Abstract
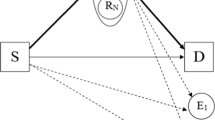
This paper studies physical layer security of a three node multicarrier network with a source node, a destination node and a full-duplex proactive eavesdropper who sends jamming signals for improving its eavesdropping performance. The problem of transmit power allocation for minimizing the average secrecy outage probability on all subcarriers is investigated under the assumptions that the channel state information (CSI) related to the eavesdropper is perfectly known and only channel distribution information (CDI) is known. Algorithms are proposed for the optimization problem and are shown to greatly outperform the benchmark algorithms.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Xu, D., Li, Q.: Resource allocation for cognitive radio with primary user secrecy outage constraint. IEEE Syst. J. 12, 893–904 (2018)
Liu, Y., Chen, H.H., Wang, L.: Physical layer security for next generation wireless networks: theories, technologies, and challenges. IEEE Commun. Surv. Tutor. 19(1), 347–376 (2017)
Xu, D., Li, Q.: Resource allocation for secure communications in cooperative cognitive wireless powered communication networks. IEEE Syst. J. 13(3), 2431–2442 (2019)
Zhang, H., Xing, H., Cheng, J., Nallanathan, A., Leung, V.C.: Secure resource allocation for ofdma two-way relay wireless sensor networks without and with cooperative jamming. IEEE Trans. Ind. Inf. 12(5), 1714–1725 (2015)
Tang, X., Ren, P., Han, Z.: Power-efficient secure transmission against full-duplex active eavesdropper: a game-theoretic framework. IEEE Access 5, 24632–24645 (2017)
Tang, X., Ren, P., Wang, Y., Han, Z.: Combating full-duplex active eavesdropper: a hierarchical game perspective. IEEE Trans. Commun. 65(3), 1379–1395 (2017)
Fang, H., Xu, L., Zou, Y., Wang, X., Choo, K.K.R.: Three-stage stackelberg game for defending against full-duplex active eavesdropping attacks in cooperative communication. IEEE Trans. Veh. Technol. 67(11), 10788–10799 (2018)
Huang, W., Chen, W., Bai, B., Han, Z.: Wiretap channel with full-duplex proactive eavesdropper: a game theoretic approach. IEEE Trans. Veh. Technol. 67(8), 7658–7663 (2018)
Liu, C., Lee, J., Quek, T.Q.: Secure transmission in the presence of full-duplex active eavesdropper. In: IEEE Global Communications Conference, pp. 1–6. IEEE (2017)
Li, L., Petropulu, A.P., Chen, Z.: Mimo secret communications against an active eavesdropper. IEEE Trans. Inf. Forensics Secur. 12(10), 2387–2401 (2017)
Xu, D., Zhu, H.: Secure transmission for SWIPT IoT systems with full-duplex IoT devices. IEEE Internet Things J. 6(6), 10915–10933 (2019)
Boyd, S., Vandenberghe, L.: Convex Optimization. Cambridge University Press, Cambridge (2004)
Xu, D., Li, Q.: Improving physical-layer security for primary users in cognitive radio networks. IET Commun. 11(15), 2303–2310 (2017)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 ICST Institute for Computer Sciences, Social Informatics and Telecommunications Engineering
About this paper
Cite this paper
Li, Q., Xu, D. (2020). Secure Communication with a Proactive Eavesdropper Under Perfect CSI and CDI. In: Gao, H., Feng, Z., Yu, J., Wu, J. (eds) Communications and Networking. ChinaCom 2019. Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, vol 312. Springer, Cham. https://doi.org/10.1007/978-3-030-41114-5_39
Download citation
DOI: https://doi.org/10.1007/978-3-030-41114-5_39
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-41113-8
Online ISBN: 978-3-030-41114-5
eBook Packages: Computer ScienceComputer Science (R0)