Abstract
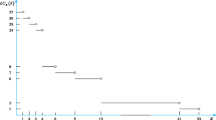
The edit distance correlation attack on the well-known alternating step generator for stream cipher applications was proposed by Golić and Menicocci. The attack can be successful only if the probability of the zero edit distance, the so-called embedding probability, conditioned on a given segment of the output sequence, decreases with the segment length, and if the decrease is exponential, then the required segment length is linear in the total length of the two linear feedback shift registers involved. The exponential decrease for the maximal value of the embedding probability as a function of the given output segment was estimated experimentally by Golić and Menicocci. In this paper, by using the connection with the interleaving and decimation operations, the embedding probability is theoretically analyzed. Tight exponentially small upper bounds on the maximal embedding probability are thus derived. Sharp exponentially small lower and upper bounds on the minimal embedding probability are also determined.
Chapter PDF
Similar content being viewed by others
References
Golić, J.D., Mihaljević, M.: A generalized correlation attack on a class of stream ciphers based on the Levenshtein distance. Journal of Cryptology 3(3), 201–212 (1991)
Golić, J.D., Petrović, S.: A generalized correlation attack with a probabilistic constrained edit distance. In: Rueppel, R.A. (ed.) EUROCRYPT 1992. LNCS, vol. 658, pp. 472–476. Springer, Heidelberg (1993)
Golić, J.D., O’Connor, L.: Embedding and probabilistic correlation attacks on clock-controlled shift registers. In: De Santis, A. (ed.) EUROCRYPT 1994. LNCS, vol. 950, pp. 230–243. Springer, Heidelberg (1995)
Golić, J.D., Menicocci, R.: Edit distance correlation attack on the alternating step generator. In: Kaliski Jr., B.S. (ed.) CRYPTO 1997. LNCS, vol. 1294, pp. 499–512. Springer, Heidelberg (1997)
Golić, J.D., Menicocci, R.: Edit probability correlation attack on the alternating step generator. In: Ding, C., Helleseth, T., Niederreiter, H. (eds.) Sequences and their Applications - SETA 1998. Discrete Mathematics and Theoretical Computer Science, pp. 213–227. Springer, Heidelberg (1999)
Günther, C.G.: Alternating step generators controlled by de Bruijn sequences. In: Price, W.L., Chaum, D. (eds.) EUROCRYPT 1987. LNCS, vol. 304, pp. 5–14. Springer, Heidelberg (1988)
Jiang, S., Gong, G.: On edit distance attack to alternating step generator (unpublished manuscript)
Johansson, T.: Reduced complexity correlation attacks on two clock-controlled generators. In: Ohta, K., Pei, D. (eds.) ASIACRYPT 1998. LNCS, vol. 1514, pp. 342–357. Springer, Heidelberg (1998)
Živković, M.: An algorithm for the initial state reconstruction of the clock-controlled shift register. IEEE Trans. Information Theory 37, 1488–1490 (1991)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2004 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Golić, J.D. (2004). On the Success of the Embedding Attack on the Alternating Step Generator. In: Matsui, M., Zuccherato, R.J. (eds) Selected Areas in Cryptography. SAC 2003. Lecture Notes in Computer Science, vol 3006. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-24654-1_19
Download citation
DOI: https://doi.org/10.1007/978-3-540-24654-1_19
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-21370-3
Online ISBN: 978-3-540-24654-1
eBook Packages: Springer Book Archive