Abstract
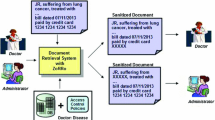
We present and analyze portable access control mechanisms for large data repositories, in that the customized access policies are stored on a portable device (e.g., a smart card). While there are significant privacy-preservation advantages to the use of smart cards anonymously created and bought in public places (stores, libraries, etc), a major difficulty is that, for huge data repositories and limited-capacity portable storage devices, it is not possible to represent any possible access configuration on the card. For a customer whose card is supposed to contain a subset S of documents, access to all of S must be allowed. In some situations a small enough number of ”false positives” (which are accesses to non-S documents) is acceptable to the server, and the challenge then is to minimize the number of false positives implicit to any given card. We describe and analyze schemes for both unstructured and structured collections of documents. For these schemes, we give fast algorithms for efficiently using the limited space available on the card. In our model the customer does not know which documents correspond to false positives, the probability of a randomly chosen document being a false positive is small, and information about false positives bound to one card is useless for any other card even if both of them permit access to the same set of documents S.
Portions of this work were supported by Grants IIS-0325345, IIS-0219560, IIS-0312357, and IIS-0242421 from the National Science Foundation, Contract N00014-02-1-0364 from the Office of Naval Research, by sponsors of the Center for Education and Research in Information Assurance and Security, and by Purdue Discovery Park’s e-enterprise Center.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Atallah, M., Bykova, M.: Portable and Flexible Document Access Control Mechanisms. CERIAS Technical Report TR 2004–24, Purdue University (June 2004)
Atallah, M., Frikken, K., Black, C., Overstreet, S., Bhatia, P.: Digital Rights Management. In: Singh, M. (ed.) Practical Handbook of Internet Computing, CRC Press, Boca Raton (2004)
Atallah, M., Li, J.: Enhanced Smart-card based License Management. In: IEEE International Conference on E-Commerce (CEC), June 2003, pp. 111–119 (2003)
Aura, T., Gollmann, D.: Software license management with smart cards. In: USENIX Workshop on Smart Card Technology, USENIX Association (May 1999)
Bertino, E., Carminati, B., Ferrari, E., Thuraisingham, B., Gupta, A.: Selective and Authentic Third-party Distribution of XML Documents. In: Working Paper, Sloan School of Management, MIT, Cambridge (2002), http://papers.ssrn.com/sol3/papers.cfm?abstractid=299935
Bertino, E., Castano, S., Ferrari, E.: On Specifying Security Policies for Web Documents with an XML-based Language. In: ACM Symposium on Access Control Models and Technologies (SACMAT 2001) (May 2001)
Bertino, E., Castano, S., Ferrari, E.: Securing XML Documents with Author- X. IEEE Internet Computing 5(3), 21–31 (2001)
Bertino, E., Ferrari, E.: Secure and Selective Dissemination of XML Documents. ACM Transactions on Information and System Security 5(3), 290–331 (2002)
Bloom, B.: Space/time trade-offs in hash coding with allowable errors. Communications of the ACM 13(7), 422–426 (1970)
Broder, A., Mitzenmacher, M.: Network Applications of Bloom Filters: A Survey. In: Allerton Conference (2002)
Bykova, M., Atallah, M.: Succinct Specifications of Portable Document Access Policies. In: ACM Symposium on Access Control Models and Technologies (SACMAT 2004) (June 2004)
Chaum, D.: Untraceable Electronic Mail, Return Addresses, and Digital Pseudonyms. Communications of the ACM 24(2), 84–88 (1981)
Damiani, D., De Capitani Di Vimercati, S., Paraboschi, S., Samarati, P.: A Fine-Grained Access Control System for XML Documents. ACM Transactions on Information and System Security 5(2), 169–202 (2002)
Devanbu, P., Gertz, M., Kwong, A., Martel, C., Nuckolls, G.: Flexible Authentication of XML Documents. In: ACM Conference on Computer and Communications Security (CCS 2001) (November 2001)
Fan, L., Cao, P., Almeida, J., Broder, A.: Summary Cache: A Scalable Wide- AreaWeb Cache Sharing Protocol. IEEE/ACM Transactions on Networking 8(3), 281–293 (2000)
Kim, J., Choi, S., Kim, K., Boyd, C.: Anonymous Authentication Protocol for Dynamic Groups with Power-Limited Devices. In: Symposium on Cryptography and Information Security (SCIS 2003), January 2003, vol. 1/2, pp. 405–410 (2003)
Lee, C., Deng, X., Zhu, H.: Design and Security Analysis of Anonymous Group Identification Protocols. In: Naccache, D., Paillier, P. (eds.) PKC 2002. LNCS, vol. 2274, pp. 188–198. Springer, Heidelberg (2002)
Mitzenmacher, M.: Compressed Bloom Filters. In: ACM symposium on Principles of Distributed Computing (August 2001)
Payette, S., Lagoze, C.: Policy-Carrying, Policy-Enforcing Digital Objects. In: Borbinha, J.L., Baker, T. (eds.) ECDL 2000. LNCS, vol. 1923, pp. 144–157. Springer, Heidelberg (2000)
Persiano, P., Visconti, I.: A Secure and Private System for Subscription-Based Remote Services. ACM Transactions on Information and System Security 6(4), 472–500 (2003)
Schechter, S., Parnell, T., Hartemink, A.: Anonymous Authentication of Membership in Dynamic Groups. In: Franklin, M.K. (ed.) FC 1999. LNCS, vol. 1648, pp. 184–195. Springer, Heidelberg (1999)
Stubblebine, S., Syverson, P., Goldschlag, D.: Unlinkable Serial Transactions. ACM Transactions on Information and System Security 2(4), 354–389 (1999)
World Wide Web Consortium. Extensible Markup Language (XML) 1.0 (second edition), W3C Recommendation (October 2000), http://www.w3.org/TR/REC-xml
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2004 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Atallah, M., Bykova, M. (2004). Portable and Flexible Document Access Control Mechanisms. In: Samarati, P., Ryan, P., Gollmann, D., Molva, R. (eds) Computer Security – ESORICS 2004. ESORICS 2004. Lecture Notes in Computer Science, vol 3193. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-30108-0_12
Download citation
DOI: https://doi.org/10.1007/978-3-540-30108-0_12
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-22987-2
Online ISBN: 978-3-540-30108-0
eBook Packages: Springer Book Archive