Abstract
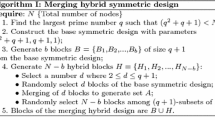
Wireless Sensor Networks (WSN) security is an important issue which has been investigated by researchers for few years. The most fundamental security problem in WSN is key management that covers the establishment, distribution, renewing and revocation of cryptographic keys. Several key management protocols were proposed in the literature. Unfortunately, most of them are not resilient to nodes capture. This means that an attacker compromising a node can reuse the node’s key materials to populate any part of the network with cloned nodes and new injected nodes. In this article, we present a simple polynomial-based key management protocol using a group-based deployment model without any necessary predictable deployment location of nodes. That solution achieves high resilience to nodes compromising compared with other protocols.
Chapter PDF
Similar content being viewed by others
References
Akyildiz, I.F., Su, W., Sankarasubramaniam, Y.: Wireless sensor networks: a survey. Computer Networks 38, 393–422 (2002)
Chan, H., Perrig, A., Song, D.: Random Key Predistibution Schemes for Sensor Networks. In: IEEE Symposium on Security and Privacy, Okland, California, USA, pp. 197–213 (2003)
Liu, D., Ning, P., Du, W.: Group-Based Key Pre-Distribution in Wireless Sensor Networks. In: Proc. of the 4th ACM workshop on Wireless security, Cologne, Germany, pp. 11–20 (2005)
Liu, F., Major Rivera, J.M., Cheng, X.: Location-aware Key Establishment in Wireless Sensor Networks. In: Proc. of the International Conf. on Wireless Communications and Mobile Computing, Vancouver, Canada, pp. 21–26 (2006)
Zhu, S., Setia, S., Jajodia, S.: LEAP: Efficient Security Mechanisms for Large Scale Distributed Sensor Networks. In: Proc. of the 10th ACM Conf. on Computer and Communications Security, Washington, DC, USA, pp. 62–72 (2003)
Bhuse, V., Gupta, A., Pidva, R.: A Distributed Approach to Security in Sensor-nets. In: IEEE Vehicular Technology Conference, pp. 3010–3014 (2003)
Yung, M., et al.: Perfectly-Secure Key Distribution for Dynamic Conferences. In: Brickell, E.F. (ed.) CRYPTO 1992. LNCS, vol. 740, pp. 471–486. Springer, Heidelberg (1993)
Yu, Z., Guan, Y.: A Robust Group-based Key Management Scheme for Wireless Sensor Networks. In: IEEE Wireless Communications and Networking Conference, New Orleans, USA, pp. 1915–1920 (2005)
Dutertre, B., Cheung, S., Levy, J.: Lightweight Key Management in Wireless Sensor Networks by Leveraging Initial Trust. SDL Technical Report SRI-SDL-04-02, SRI International (2004)
Perrig, A., et al.: Spins: Security protocols for sensor networks. In: Proc. of the 7th Annual ACM/IEEE International Conference on Mobile Computing and Networking, Rome, Italy, pp. 189–199 (2001)
Liu, D., Ning, P.: Establishing Pairwise Keys in Distributed Sensor Networks. In: Proc. of the 10th ACM Conference on Computer and Communication Security, Washington, DC, USA, pp. 52–61 (2003)
TmoteSky wireless sensor module, http://www.moteiv.com/products/docs/tmote-sky-datasheet.pdf
DH Key-Excchange Protocols. https://www.cs.tcd.ie/courses/baict/bass/4ict11/Coursework/4ICT11MT6.2.pdf
Karlof, C., Wagner, D.: Secure routing in wireless sensors networks: attacks and countermeasures. Elsevier’s AdHoc Networks Journal, Special Issue on Sensor Network Applications and Protocols (2003)
Dimitriou, T., Krontiris, I.: A Localized, Distributed Protocol for Secure Information Exchange in Sensor Networks. In: Proc. of the 19th IEEE International Parallel and Distributed Processing Symposium (2005)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 IFIP International Federation for Information Processing
About this paper
Cite this paper
Bekara, C., Laurent-Maknavicius, M. (2007). A New Resilient Key Management Protocol for Wireless Sensor Networks. In: Sauveron, D., Markantonakis, K., Bilas, A., Quisquater, JJ. (eds) Information Security Theory and Practices. Smart Cards, Mobile and Ubiquitous Computing Systems. WISTP 2007. Lecture Notes in Computer Science, vol 4462. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-72354-7_2
Download citation
DOI: https://doi.org/10.1007/978-3-540-72354-7_2
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-72353-0
Online ISBN: 978-3-540-72354-7
eBook Packages: Computer ScienceComputer Science (R0)