Abstract
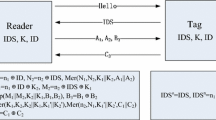
The increased functionality of EPC Class1 Gen2 (EPCGen2) is making this standard the de facto specification for inexpensive tags in the RFID industry. EPCGen2 supports only very basic security tools such as a 16-bit Pseudo-Random Number Generator and a 16-bit Cyclic Redundancy Code. Recently two EPCGen2 compliant protocols that address security issues were proposed in the literature. In this paper we analyze these protocols and show that they are not secure and subject to replay/impersonation and synchronization attacks. We then consider the general issue of supporting security in EPCGen2 compliant protocols and propose two RFID protocols that are secure within the restricted constraints of this standard, and an anonymous RFID mutual authentication protocol with forward secrecy that is compliant with the EPC Class2 Gen2 standard.
Chapter PDF
Similar content being viewed by others
References
Ateniese, G., Camenisch, J., de Medeiros, B.: Untraceable RFID tags via insubvertible encryption. In: Proc. ACM Conf. on Computer and Communication Security (ACM CCS 2005), pp. 92–101. ACM Press, New York (2005)
Avoine, G.: http://lasecwww.epfl.ch/~gavoine/rfid/
Avoine, G., Oechslin, P.: A scalable and provably secure hash based RFID protocol. In: Proc. IEEE International Workshop on Pervasive Computing and Communication Security (PerSec 2005). IEEE Computer Society Press, Los Alamitos (2005)
Burmester, M., de Medeiros, B., Motta, R.: Robust, Anonymous RFID Authentication with Constant Key-Lookup. In: Proc. ACM Symposium on Information, Computer and Communication Security (ASIACCS 2008), pp. 283–291. ACM Press, New York (2008)
Burmester, M., van Le, T., de Medeiros, B.: Provably secure ubiquitous systems: Universally composable RFID authentication protocols. In: Proceedings of the 2nd IEEE/CreateNet International Conference on Security and Privacy in Communication Networks (SECURECOMM 2006). IEEE Press, Los Alamitos (2006)
Canetti, R.: Studies in Secure Multiparty Computation and Application. PhD thesis, Weizmann Institute of Science, Rehovot 76100, Israel (June 1995)
Canetti, R.: Security and composition of multi-party cryptographic protocols. Journal of Cryptology 13(1), 143–202 (2000)
Canetti, R.: Universally composable security: A new paradigm for cryptographic protocols. In: Proc. IEEE Symp. on Foundations of Computer Science (FOCS 2001), pp. 136–145. IEEE Press, Los Alamitos (2001)
Chien, H.-Y., Chen, C.-H.: Mutual authentication protocol for rfid conforming to EPC class 1 generation 2 standards. Comput. Stand. Interfaces 29(2), 254–259 (2007)
Duc, D.N., Jaemin Park, H.L., Kim, K.: Enhancing Security of EPCglobal Gen-2 RFID Tag against Traceability and Cloning (2006), Symposium on Cryptography and Information Security, SCIS 2006 (2006)
Dimitriou, T.: A lightweight RFID protocol to protect against traceability and cloning attacks. In: Proc. IEEE Intern. Conf. on Security and Privacy in Communication Networks (SECURECOMM 2005). IEEE Press, Los Alamitos (2005)
Dimitriou, T.: A secure and efficient RFID protocol that can make big brother obsolete. In: Proc. Intern. Conf. on Pervasive Computing and Communications (PerCom 2006). IEEE Press, Los Alamitos (2006)
EPC Global. EPC Tag Data Standards, vs. 1.3. http://www.epcglobalinc.org/standards/EPCglobal_Tag_Data_Standard_TDS_Version_1.3.pdf
Goldreich, O., Goldwasser, S., Micali, S.: How to construct pseudorandom functions. Journal of the ACM 33(4) (1986)
Henrici, D., Müller, P.M.: Hash-based enhancement of location privacy for radio-frequency identification devices using varying identifiers. In: Proc. IEEE Intern. Conf. on Pervasive Computing and Communications, pp. 149–153 (2004)
ISO/IEC. Standard # 18000 – RFID Air Interface Standard, http://www.hightechaid.com/standards/18000.htm
Juels, A.: Minimalist cryptography for low-cost RFID tags. In: Blundo, C., Cimato, S. (eds.) SCN 2004. LNCS, vol. 3352, pp. 149–164. Springer, Heidelberg (2005)
Menezes, A., van Oorschot, P., Vanstone, S.: Handbook of Applied Cryptography. CRC Press, Boca Raton (1996)
Molnar, D., Soppera, A., Wagner, D.: A scalable, delegatable pseudonym protocol enabling ownership transfer of RFID tags. In: Preneel, B., Tavares, S. (eds.) SAC 2005. LNCS, vol. 3897, Springer, Heidelberg (2006)
Ohkubo, M., Suzuki, K., Kinoshita, S.: Cryptographic approach to “privacy-friendly” tags. In: Proc. RFID Privacy Workshop (2003)
Sharma, S.E., Weiss, S.A., Engels, D.W.: RFID systems and security and privacy implications. In: Kaliski Jr., B.S., Koç, Ç.K., Paar, C. (eds.) CHES 2002. LNCS, vol. 2523, pp. 454–469. Springer, Heidelberg (2003)
Stinson, D.: Cryptography Theory and Practice, 2nd edn. CRC Press, Inc., Boca Raton (2002)
Tsudik, G.: YA-TRAP: Yet another trivial RFID authentication protocol. In: Proc. IEEE Intern. Conf. on Pervasive Computing and Communications (PerCom 2006), IEEE Press, Los Alamitos (2006)
van Le, T., Burmester, M., de Medeiros, B.: Universally composable and forward-secure RFID authentication and authenticated key exchange. In: Proc. of the ACM Symp. on Information, Computer, and Communications Security (ASIACCS 2007), pp. 242–252. ACM Press, New York (2007)
Weis, S., Sarma, S., Rivest, R., Engels, D.: Security and privacy aspects of low-cost radio frequency identification systems. In: Hutter, D., Müller, G., Stephan, W., Ullmann, M. (eds.) Security in Pervasive Computing. LNCS, vol. 2802, pp. 454–469. Springer, Heidelberg (2004)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2008 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Burmester, M., de Medeiros, B. (2008). The Security of EPC Gen2 Compliant RFID Protocols. In: Bellovin, S.M., Gennaro, R., Keromytis, A., Yung, M. (eds) Applied Cryptography and Network Security. ACNS 2008. Lecture Notes in Computer Science, vol 5037. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-68914-0_30
Download citation
DOI: https://doi.org/10.1007/978-3-540-68914-0_30
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-68913-3
Online ISBN: 978-3-540-68914-0
eBook Packages: Computer ScienceComputer Science (R0)