Abstract
In this paper, we introduce a Prony-type data fitting problem consisting in interpolating the table \(\left\{ m, g(m)\right\} _{m=0}^M\) with \(g(0)\ne 0\) in the sense of least squares by exponential sums with equal weights. We further study how to choose the parameters of the sums properly to solve the problem. Moreover, we show that the sums have some advantages in data fitting over the classical Prony exponential sums. Namely, we prove that the parameters of our sums are a priori well-controlled and thus can be found via a stable numerical framework, in contrast to those of the Prony ones. In several numerical experiments, we also compare the behaviour of both the sums and illustrate the above-mentioned advantages.
The research was financially supported by Russian Science Foundation, Agreement 19-71-10078.
You have full access to this open access chapter, Download conference paper PDF
Similar content being viewed by others
Keywords
1 Introduction and Main Results
Interpolation (or data fitting) of a complex-valued function \(g=g(z)\), \(z\in \mathbb {C}\), by a linear combination of exponents, e.g. by the Prony exponential sums
appears in many contexts in Science and Engineering, in particular, in time series analysis, physical phenomena modelling and signal processing. There exist numerous state-of-the-art analytical and numerical methods for solving the corresponding data fitting problems, see the overview in [2, 5, 7, 9,10,11,12]. One of the main challenges in the area is that the exponential data fitting is ill-conditioned in many cases [10]. Among other things, this can be connected with the behaviour of exponential sum parameters (such as \(\mu _k\) and \(\lambda _k\) in (1)). In particular, one can find in [6] a family of g whose corresponding parameters of (1) tend to infinity thus making the interpolation process divergent.
To address this disadvantage, we consider in this paper a modified version of the exponential sums (1) and introduce and solve the corresponding Prony-type data fitting problem. Moreover, we prove that the parameters in our exponential sums are a priori well-controlled and thus can be found via a stable numerical framework, in contrast to those in the sums (1). Let us move to the formal description of our approach.
We introduce the following Prony-type data fitting problem: numerically interpolate the table
by the following exponential sums with equal weights
The fitting should be carried out by a proper choice of the parameters \(\mu \) and \(\{\lambda _k\}_{k=1}^K\) which depend on K, M and g. The fitting quality has to be evaluated in the sense of least squares via a numerical optimization method so that
The main result of the paper in the above-mentioned settings is about the construction and the a priori control of the parameters of \(H_K\) and is as follows.
Theorem 1
Given a table (2), the parameters of \(H_K\) are as follows: \(\mu =g(0)\) and the set \(\{\lambda _k\}_{k=1}^K\) is the solution to the Newton-type moment problem
Furthermore, if \(|g(m)|\leqslant \frac{|g(0)|}{K}\, a^m\) for all \(m=1,\ldots ,M\) and some \(a\geqslant 1\), thenFootnote 1
and moreover \(|H_K(x)|\leqslant |g(0)|\left( \kappa a \right) ^x\) for any \(x\in \mathbb {R}\).
Thus the parameters of \(H_K\) are well-controlled by g in (2) and by \(\delta \) in (4).
The paper is organised as follows. Section 2 provides necessary facts on and the theoretical comparison of the sums \(H_K\) and \(\mathcal {H}_K\). Section 3 is devoted to the proof of Theorem 1. Section 4 contains several experiments with \(H_K\) and \(\mathcal {H}_K\) illustrating the difference of their behaviour in numerical processes.
2 Necessary Facts on and the Comparison of \(H_K\) and Classical Prony Exponential Sums
The analytical construction of (3) with \(K=M\) for the table (2) was introduced in [1]. It was also shown that the problem (4) then can be solved analytically, with \(\delta =0\). Moreover, if the corresponding \(\mu \) and \(\{\lambda _k\}_{k=1}^M\) are known precisely and determined via the so-called Newton-Prony method, then \(g(z)=H_M(z)\) for \(z\in \{m\}_{m=0}^{M}\). Now we briefly describe the approach from [1].
Let \(L_M:=\{l_k\}_{k=1}^M\), where \(l_k\in \mathbb {C}\). Consider the power sums
One can find the set \(L_M\) from the Newton moment problem
via the elementary symmetric polynomials
The connection between the power sums (6) and the polynomials (8) is expressed by the well-known Newton-Girard formulas [13, Section 3.1]:
Moreover, \(L_M\) is then the set of M roots of the unitary polynomial
Consequently, given any \(s_m\), one can solve (7) using (9) and (10) and the solution \(L_M\) always exists and is unique. What is more, it is shown in [1] that the elements of \(L_M\) are well-controlled by the table (2) under few natural assumption on g. Namely, the following result is a consequence of what is proved in [1]:
For \(M\geqslant 2\), \(\gamma >0\) and \(a\geqslant 1\), if \(|s_m|\leqslant \gamma a^m\) in (7) for \(m=1,\ldots ,M\), then
Now we turn our attention to the Prony exponential sums (1). There exist a classical analytical Prony method for interpolating the table (2) with odd M (so that \(M+1\) is even) by the sums (1) with \(K=\tilde{M}:=(M+1)/2\), see e.g. [3, 6, 8, 10]. The main idea behind it is to separate calculating the parameters \(\mu _k\) and \(\lambda _k\). Namely, by supposing \(l_k:=\exp (\lambda _k)\) and \(s_m=g(m)\) one comes to the following Prony moment problem that is a weighted version of (7):
If this problem has a unique solution, then \(L_{\tilde{M}}=\{l_k\}_{k=1}^{\tilde{M}}\) is the set of \(\tilde{M}\) roots of the (possibly non-unitary) polynomial
which is an analogue of (9) and (10). Note that \(\{\mu _k,\lambda _k\}_{k=1}^{\tilde{M}}\) can be uniquely determined (and thus (1) constructed) if and only if the polynomial (13) for a given set \(\{s_m\}_{m=0}^M\) is exactly of degree \({\tilde{M}}\) and all its roots are pairwise distinct [6]. In general, the problem (12) can be unsolvable or have multiple solutions [6].
Let us mention that the system (12) is not only related to (1) but plays an important role in different areas of approximation theory and is closely related to Hankel matrices, Gauss quadratures, moment problems and classical Padé rational fractions (a survey can be found e.g. in [6, Section 2] or [8]).
Due to the importance of (1) and (12) in approximation theory and applied data fitting (see Introduction), multiple numerical approaches for data fitting by the sums (1) with \(K\leqslant \tilde{M}\) have been proposed [2, 4, 5, 11, 12]. The fitting quality evaluation is usually performed in the sense of least squares:
However, in sharp contrast to \(H_K\) within (4) and (7), there are no more or less general estimates for the parameters of \(\mathcal {H}_K\) similar to those in Theorem 1 and the theorems from [1], as seen from the huge bibliography on the Prony exponential sums ([2, 3, 5, 6, 8, 11, 12] and references therein). Moreover, numerical processes for finding solutions to (14) and (12) can be unstable and divergent (see [2, 6]).
To finish the comparison of \(H_K\) and \(\mathcal {H}_K\), let us also observe that computing (3) requires less arithmetic operations than that of (1) for each fixed z and known \(\mu \), \(\mu _k\) and \(\lambda _k\), see [1].
3 The Proof of Theorem 1
The identity for \(\mu \) follows directly from (3) and (4) for \(m=0\). The optimization problem (5) is then deduced from (4) by the exchange \(l_k:=\exp (\lambda _k)\).
Now let \(|g(m)|\leqslant \frac{|g(0)|}{K}\, a^m\) in (2) for all \(m=1,\ldots ,M\) and some \({a\geqslant 1}\). Once the solution \(\{l_k\}_{k=1}^K\) to (5) and a certain \(\delta \) are found by a numerical optimization method, we obtain by the triangle inequality that
Note that m here is from 1 to K, not M. Consequently, we come to the system (7) with K unknowns and K equations:
Furthermore, by (11) we easily obtain the required inequalities for \(\max _{k=1,\ldots ,K}|l_k|\) and \( \mathsf{Re}\,\lambda _k\). What is more, \( |H_K(x)|\leqslant \frac{|g(0)|}{K}\sum _{k=1}^K (\kappa a)^x\leqslant |g(0)| (\kappa a)^x\) for \(x\in \mathbb {R}\).
4 Numerical Experiments
Experiments below show the difference in the behaviour of \(H_K\) and \(\mathcal {H}_K\) in numerical processes and illustrate Theorem 1. In fact, one can use any suitable numerical method for finding the parameters of \(H_K\) and \(\mathcal {H}_K\) as the examples below are constructed to be independent of the method (see [2, 5, 11, 12] for the methods suitable for \(\mathcal {H}_K\); any numerical method for non-linear least squares can be adapted for \(H_K\)). We produced calculations using Maple 2019 tools with 200 significant digits and same environment for both \(H_K\) and \(\mathcal {H}_K\), to avoid the influence of a particular method and its precision.
In order to have the same number of free parameters in the exponential sums and to establish the connection with the problems (7) and (12), we solve the data fitting problems (4) and (14) with \(K=M\) and \(K=(M+1)/2\), correspondingly.
We consider the following parametric table of the form (2) with \(M=3\):
Note that (15) can be easily complemented to contain arbitrarily many elements. However, since the data (15) should be still fitted, the same effects will be observed for the corresponding exponential sums \(H_3\) and \(\mathcal {H}_2\) (see [6, Section 7]).
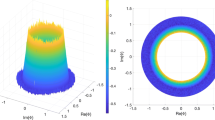
Plots of \(H_3\) (blue) and \(\mathcal {H}_2\) (red) for different \(\varepsilon \) in the table (15) (black points): (a) \(\varepsilon =10^{-1}\), (b) \(\varepsilon =10^{-6}\), (c) \(\varepsilon =10^{-7}\), (d) \(\varepsilon =10^{-8}\) (Color figure online).
It directly follows from (13) that (15) leads to a unique solution to (12) for \(0<\varepsilon \leqslant 10^{-1}\) (note that (7) always has such a solution) and therefore a proper numerical method should converge to this solution. Below we choose \(\delta =10^{-10}\) in (4) and (14). Table 1 and Fig. 1 contain the results for different \(\varepsilon >0\) and the extreme case \(\varepsilon =0\) (this case for \(\mathcal {H}_2\) was studied in [6, Section 7]).
It can be observed that for \(10^{-5}\leqslant \varepsilon \leqslant 10^{-1}\) both \(H_3\) and \(\mathcal {H}_2\) solve the data fitting problem with good quality (see Fig. 1(a)). For \(\varepsilon < 10^{-5}\), the precision of \(\mathcal {H}_2\) however shrinks significantly and the data is not fitted properly, while the fitting quality of \(H_3\) is still good (see Fig. 1(b), (c), (d)). This can be explained as follows.
The table (15) with \(\varepsilon \rightarrow 0\) leads to an unsolvable problem (12). Thus one has a divergent numerical process for \(\mathcal {H}_2\) (with \(|\lambda _{1,2}|\rightarrow \infty \) and \(|\mu _1|\rightarrow 0\)) as \(\varepsilon \rightarrow 0\). The corresponding computational errors significantly grow (200 significant digits for the parameters of \(\mathcal {H}_2\) are not already enough for a reasonable precision of \(\mathcal {H}_2\) itself) and this leads to the incorrect data fitting by \(\mathcal {H}_2\) (especially for \(m=3\)) represented in Fig. 1 (b), (c), (d).
Oppositely, since the parameters of \(H_3\) are well-controlled (in particular, Theorem 1 implies for the table (15) that \(\mu =1+\varepsilon \), \(\max _{k=1,\ldots ,3}|l_k|\leqslant 3.1(1+\varepsilon )\) and \( -\infty \leqslant \mathsf{Re}\,(\lambda _k) \leqslant \varepsilon +\ln 3.1\)), 200 significant digits stay enough for rather accurate calculation of \(H_3\) and its representation in Fig. 1 (b), (c), (d).
5 Conclusions
In this paper, we considered the exponential sums with equal weights (3) in the context of the Prony-type problem of fitting data (the table (2)) in the sense of non-linear least squares (4). We showed how the parameters \(\mu \) and \(\lambda _k\) of the sums (3) should be chosen for proper data fitting. Moreover, we proved that the parameters are well-controlled by (2) and by \(\delta \) in (4) (see Theorem 1) that is in sharp contrast to the case of parameters in the well-known Prony exponential sums (1). Furthermore, in several special numerical experiments, we compared the behaviour of the sums (3) and (1) and demonstrated that (3) do not produce divergent data fitting processes while (1) do in some cases.
Notes
- 1.
Due to the periodicity of the exponential function, one can think that \(| \mathsf{Im}\,\lambda _k|\leqslant \pi \).
References
Chunaev, P.: Interpolation by generalized exponential sums with equal weights. J. Approx. Theory 254 (2020). Article: 105397
Batenkov, D.: Decimated generalized Prony systems. arXiv:1308.0753 (2013)
Batenkov, D., Yomdin, Y.: On the accuracy of solving confluent Prony systems. SIAM J. Appl. Math. 73(1), 134–154 (2013)
Beylkin, G., Monzón, L.: On approximation of functions by exponential sums. Appl. Comput. Harmonic Anal. 19(1), 17–48 (2005)
Beylkin, G., Monzón, L.: Approximation by exponential sums revisited. Appl. Comput. Harmonic Anal. 28, 131–149 (2010)
Chunaev, P., Danchenko, V.: Approximation by amplitude and frequency operators. J. Approx. Theory 207, 1–31 (2016)
Keller, I., Plonka, G.: Modifications of Prony’s method for the recovery and sparse approximation of generalized exponential sums. arXiv:2001.03651 (2020)
Lyubich, Y.I.: The Sylvester-Ramanujan system of equations and the complex power moment problem. Ramanujan J. 8, 23–45 (2004). https://doi.org/10.1023/B:RAMA.0000027196.19661.b7
Mourrain, B.: Polynomial-exponential decomposition from moments. Found. Comput. Math. 18, 1435–1492 (2018). https://doi.org/10.1007/s10208-017-9372-x
Pereyra, V., Scherer, G.: Exponential Data Fitting and Its Applications. Bentham Science Publishers, Sharjah (2018)
Plonka, G., Tasche, M.: Prony methods for recovery of structured functions. GAMM-Mitt. 37(2), 239–258 (2014)
Potts, D., Tasche, M.: Parameter estimation for nonincreasing exponential sums by Prony-like methods. Linear Algebra Appl. 439(4), 1024–1039 (2013)
Prasolov, V.V.: Polynomials. Algorithms and Computation in Mathematics, vol. 11. Springer, Heidelberg (2004). https://doi.org/10.1007/978-3-642-03980-5
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Chunaev, P., Safiullin, I. (2020). Data Fitting by Exponential Sums with Equal Weights. In: Krzhizhanovskaya, V., et al. Computational Science – ICCS 2020. ICCS 2020. Lecture Notes in Computer Science(), vol 12138. Springer, Cham. https://doi.org/10.1007/978-3-030-50417-5_27
Download citation
DOI: https://doi.org/10.1007/978-3-030-50417-5_27
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-50416-8
Online ISBN: 978-3-030-50417-5
eBook Packages: Computer ScienceComputer Science (R0)