.: Efficient Quintuple Formulas for Elliptic Curves and Efficient Scalar Multiplication using Multibase Number Representation. Cryptology ePrint Archive, Report 2007/040 (2007)
Moller, B.: Improved Techniques for Fast Exponentiation. In: Lee, P.J., Lim, C.H. (eds.) ICISC 2002. LNCS, vol. 2587, pp. 298–312. Springer, Heidelberg (2003)
Solinas, J.: Generalized Mersenne Numbers, Technical Report CORR-99-39, Dept. of C&O, University of Waterloo (1999)
Takagi, T., Yen, S.-M., Wu, B.-C.: Radix-r Non-Adjacent Form. In: Zhang, K., Zheng, Y. (eds.) ISC 2004. LNCS, vol. 3225, pp. 99–110. Springer, Heidelberg (2004)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2008 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Longa, P., Miri, A. (2008). New Composite Operations and Precomputation Scheme for Elliptic Curve Cryptosystems over Prime Fields. In: Cramer, R. (eds) Public Key Cryptography – PKC 2008. PKC 2008. Lecture Notes in Computer Science, vol 4939. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-78440-1_14
Download citation
DOI: https://doi.org/10.1007/978-3-540-78440-1_14
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-78439-5
Online ISBN: 978-3-540-78440-1
eBook Packages: Computer ScienceComputer Science (R0)