Abstract
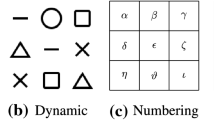
One of the most popular contemporary graphical password approaches is the Pattern-Lock authentication mechanism that comes integrated with the Android mobile operating system. In this paper we investigate the impact of password strength meters on the selection of a perceivably secure pattern. We first define a suitable metric to measure pattern strength, taking into account the constraints imposed by the Pattern-Lock mechanism’s design. We then implement an app via which we conduct a survey for Android users, retaining demographic information of responders and their perceptions on what constitutes a pattern complex enough to be secure. Subsequently, we display a pattern strength meter to the participant and investigate whether this additional prompt influences the user to change their pattern to a more effective and complex one. We also investigate potential correlations between our findings and results of a previous pilot study in order to detect any significant biases on setting a Pattern-Lock.
Chapter PDF
Similar content being viewed by others
References
Andriotis, P., Tryfonas, T., Oikonomou, G., Yildiz, C.: A pilot study on the security of pattern screen-lock methods and soft side channel attacks. In: 6th ACM Conference on Security and Privacy in Wireless and Mobile Networks, WiSec 2013, pp. 1–6. ACM (2013)
Askoxylakis, I.G., Kastanis, D.D., Traganitis, A.: Elliptic curve and password based dynamic key agreement in wireless ad-hoc networks. In: Communication, Network, and Information Security, pp. 50–60 (2006)
Aviv, A.J., Gibson, K., Mossop, E., Blaze, M., Smith, J.M.: Smudge attacks on smartphone touch screens. In: 4th USENIX Conference on Offensive Technologies, pp. 1–7. USENIX Association (2010)
Biddle, R., Chiasson, S., Van Oorschot, P.C.: Graphical passwords: Learning from the first twelve years. ACM Computing Surveys 44(4), 1–41 (2012)
Bonneau, J.: The science of guessing: analyzing an anonymized corpus of 70 million passwords. In: 2012 IEEE Symposium Security and Privacy (SP), pp. 538–552. IEEE (2012)
Brostoff, S., Sasse, A.: Are Passfaces More Usable Than Passwords? A Field Trial Investigation. In: People and Computers XIV Usability or Else!. Springer, London (2000)
Davis, D., Monrose, F., Reiter, M.: On user choice in graphical password schemes. In: USENIX Assosiation Proceedings of the 13th USENIX Security Symposium, pp. 151–163. USENIX Association (2004)
Jermyn, I., Mayer, A., Monrose, F., Reiter, M.K., Rubin, A.D.: The Design and Analysis of Graphical Passwords. In: 8th USENIX Security Symposium, pp. 1–14 (1999)
Passfaces Corporation.: The Science Behind Passfaces. White paper, http://www.passfaces.com/enterprise/resources/white_papers.htm
Solar Designer. John the Ripper, http://www.openwall.com/john/
van Oorschot, P.C., Thorpe, J.: Exploiting Predictability in Click-based Graphical Passwords. Journal of Computer Security 19(4), 669–702 (2011)
van Oorschot, P.C., Thorpe, J.: On predictive models and user-drawn graphical passwords. ACM Trans. Inf. Syst. Secur. 10(4), 5:1–5:33 (2008)
Sasse, M.A., Brostoff, S., Weirich, D.: Transforming the ‘weakest link’ - a human/computer interaction approach to usable and effective security. BT Technology Journal 19(3), 122–131 (2001)
Standing, L., Conezio, J., Haber, R.N.: Perception and Memory for Pictures: Single-trial Learning of 2500 Visual Stimuli. Psychonomic Science 19(2), 73–74 (1970)
Tao, H., Adams, C.: Pass-Go: A Proposal to Improve the Usability of Graphical Passwords. International Journal of Network Security 7(2), 273–292 (2008)
Thorpe, J., van Oorschot, P.C.: Human-seeded attacks and exploiting hot-spots in graphical passwords. In: USENIX Assosiation Proceedings of the 16th USENIX Security Symposium, pp. 103–118. USENIX Association (2007)
Uellenbeck, S., Dürmuth, M., Wolf, C., Holz, T.: Quantifying the security of graphical passwords: the case of android unlock patterns. In: 2013 ACM SIGSAC Conference on Computer & Communications Security, pp. 161–172. ACM (2013)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Andriotis, P., Tryfonas, T., Oikonomou, G. (2014). Complexity Metrics and User Strength Perceptions of the Pattern-Lock Graphical Authentication Method. In: Tryfonas, T., Askoxylakis, I. (eds) Human Aspects of Information Security, Privacy, and Trust. HAS 2014. Lecture Notes in Computer Science, vol 8533. Springer, Cham. https://doi.org/10.1007/978-3-319-07620-1_11
Download citation
DOI: https://doi.org/10.1007/978-3-319-07620-1_11
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-07619-5
Online ISBN: 978-3-319-07620-1
eBook Packages: Computer ScienceComputer Science (R0)