Abstract
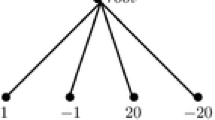
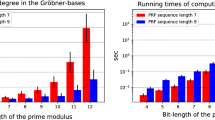
This paper investigates some modular powering functions suitable for cryptography. It is well known that the Rabin encryption function is a 4-to-1 mapping and breaking its one-wayness is secure under the factoring assumption. The previously reported encryption schemes using a powering function are variants of either the 4-to-1 mapping or higher n-to-1 mapping, where n>4. In this paper, we propose an optimized powering function that is a 3-to-1 mapping using a p 2 q-type modulus. The one-wayness of the proposed powering function is as hard as the infeasibility of the factoring problem. We present an efficient algorithm for computing the decryption for a p 2 q-type modulus, which requires neither modular inversion nor division. Moreover, we construct new provably secure digital signatures as an application of the optimized functions. In order to achieve provable security in the random oracle model, we usually randomize a message using random hashing or padding. However, we have to compute the randomization again if the randomized message is a non-cubic residue element — it is inefficient for long messages. We propose an algorithm that can deterministically find the unique cubic residue element for a randomly chosen element.
Chapter PDF
Similar content being viewed by others
References
Bellare, M., Rogaway, P.: Random Oracles are Practical: A Paradigm for Designing Efficient Protocols. In: Proceedings of the 1st ACM Conference on Computer and Communications Security, pp. 62–73. ACM Press, New York (1993), Available at: http://www.cs.ucdavis.edu/rogaway/papers/index.html
Bellare, M., Rogaway, P.: Optimal asymmetric encryption – How to encrypt with RSA. In: De Santis, A. (ed.) EUROCRYPT 1994. LNCS, vol. 950, pp. 92–111. Springer, Heidelberg (1995)
Bellare, M., Rogaway, P.: The exact security of digital signatures – How to sign with RSA and Rabin. In: Maurer, U.M. (ed.) EUROCRYPT 1996. LNCS, vol. 1070, pp. 399–416. Springer, Heidelberg (1996)
Boneh, D., Durfee, G., Howgrave-Graham, N.: Factoring N = prq for large r. In: Wiener, M. (ed.) CRYPTO 1999. LNCS, vol. 1666, pp. 326–337. Springer, Heidelberg (1999)
Boneh, D., Shacham, H.: Fast Variants of RSA. Cryptobytes 5(1), 1–9 (2002)
Coron, J.S.: Optimal security proofs for PSS and other signature schemes. In: Knudsen, L.R. (ed.) EUROCRYPT 2002. LNCS, vol. 2332, pp. 272–287. Springer, Heidelberg (2002)
HIME(R): High Performance Modular Squaring Based Public-Key Encryption (Revised Edition), Hitachi, Ltd. (2001)
Kurokawa, K., Ito, T., Takeuchi, M.: Public Key cryptosystem using a reciprocal number with the same intractability as factoring a large number. Cryptologia 12, 225–233 (1988)
Kurokawa, K., Ogata, W.: Efficient Rabin-type Digital Signature Scheme. Designs, Codes and Cryptography 16, 53–64 (1999)
Loxton, J.H., Khoo, D.S.P., Bird, G.J., Seberry, J.: A cubic RSA code equivalent to factorization. Journal of Cryptology 5, 139–150 (1992)
Montgomery, P.L.: Modular mutiplication without trial division. Math. Comp. 44, 519–521 (1985)
Pointcheval, D., Stern, J.: Security proofs for signature schemes. In: Maurer, U.M. (ed.) EUROCRYPT 1996. LNCS, vol. 1070, pp. 387–398. Springer, Heidelberg (1996)
Public-Key Cryptography Standards, PKCS # 1, Amendment 1: Multi-Prime RSA, RSA Laboratories
Rabin, M.O.: Digitalized signatures and public key cryptosystems as intractable as factorization, Technical Report, MIT/LCS/TR-212, MIT, Cambridge, MA (1979)
Rivest, R.L., Shamir, A., Adleman, L.: A method for obtaining digital signatures and public-key cryptosystems. Communications of the ACM 21(2), 120–126 (1978)
Scheidler, R.: A Public-Key Cryptosystem Using Purely Cubic Fields. J. Cryptology 11, 109–124 (1998)
Shoup, V.: A Proposal for an ISO Standard for Public Key Encryption (v. 2.1), ISO/IEC JTC1/SC27, N2563 (2001), Available at: http://www.shoup.net/papers/ or http://www.eprint.iacr.org/
Takagi, T.: Fast RSA-type cryptosystem modulo pkq. In: Krawczyk, H. (ed.) CRYPTO 1998. LNCS, vol. 1462, pp. 318–326. Springer, Heidelberg (1998)
Williams, H.C.: A modification of the RSA public key encryption procedure. IEEE Trans. on Information Theory IT-26(6), 726–729 (1980)
Williams, H.C.: Some public-key crypto-functions as intractable as factorization. Cryptologia 9(3), 223–237 (1985)
Williams, H.C.: An M3 public-key encryption scheme. In: Williams, H.C. (ed.) CRYPTO 1985. LNCS, vol. 218, pp. 358–368. Springer, Heidelberg (1986)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2003 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Sato, H., Takagi, T., Tezuka, S., Takaragi, K. (2003). Generalized Powering Functions and Their Application to Digital Signatures. In: Laih, CS. (eds) Advances in Cryptology - ASIACRYPT 2003. ASIACRYPT 2003. Lecture Notes in Computer Science, vol 2894. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-40061-5_28
Download citation
DOI: https://doi.org/10.1007/978-3-540-40061-5_28
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-20592-0
Online ISBN: 978-3-540-40061-5
eBook Packages: Springer Book Archive