Abstract
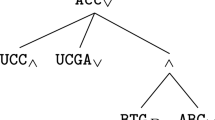
A main problem for the detection of security violations in misuse detection systems is the manner how attack scenarios (signatures) are described. Attack languages are used to specify attack scenarios for misuse detection systems. Usually not only the attack signatures are described also some details controlling the detection process have to be noted. This is disadvantageous because it makes signature development more complicated and prone to errors. In this paper we propose an attack language for describing signatures without caring about the used detection techniques. The language further provides means to simplify the description of attack signatures.
The work described here was partially funded by Deutsche Forschungsgemeinschaft under contract number Ko 1273/13-1.
The original version of this chapter was revised: The copyright line was incorrect. This has been corrected. The Erratum to this chapter is available at DOI: 10.1007/978-0-387-35586-3_46
Chapter PDF
Similar content being viewed by others
References
Eckmann, S. T.; Vigna, G.; Kemmerer, R. A.: STATL: an Attack Language for Statebased Intrusion Detection, in Proc. of the ACM Workshop on Intrusion Detection, Athens, Greece, Nov. 2000.
Michel, C.; Me, L.: ADeLe: an Attack Description Language for Knowledge-based Intrusion Detection, in Proc. of the International Conference on Information Security, Kluwer, Jun. 2001.
Mounji, A.: Languages and Tools for Rule-Based Distributed Intrusion Detection, PhD thesis, University of Namur. Belgium Sen. 1997
Lindqvist, U.; Porras, P. A.: Detecting Computer and Network Misuse with the Production-Based Expert System Toolset (P-BEST), in Proc. of the IEEE Symposium on Security and Privacy, IEEE Computer Society Press, Los Alamitos, CA, Oakland, CA, May 1999, DD. 146–161.
Sobirey, M.; Richter, B.; König, H.: The Intrusion Detection System AID. Architecture, and experiences in automated audit analysis, in Proc. of the International Conference on Communication and Multimedia Security, Essen, Germany, Sep. 1996, Chapman & Hall, London, pp. 278–290.
Vigna, G.; Eckmann, S. T.; Kemmerer, R. A.: Attack Languages, in: Proc. of the IEEE Information Survivability Workshop. Boston. MA, Oct 2000
Sun Microsystems, Inc.: SunSHIELD Basic Security Module Guide, Solaris 2.6 System Administrator Collection Vol 1, Mountain View. CA, 1997.
Vigna, G.; Eckmann, S. T.; Kemmerer, R. A.: The STAT Tool Suite, in Proc. of DISCEX, Hilton Head, South Carolina, IEEE Computer Society Press. Jan. 2000
Kumar, S.: Classification and Detection of Computer Intrusions, PhD Thesis, Purdue University, 1995.
Cuppens, F.; Ortalo, R.: LAMBDA: A Language to Model a Database for Detection of Attacks, in Proc. of the Third International Workshop on the Recent Advances in Intrusion Detection, LNCS 1907, Springer, 2000, pp. 197–216.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2002 IFIP International Federation for Information Processing
About this chapter
Cite this chapter
Meier, M., Bischof, N., Holz, T. (2002). SHEDEL — A Simple Hierarchical Event Description Language for Specifying Attack Signatures. In: Ghonaimy, M.A., El-Hadidi, M.T., Aslan, H.K. (eds) Security in the Information Society. IFIP Advances in Information and Communication Technology, vol 86. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-35586-3_44
Download citation
DOI: https://doi.org/10.1007/978-0-387-35586-3_44
Publisher Name: Springer, Boston, MA
Print ISBN: 978-1-4757-1026-7
Online ISBN: 978-0-387-35586-3
eBook Packages: Springer Book Archive