Abstract
In 1993 Lennon and Smith proposed to use Lucas functions instead of the exponentiation function as a one-way function in cryptographic mechanisms. Recently Smith and Skinner presented an ElGamal signature scheme based on Lucas functions.
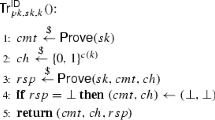
In this paper we point out a serious weakness in this approach and present our version of an ElGamal signature scheme based on Lucas functions. Furthermore, we outline how to apply the ideas of the Meta-ElGamal signature scheme to Lucas functions. As a result we get various new signature schemes. In contradiction to a conjecture by Smith and Skinner the security of the schemes isn’t increased: It can be proved that a variant of the signature schemes based on Lucas functions can be universally forged if a related signature scheme in GF(p) can be universally forged. We further outline how the Meta signature scheme can be described in an elliptic curve environment and mention some other possible extensions.
Chapter PDF
Similar content being viewed by others
References
T. ElGamal, (1984), Cryptography and logarithms over finite fields, Ph. D. thesis, Stanford University, CA., UMI Order No. DA 8420519, 119 pages.
P. Horster, M. Michels, H. Petersen, (1994), Meta-ElGamal signature scheme for one message block, Proc. of the Workshop IT-Security, Vienna, Sep. 22–23, 1994, R. Oldenbourg Wien München, 1995, pp. 66–81.
P. Horster, M. Michels, H. Petersen, (1994), Meta-ElGamal signature scheme, Proc. of the 2nd ACM Conference on Computer and Communications Security, Fairfax, Virginia, Nov. 2–4, 1994, pp. 96–107.
P. Horster, M. Michels, H. Petersen, (1994), Meta Message Recovery and Meta blind signature schemes based on the discrete logarithm problem and some applications, Lecture Notes in Computer Science 917, Advances in Cryptology: Proc. Asiacrypt ‘84, Berlin: Springer Verlag, 1995, pp. 224–37.
D. E. Knuth, (1981), The art of computer programming, Vol. 2: Seminumerical algorithms, 2nd Edition, Addison-Wesley, Reading, MA.
C.-S. Laih, F.-K. Tu, W.-C. Tai, (1994), Remarks on LUC public key system, Electronics Letters, Vol. 30, No. 2, pp. 123–4.
C.-S. Laih, F.-K. Tu, W.-C. Tai, (1995), On the security of Lucas function, Information Processing Letters, Vol. 53, pp. 243–7.
F. E. A. Lucas, (1878), Theorie des fonctions numeriques simplement periodiques, American Journal Mathematics, Vol. 1, pp. 184–240 and 289–321.
D. H. Lehmer, (1930), An extended theory of Lucas’ functions, Annals of Mathematics (2), Vol. 31, pp. 419–48.
A. J. Menezes, M. Qu, S. A. Vanstone, (1995), Standard for RSA, Diffie-Hellman and related public-key cryptography, Part 6: Elliptic curve systems (Draft 3), Working Draft, IEEE P1363 Standard, January, 42 pages.
A. Miyaji, (1992), Elliptic curves over F„ suitable for cryptosystems, Lecture Notes in Computer Science 718, Advances in Cryptology: Proc. Asiacrypt ‘82, Berlin: Springer Verlag, 1993, pp. 224–37.
W. B. Müller, W. Nöbauer, (1981), Some remarks on public key cryptosystems, Studia Sci. Math. Hung., Vol. 16, pp. 71–6.
W. B. Müller, R. Nöbauer, (1985), Cryptanalysis of the Dickson-scheme, Lecture Notes in Computer Science 219, Advances in Cryptology: Proc, Eurocrypt’85, Berlin: Springer Verlag, 1986, pp. 50–61.
S. Murphy, (1994), Comment: Remarks on LUC public key system, Electronics Letters, Vol. 30, No. 7, pp. 558–9.
K. Nyberg, R. A. Rueppel, (1994), Message recovery for signature schemes based on the discrete logarithm problem, 21 July 1994, to appear in Design, Codes and Cryptography, Kluwer Academic Publishers, Boston, 15 pages.
H. Postl, (1988), Fast evaluation of Dickson Polynomials, Contributions to General Algebra 6, Verlag Hölder-Pichler-Tempsky, Wien–Verlag B. G. Teubner, Stuttgart, pp. 223–5.
D. Shanks, (1971), Class number, a theory of factorisation and genera, Proceedings Symposia in Pure Mathematics (20), Providence: American Mathematical Society, pp. 415–40.
P. Smith, C. Skinner, (1994), A public key cryptosystem and a digital signature scheme based on Lucas functions analogue to discrete logarithms, Lecture Notes in Computer Science 917, Advances in Cryptology: Proc. Asiacrypt ‘84, Berlin: Springer Verlag, 1995, pp. 357–64.
P. Smith, M. Lennon, (1993), LUC: A new public-key system, Proc. of IFIP/SEC ‘83, Elsevier Science Publishers, 1994, pp. 97–110.
H. Williams, (1982), A p + 1 method of factoring, Mathematics on Computation, Vol. 39, pp. 225–34.
S.-M. Yen, C.-S. Laih, (1995), Fast algorithms for the LUC digital signature computation, IEE Proc.-Comput. Digit. Tech., Vol. 142, No. 2, pp. 165–9.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1995 IFIP International Federation for Information Processing
About this chapter
Cite this chapter
Horster, P., Michels, M., Petersen, H. (1995). Digital signature schemes based on Lucas functions. In: Posch, R. (eds) Communications and Multimedia Security. IFIP Advances in Information and Communication Technology. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-34943-5_15
Download citation
DOI: https://doi.org/10.1007/978-0-387-34943-5_15
Publisher Name: Springer, Boston, MA
Print ISBN: 978-1-5041-2908-4
Online ISBN: 978-0-387-34943-5
eBook Packages: Springer Book Archive