Abstract
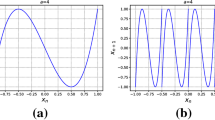
We propose a modified version of the chaotic cryptographic method based on iterating a logistic map. Simulation results show that the distribution of the ciphertext is flatter and the encryption time is shorter. Moreover, the trade-off between the spread of the distribution of ciphertext and the encryption time can be controlled by a single parameter.
The original version of this chapter was revised: The copyright line was incorrect. This has been corrected. The Erratum to this chapter is available at DOI: 10.1007/978-0-387-35413-2_36
Chapter PDF
Similar content being viewed by others
Keyword
References
G. Grassi, S. Mascolo, Electron. Lett. 34 (1998) 1844.
Y.H. Chu and S. Chang, Electron Lett. 35 (1999) 271–273.
T. Yang Tao, C.W. Wu, L.O. Chua, IEEE Trans. CASI 44 (1997) 469.
M.S. Baptista, Phys. Lett. A 240 (1998) 50.
E. Alvarez, A. Fernandez, P. Garcia, J. Jimenez, A. Marcano, Phys. Lett. A 263 (1999) 373.
A.J. Menezes, P.C. Oorschot, and S.A. Vanstone, Handbook of Appl. Cryptography ( CRC Press, New York, 1996 ).
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2001 IFIP International Federation for Information Processing
About this chapter
Cite this chapter
Wong, Wk., Lee, Lp., Wong, Kw. (2001). A Modified Chaotic Cryptographic Method. In: Steinmetz, R., Dittman, J., Steinebach, M. (eds) Communications and Multimedia Security Issues of the New Century. IFIP — The International Federation for Information Processing, vol 64. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-35413-2_11
Download citation
DOI: https://doi.org/10.1007/978-0-387-35413-2_11
Publisher Name: Springer, Boston, MA
Print ISBN: 978-1-4757-4811-6
Online ISBN: 978-0-387-35413-2
eBook Packages: Springer Book Archive