Abstract
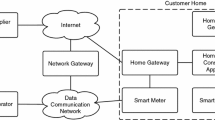
Security has been a growing concern for most large organizations, especially financial and government institutions, as security breaches in the socio-technical systems they depend on are costing billions. A major reason for these breaches is that socio-technical systems are designed in a piecemeal rather than a holistic fashion that leaves parts of a system vulnerable. To tackle this problem, we propose a three-layer security analysis framework for socio-technical systems involving business processes, applications and physical infrastructure. In our proposal, global security requirements lead to local security requirements that cut across layers and upper-layer security analysis influences analysis at lower layers. Moreover, we propose a set of analytical methods and a systematic process that together drive security requirements analysis throughout the three-layer framework. Our proposal supports analysts who are not security experts by defining transformation rules that guide the corresponding analysis. We use a smart grid example to illustrate our approach.
Chapter PDF
Similar content being viewed by others
References
Carpenter, M., Goodspeed, T., Singletary, B., Skoudis, E., Wright, J.: Advanced metering infrastructure attack methodology. InGuardians White Paper (2009)
Chung, L.: Dealing with security requirements during the development of information systems. In: Rolland, C., Cauvet, C., Bodart, F. (eds.) CAiSE 1993. LNCS, vol. 685, pp. 234–251. Springer, Heidelberg (1993)
Chung, L., Supakkul, S.: Representing nfrs and frs: A goal-oriented and use case driven approach. In: Dosch, W., Lee, R.Y., Wu, C. (eds.) SERA 2004. LNCS, vol. 3647, pp. 29–41. Springer, Heidelberg (2006)
Firesmith, D.: Specifying reusable security requirements. Journal of Object Technology 3(1), 61–75 (2004)
Flick, T., Morehouse, J.: Securing the smart grid: next generation power grid security. Elsevier (2010)
Giorgini, P., Massacci, F., Zannone, N.: Security and trust requirements engineering. In: Aldini, A., Gorrieri, R., Martinelli, F. (eds.) FOSAD 2005. LNCS, vol. 3655, pp. 237–272. Springer, Heidelberg (2005)
Gross, D., Yu, E.: From non-functional requirements to design through patterns. Requirements Engineering 6(1), 18–36 (2001)
Hafiz, M., Adamczyk, P., Johnson, R.E.: Organizing security patterns. IEEE Software 24(4), 52–60 (2007)
Herrmann, P., Herrmann, G.: Security requirement analysis of business processes. Electronic Commerce Research 6(3-4), 305–335 (2006)
Jureta, I., Borgida, A., Ernst, N., Mylopoulos, J.: Techne: Towards a new generation of requirements modeling languages with goals, preferences, and inconsistency handling. In: Proc. of RE 2010, pp. 115–124 (2010)
Liu, L., Yu, E., Mylopoulos, J.: Security and privacy requirements analysis within a social setting. In: Proc. of RE 2003, Monterey, California, pp. 151–161 (2003)
Menzel, M., Thomas, I., Meinel, C.: Security requirements specification in service-oriented business process management. In: Proceedings of International Conference on Availability, Reliability and Security, ARES 2009, pp. 41–48. IEEE (2009)
Mouratidis, H., Giorgini, P.: A natural extension of tropos methodology for modelling security. In: Proc. of the Agent Oriented Methodologies Workshop (OOPSLA 2002). Citeseer, Seattle (2002)
Mouratidis, H., Jurjens, J.: From goal-driven security requirements engineering to secure design. International Journal of Intelligent System 25(8), 813–840 (2010)
Rodríguez, A., Fernández-Medina, E., Trujillo, J., Piattini, M.: Secure business process model specification through a uml 2.0 activity diagram profile. Decision Support Systems 51(3), 446–465 (2011)
de Rodríguez, G.I.G.R., Fernández-Medina, E., Piattini, M.: Semi-formal transformation of secure business processes into analysis class and use case models: An mda approach. Information and Software Technology 52(9), 945–971 (2010)
Scandariato, R., Yskout, K., Heyman, T., Joosen, W.: Architecting software with security patterns. Tech. rep., KU Leuven (2008)
Schneier, B.: Attack trees. Dr. Dobb’s Journal 24(12), 21–29 (1999)
Schumacher, M., Fernandez-Buglioni, E., Hybertson, D., Buschmann, F., Sommerlad, P.: Security Patterns: Integrating security and systems engineering. John Wiley & Sons (2013)
Sindre, G., Opdahl, A.L.: Eliciting security requirements with misuse cases. Requirements Engineering 10(1), 34–44 (2005)
Van Lamsweerde, A., Letier, E.: Handling obstacles in goal-oriented requirements engineering. IEEE Transactions on Software Engineering 26(10), 978–1005 (2000)
Yu, E.: Towards modelling and reasoning support for early-phase requirements Engineering, pp. 226–235. IEEE Computer Soc. Press (1997)
Zave, P., Jackson, M.: Four dark corners of requirements engineering. ACM Trans. Softw. Eng. Methodol. 6(1), 1–30 (1997)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Li, T., Horkoff, J. (2014). Dealing with Security Requirements for Socio-Technical Systems: A Holistic Approach. In: Jarke, M., et al. Advanced Information Systems Engineering. CAiSE 2014. Lecture Notes in Computer Science, vol 8484. Springer, Cham. https://doi.org/10.1007/978-3-319-07881-6_20
Download citation
DOI: https://doi.org/10.1007/978-3-319-07881-6_20
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-07880-9
Online ISBN: 978-3-319-07881-6
eBook Packages: Computer ScienceComputer Science (R0)