Abstract
Relationships databases have enjoyed a certain boom in software worlds until now. These days, with the rise of modern applications, unstructured data production, traditional databases do not completely meet the needs of all systems. Regarding these issues, NOSQL databases have been developed and are a good alternative. But security aspects stay behind. Injection attacks are the most serious class of web attacks that are not taken seriously in NoSQL.
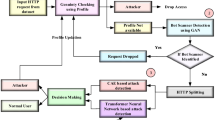
This paper presents a Neural Network model approach for NoSQL injection. This method attempts to use the best and most effective features to identify an injection. The features used are divided into two categories, the first one based on the content of the request, and the second one independent of the request meta parameters. In order to detect attack payloads features, we work on character level analysis to obtain malicious rate of user inputs. The results demonstrate that our model has detected more attack payloads compare with models that work black list approach in keyword level.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Xu, Y., Li, W., Wang, D.: Web security attack and defense Guide to infiltration testing. Publishing House of Electronics Industry (2018)
Japkowicz, N., Stephen, S.: The class imbalance problem: a systematic study. Intell. Data Anal. 6(5), 429–449 (2002)
Liu, G., Yi, Z., Yang, S.: A hierarchical intrusion detection model based on the pca neural networks. Neurocomputing 70(7), 1561–1568 (2007)
Sahasrabuddhe, A., et al.: Survey on intrusion detection system using data mining techniques. Int. Res. J. Eng. Technol. 4(5), 1780–1784 (2017)
Dali, L., et al.: A survey of intrusion detection system. In: 2nd World Symposium on Web Applications and Networking (WSWAN), pp. 1–6. IEEE, Piscataway (2015)
Batista, L.O., de Silva, G.A., Araújo, V.S., Araújo, V.J.S., Rezende, T.S., Guimarães, A.J., de Campos Souza, P.V.: Fuzzy neural networks to create an expert system for detecting attacks by SQL Injection. IJoFCS 1, 8–21 (2018)
Liu, H., Bo, L.: Machine learning and deep learning methods for intrusion detection systems: a survey. Appl. Sci. 9, 4396 (2019)
Othman, S.M., Ba-Alwi, F.M., Alsohybe, N.T., Al-Hashida, A.Y.: Intrusion detection model using machine learning algorithm on big data environment. J. Big Data 5, 34 (2018)
Karatas, F.: Sevcan Aytaç Korkmaz. Controlling Fraud by Using Machine Learning Libraries on Spark. Applied Mathematics, Electronics and Computers, IJAMEC (2018)
Owen, S., Anil, R., Dunning, T., Friedman, E.: Mahout in action: Manning Shelter Island (2011)
Zhang, J., Jou, Y.-T., Li, X.: Cross-Site Scripting (XSS) Detection Integrating Evidences in Multiple Stages, 08 Jan 2019
Uwagbole, S.O., Buchanan, W.J., Lu, F.: Applied machine learning predictive analytics to SQL injection attack detection and prevention. IFIP/IEEE IM (2017)
Teixido, M., Palleja, T., Tresanchez, M., Font, D., Moreno, J., Fernández, A., Palacín, J., Rebate, C.: Optimization of the virtual mouse HeadMouse to foster its classroom use by children with physical disabilities. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 2(4) (2013). ISSN 2255–2863
Li, T., Sun, S., Corchado, J.M., Siyau, M.F.: A particle dyeing approach for track continuity for the SMC-PHD filter. In: 17th International Conference on Information Fusion (FUSION), pp. 1–8. IEEE, July 2014
Costa, A., Heras, S., Palanca, J., Novais, P., Julián, V.: Persuasion and recommendation system applied to a cognitive assistant. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(2) (2016). ISSN 2255–2863
Fdez-Riverola, F., Iglesias, E.L., Díaz, F., Méndez, J.R., Corchado, J.M.: Applying lazy learning algorithms to tackle concept drift in spam filtering. Expert Syst. Appl. 33(1), 36–48 (2007)
Keyhanipour, A.H., Moshiri, B.: Designing a web spam classifier based on feature fusion in the layered multi-population genetic programming framework. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 2(3) (2013). ISSN 2255-2863
Ameller, M.A., González, M.A.: Minutiae filtering using ridge-valley method. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(1) (2016). ISSN 2255-2863
Morente-Molinera, J.A., Kou, G., González-Crespo, R., Corchado, J.M., Herrera-Viedma, E.: Solving multi-criteria group decision making problems under environments with a high number of alternatives using fuzzy ontologies and multi-granular linguistic modelling methods. Knowl.-Based Syst. 137, 54–64 (2017)
Li, T., Sun, S., Bolić, M., Corchado, J.M.: Algorithm design for parallel implementation of the SMC-PHD filter. Sig. Process. 119, 115–127 (2016)
Coria, J.A.G., Castellanos-Garzón, J.A., Corchado, J.M.: Intelligent business processes composition based on multi-agent systems. Expert Syst. Appl. 41(4), 1189–1205 (2014)
Adriana, F.-F., Cristina, C.-P., Leonardo, O.-A.: Energy-aware routing in multiple domains software-defined networks. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(3) (2016). ISSN 2255-2863
Khayati, N., Wided, L.-C.: A distributed and collaborative intelligent system for medical diagnosis. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 2(2) (2013). ISSN 2255-2863
Tapia, D.I., Fraile, J.A., Rodríguez, S., Alonso, R.S., Corchado, J.M.: Integrating hardware agents into an enhanced multi-agent architecture for Ambient Intelligence systems. Inf. Sci. 222, 47–65 (2013)
Corchado, J.M., Pavón, J., Corchado, E.S., Castillo, L.F.: Development of CBR-BDI agents: a tourist guide application. In: European Conference on Case-based Reasoning, pp. 547–559. Springer, Heidelberg (2004)
Lima, A.C.E., de Castro, L.N., Corchado, J.M.: A polarity analysis framework for Twitter messages. Appl. Math. Comput. 270, 756–767 (2015)
Fdez-Riverola, F., Corchado, J.M.: FSfRT: forecasting system for red tides. Appl. Intell. 21(3), 251–264 (2004)
Fdez-Riverola, F., Iglesias, E.L., Díaz, F., Méndez, J.R., Corchado, J.M.: SpamHunting: an instance-based reasoning system for spam labelling and filtering. Decis. Support Syst. 43(3), 722–736 (2007)
Casado-Vara, R., Martin-del Rey, A., Affes, S., Prieto, J., Corchado, J.M.: IoT network slicing on virtual layers of homogeneous data for improved algorithm operation in smart buildings. Future Gen. Comput. Syst. 102, 965–977 (2020)
Baruque, B., Corchado, E., Mata, A., Corchado, J.M.: A forecasting solution to the oil spill problem based on a hybrid intelligent system. Inf. Sci. 180(10), 2029–2043 (2010)
Rodrigues, M., Gonçalves, S., Fdez-Riverola, F.: E-learning platforms and e-learning students: building the bridge to success. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 1(2) (2012). ISSN 2255-2863
Casado-Vara, R., Prieto, J., De la Prieta, F., Corchado, J.M.: How blockchain improves the supply chain: case study alimentary supply chain. Procedia Comput. Sci. 134, 393–398 (2018)
Corchado, J.M., Aiken, J.: Hybrid artificial intelligence methods in oceanographic forecast models. IEEE Trans. Syst. Man Cybern. Part C (Appl. Rev.) 32(4), 307–313 (2002)
González-Briones, A., Prieto, J., De La Prieta, F., Herrera-Viedma, E., Corchado, J.M.: Energy optimization using a case-based reasoning strategy. Sensors 18(3), 865 (2018)
Díaz, F., Fdez-Riverola, F., Corchado, J.M.: gene-CBR: a case-based reasoning tool for cancer diagnosis using microarray data sets. Comput. Intell. 22(3–4), 254–268 (2006)
Corchado, J.M., Corchado, E.S., Aiken, J., Fyfe, C., Fernandez, F., Gonzalez, M.: Maximum likelihood hebbian learning based retrieval method for CBR systems. In: International Conference on Case-Based Reasoning, pp. 107–121. Springer, Berlin (2003)
Castro, J., Marti-Puig, P.: Real-time identification of respiratory movements through a microphone. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 3(3) (2014). ISSN 2255-2863
Mokom, F., Kobti, Z.: Interventions via social influence for emergent suboptimal restraint use. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 2(2) (2013). ISSN 2255-2863
Guillén, J.H., del Rey, A.M., Casado-Vara, R.: Security countermeasures of a SCIRAS model for advanced malware propagation. IEEE Access 7, 135472–135478 (2019)
Corchado, J.M., Lees, B.: A hybrid case-based model for forecasting. Appl. Artif. Intell. 15(2), 105–127 (2001)
Fernández-Riverola, F., Diaz, F., Corchado, J.M.: Reducing the memory size of a fuzzy case-based reasoning system applying rough set techniques. IEEE Trans. Syst. Man Cybern. Part C (Appl. Rev.) 37(1), 138–146 (2006)
Tapia, D.I., Corchado, J.M.: An ambient intelligence based multi-agent system for alzheimer health care. Int. J. Ambient Comput. Intell. (IJACI) 1(1), 15–26 (2009)
Corchado, J.M., Fyfe, C.: Unsupervised neural method for temperature forecasting. Artif. Intell. Eng. 13(4), 351–357 (1999)
Mendez, J.R., Fdez-Riverola, F., Diaz, F., Iglesias, E.L., Corchado, J.M.: A comparative performance study of feature selection methods for the anti-spam filtering domain. In: Industrial Conference on Data Mining, pp. 106–120. Springer, Berlin (2006)
Koskimaki, H., Siirtola, P.: Accelerometer vs. electromyogram in activity recognition. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(3) (2016). ISSN 2255-2863
Goyal, S., Goyal, G.K.: Machine learning ANN models for predicting sensory quality of roasted coffee flavoured sterilized drink. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 2(3) (2013). ISSN 2255-2863
Jiménez-Rodríguez, A., Fernando Castillo, L., González, M.: Studying the mechanisms of the Somatic Marker Hypothesis in Spiking Neural Networks (SNN). ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 1(2) (2012). ISSN 2255-2863
Fähndrich, J., Ahrndt, S., Albayrak, S.: Formal language decomposition into semantic primes. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 3(1) (2014). ISSN 2255-2863
Griol, D., Molina, J.M.: A proposal to manage multi-task dialogs in conversational interfaces. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(2) (2016). ISSN 2255-2863
Santos, A., Nogueira, R., Lourenço, A.: Applying a text mining framework to the extraction of numerical parameters from scientific literature in the biotechnology domain. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 1(1) (2012). ISSN 2255-2863
Mata, A., Corchado, J.M.: Forecasting the probability of finding oil slicks using a CBR system. Expert Syst. Appl. 36(4), 8239–8246 (2009)
Chamoso, P., González-Briones, A., Rodríguez, S., Corchado, J.M.: Tendencies of technologies and platforms in smart cities: a state-of-the-art review. Wirel. Commun. Mob. Comput. (2018)
Glez-Bedia, M., Corchado, J.M., Corchado, E.S., Fyfe, C.: Analytical model for constructing deliberative agents. Eng. Intell. Syst. Electr. Eng. Commun. 10(3), 173–185 (2002)
Beliz, N., Rangel, J.C., Hong, C.S.: Detecting DoS attack in web services by using an adaptive multiagent solution. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 1(2) (2012). ISSN 2255-2863
Fyfe, C., Corchado, J.M.: Automating the construction of CBR systems using kernel methods. Int. J. Intell. Syst. 16(4), 571–586 (2001)
Choon, Y.W., Mohamad, M.S., Safaai Deris, R.M., Illias, C.K.C., Chai, L.E., Omatu, S., Corchado, J.M.: Differential bees flux balance analysis with OptKnock for in silico microbial strains optimization. PloS One 9(7) (2014)
Martín del Rey, A., Casado Vara, R., Hernández Serrano, D.: Reversibility of symmetric linear cellular automata with radius r = 3. Mathematics 7(9), 816 (2019)
Casado-Vara, R., Novais, P., Gil, A.B., Prieto, J., Corchado, J.M.: Distributed continuous-time fault estimation control for multiple devices in IoT networks. IEEE Access 7, 11972–11984 (2019)
Loukanova, R.: Relationships between specified and underspecified quantification by the theory of acyclic recursion. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(4) (2016). ISSN 2255-2863
Matos, S., Araújo, H., Luís Oliveira, J.: Biomedical literature exploration through latent semantics. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 2(2) (2013). ISSN 2255-2863
Casado-Vara, R., Chamoso, P., De la Prieta, F., Prieto, J., Corchado, J.M.: Non-linear adaptive closed-loop control system for improved efficiency in IoT-blockchain management. Inf. Fusion 49, 227–239 (2019)
Monino, J.L., Sedkaoui, S.: The algorithm of the snail: an example to grasp the window of opportunity to boost big data. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(3) (2016). ISSN 2255-2863
Griol, D., Molina, J.M.: From VoiceXML to multimodal mobile Apps: development of practical conversational interfaces. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(3) (2016). ISSN 2255-2863
Mouysset, S., Guivarch, R., Noailles, J., Ruiz, D.: Segmentation of cDNA microarray images using parallel spectral clustering. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 2(1) (2013). ISSN 2255-2863
Leong, Y.Y., Chong, C.K., Chai, L.E., Deris, S., Illias, R., Omatu, S., Mohamad, M.S.: Simulation of fermentation pathway using bees algorithm. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 1(2) (2012). ISSN 2255-2863
Pinto, A., Costa, R.: Hash-chain-based authentication for IoT. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(4) (2016). ISSN 2255-2863
Efthymiou, V., Koutraki, M., Antoniou, G.: Real-time activity recognition and assistance in smart classrooms. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 1(1) (2012). ISSN 2255-2863
García-Valls, M.: Prototyping low-cost and flexible vehicle diagnostic systems. ADCAIJ: Adv. Distrib. Comput. Artif. Intell. J. 5(4) (2016). ISSN 2255-2863
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 The Editor(s) (if applicable) and The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Alizadehsani, Z. (2021). Proposing to Use Artificial Neural Networks for NoSQL Attack Detection. In: Rodríguez González, S., et al. Distributed Computing and Artificial Intelligence, Special Sessions, 17th International Conference. DCAI 2020. Advances in Intelligent Systems and Computing, vol 1242. Springer, Cham. https://doi.org/10.1007/978-3-030-53829-3_29
Download citation
DOI: https://doi.org/10.1007/978-3-030-53829-3_29
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-53828-6
Online ISBN: 978-3-030-53829-3
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)