Abstract
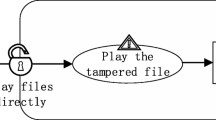
In a cloud environment, the control logic and data forwarding of network devices are separated from each other. The control layer is responsible for the centralized management of network nodes. After it acquires the entire network topology, it can automatically generate a visualized network structure. The security analyst can grasp the connection status of the devices on the entire network in the control domain. The network topology generation method based on the control layer information is directly and efficiently, which can greatly simplify the description of security events in the cloud environment. At the same time, the separate structure also makes the specific details of the underlying network device hidden. Petri-net, as a formal description tool, can be used to describe such a structure. Based on the cloud environment structure, this paper combines the advantages of CORAS modeling and analysis with object-oriented Petri-net theory, and proposes a COP (CORAS-based Object Oriented Petri-net)-based intelligent system security event description method. Model the description of the complexity and dynamics of cloud environment security events.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Hong, J.E., Bae, D.H.: Software modeling and analysis using a hierarchical object-oriented Petri net. Inf. Sci. Int. J. 130, 131–164 (2000)
Brændeland, G., Dahl, H.E.I., Engan, I., Stølen, K.: Using dependent CORAS diagrams to analyse mutual dependency. In: Lopez, J., Hämmerli, B.M. (eds.) CRITIS 2007. LNCS, vol. 5141, pp. 135–148. Springer, Heidelberg (2008). https://doi.org/10.1007/978-3-540-89173-4_12
De Oliveira, R.L.S., Shinoda, A.A., Schweitzer, C.M., et al.: Using mininet for emulation and prototyping software-defined networks. In: IEEE Colombian Conference on Communications and Computing, pp. 1–6. IEEE, Bogota (2014)
Liu, X., Wang, H., Lai, J., et al.: Multiclass support vector machines theory and its data fusion application in network security situation awareness. In: 2007 International Conference on Wireless Communications, Networking and Mobile Computing, pp. 6349–6352. IEEE, Shanghai (2007)
Shin, S., Yegneswaran, V., Porras, P., et al.: AVANT-GUARD: scalable and vigilant switch flow management in software-defined networks. In: ACM SIGSAC Conference on Computer & Communications Security, pp. 413–424. ACM (2013)
Xu, X., Liu, Q., Zhang, X., Zhang, J., Qi, L., Dou, W.: A blockchain-powered crowdsourcing method with privacy preservation in mobile environment. IEEE Trans. Comput. Soc. Syst. 6(6), 1407–1419 (2019)
Qi, L., Chen, Y., Yuan, Y., Fu, S., Zhang, X., Xu, X.: A QoS-aware virtual machine scheduling method for energy conservation in cloud-based cyber-physical systems. World Wide Web 23, 1275–1297 (2020). https://doi.org/10.1007/s11280-019-00684-y
Qi, L., et al.: Finding all you need: web APIs recommendation in web of things through keywords search. IEEE Trans. Comput. Soc. Syst. 6(5), 1063–1072 (2019)
Li, Q., Meng, S., Wang, S., Zhang, J., Hou, J.: CAD: command-level anomaly detection for vehicle-road collaborative charging network. IEEE Access 7, 34910–34924 (2019)
Li, Q., Meng, S., Zhang, S., Hou, J., Qi, L.: Complex attack linkage decision-making in edge computing networks. IEEE Access 7, 12058–12072 (2019)
Li, Q., et al.: Safety risk monitoring of cyber-physical power systems based on ensemble learning algorithm. IEEE Access 7, 24788–24805 (2019)
Li, Q., Wang, Y., Pu, Z., Wang, S., Zhang, W.: A time series association state analysis method in smart internet of electric vehicle charging network attack. Transp. Res. Rec. 2673, 217–228 (2019)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 ICST Institute for Computer Sciences, Social Informatics and Telecommunications Engineering
About this paper
Cite this paper
Hou, J., Li, Q., Chen, Y., Meng, S., Long, H., Sun, Z. (2020). Intelligent System Security Event Description Method. In: Zhang, X., Liu, G., Qiu, M., Xiang, W., Huang, T. (eds) Cloud Computing, Smart Grid and Innovative Frontiers in Telecommunications. CloudComp SmartGift 2019 2019. Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, vol 322. Springer, Cham. https://doi.org/10.1007/978-3-030-48513-9_39
Download citation
DOI: https://doi.org/10.1007/978-3-030-48513-9_39
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-48512-2
Online ISBN: 978-3-030-48513-9
eBook Packages: Computer ScienceComputer Science (R0)