Abstract
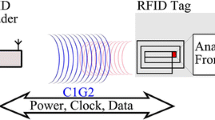
RFID applications do not always use encryption to ensure the security as public key cryptographic algorithms that are costly in term of computing resources. We proposed to secure the communication from an ISO 14443 RFID card to the reader against passive eavesdropping at the physical layer by adding noise. During the card reply, the reader generates an appropriate noise that is modulated by the load of the card. By knowing the noise it emitted, the reader is able to subtract it and to retrieve the card message when a spying probe in the field is inefficient.
Chapter PDF
Similar content being viewed by others
References
International Civil Aviation Organization (ICAO). Document 9303 Machine readable Travel Documents (MRTD). Part I: Machine readable Passports (2005)
Mastercard Paypass: http://www.paypass.com
Juels, A., Rivest, R.L., Szydlo, M.: Selective blocking of RFID tags for consumer privacy. In: 10th Annual ACM CCS 2003. ACM Press, New York (2003)
Finkenzeller, K.: RFID Handbook: Fundamentals and Applications in Contactless Smart Cards and Identification. John Wiley & Sons Ltd., Chichester (2003)
Garfinkel, S., Rosenberg, B.: RFID Applications, security, and privacy. Addison Wesley, Reading (2005)
Kfir, Z., Wool, A.: Picking virtual pockets using relay attacks on contactless smartcard systems. In: Proceedings IEE/CreateNet SecureComm, pp. 47–58 (2005)
Yoshida, J.: Tests reaveal e-passport security flaw, http://www.eetimes.com/showArticle.jhtml?articleID=45400010
Hancke, G.P.: Practical Attacks on Proximity Identification Systems (Short Paper), http://www.cl.cam.ac.uk/~gh275/SPPractical.pdf
ISO 14443 Identification cards - Contactless integrated circuit cards - Proximity cards
ISO 15693 Identification cards - Contactless integrated circuit cards - Vicinity cards
ISO 18000 RFID for item management
EPC Class-1 Generation 2 UHF RFID Conformance Requirements Specification
Zang, G., Lee, D., Cheung, R.: The Chinese University of Hong Kong, University of California, Imperial College London, Ziggurat-based hardware Gaussian random number generator (2004)
Dehmas, F., Crochon, E., Vacherand, F.: Patent WO 2006/035178 A1 (2004)
Castelluccia, C., Avoine, G.: Noisy Tags: A Pretty Good Key Exchange Protocol for RFID Tags. In: Proceedings of CARDIS 2006, pp. 289–299 (2006)
Haselsteiner, E., Breitfuss, K.: Security in near field communication. In: Workshop on RFID security (July 2006)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Savry, O., Pebay-Peyroula, F., Dehmas, F., Robert, G., Reverdy, J. (2007). RFID Noisy Reader How to Prevent from Eavesdropping on the Communication?. In: Paillier, P., Verbauwhede, I. (eds) Cryptographic Hardware and Embedded Systems - CHES 2007. CHES 2007. Lecture Notes in Computer Science, vol 4727. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-74735-2_23
Download citation
DOI: https://doi.org/10.1007/978-3-540-74735-2_23
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-74734-5
Online ISBN: 978-3-540-74735-2
eBook Packages: Computer ScienceComputer Science (R0)