Abstract
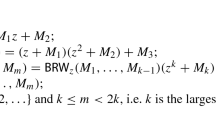
In this paper we consider very fast evaluation of strongly universal hash functions, or equivalently, authentication codes. We show how it is possible to modify some known families of hash functions into a form such that the evaluation is similar to “bucket hashing”, a technique for very fast hashing introduced by Rogaway. Rogaway’s bucket hash family has a huge key size, which for common parameter choices can be more than a hundred thousand bits. The proposed hash families have a key size that is close to the key size of the theoretically best known constructions, typically a few hundred bits, and the evaluation has a time complexity that is similar to bucket hashing.
Chapter PDF
Similar content being viewed by others
Keywords
References
V. Afanassiev, C. Gehrmann, B. Smeets, Fast message authentication using efficient polynomial evaluation, Proceedings of Fast Software Encryption Conference’ 97, to appear.
M. Bellare, R. Canetti, H. Krawczyk, Keying hash functions for message authentication, Lecture Notes in Computer Science 1109 (1996), 1–15 (CRYPTO’ 96).
M. Bellare, R. Guérin, P. Rogaway, XOR MACs: New methods for message authentication, Lecture Notes in Computer Science 963 (1995), 15–28 (CRYPTO’ 95).
M. Bellare, J. Kilian, P. Rogaway, The security of cipher block chaining, Lecture Notes in Computer Science 839 (1994), 341–358 (CRYPTO’ 94).
J. Bierbrauer, T. Johansson, G. Kabatianskii, and B. Smeets, On families of hash functions via geometric codes and concatenation, Lecture Notes in Computer Science, 773 (1994), 331–342 (CRYPTO’ 93).
B. den Boer, A simple and key-economical unconditionally authentication scheme, Journal of Computer Security, 2 (1993), 65–71.
A. Bosselaers, R. Govaerts, J. Vandewalle, Fast hashing on the Pentium, Lecture Notes in Computer Science 1109 (1996), 298–313 (CRYPTO’ 96).
J.L. Carter, M.N. Wegman, Universal classes of hash functions, J. Computer and System Sciences, 18 (1979), 143–154.
H. Dobbertin, Cryptoanalysis of MD5 compress, presented at the rump session of EUROCRYPT’96.
E.N. Gilbert, F.J. MacWilliams, and N.J.A. Sloane, Codes which detect deception, Bell Syst. Tech. J., 53 (1974), 405–424.
S. Halevi, H. Krawczyk, Software message authentication in the Gbit/second rates, Proceedings of Fast Software Encryption Conference’ 97, to appear.
T. Helleseth and T. Johansson, Universal hash functions from exponential sums over finite fields and Galois rings, Lecture Notes in Computer Science 1109 (1996), 31–44 (CRYPTO’ 96).
T. Johansson, A shift register construction of unconditionally secure authentication codes, Designs, Codes and Cryptography, 4 (1994), 69–81.
T. Johansson, G. Kabatianskii, B. Smeets, On the relation between A-codes and codes correcting independent errors, Lecture Notes in Computer Science, 765 (1994), 1–11 (EUROCRYPT’93).
G. Kabatianskii, B. Smeets, and T. Johansson, On the cardinality of systematic authentication codes via error correcting codes, IEEE Trans. Inform. Theory, 42 (1996), 566–578.
H. Krawczyk, LFSR-based hashing and authentication, Lecture Notes in Computer Science, 839 (1994), 129–139 (CRYPTO’ 94).
H. Krawczyk, New hash functions for message authentication, Lecture Notes in Computer Science, 921 (1995), 140–149 (EUROCRYPT’ 95).
B. Preneel, Cryptographic hash functions, European Transactions on Telecommunications, 5 (1994), 431–448.
B. Preneel, P. van Oorschot, MDx-MAC and building fast MACs from hash functions, Lecture Notes in Computer Science, 963 (1995), 1–14 (CRYPTO’ 95).
B. Preneel, P. van Oorschot, On the security of two MAC algorithms, Lecture Notes in Computer Science, 1070 (1996), 19–32 (EUROCRYPT’ 96).
R.L. Rivest, The MD5 message-digest algorithm, Request for Comments 1321, Internet Activities Board, Internet Privacy Task Force (1992).
P. Rogaway, Bucket hashing and its application to fast message authentication, Lecture Notes in Computer Science, 963 (1995), 29–42 (CRYPTO’ 95).
B. Schneier, Applied Cryptography, John Wiley & Sons (1996).
V. Shoup, On fast and provably secure message authentication based on universal hashing, Lecture Notes in Computer Science, 1109 (1996), 313–328 (CRYPTO’ 96).
G.J. Simmons, A game theory model of digital message authentication, Congr. Numer., 34 (1992), 413–424.
G.J. Simmons, Authentication theory/coding theory, in Lecture Notes in Computer Science, 196 (1985), 411–431 (CRYPTO’ 84).
D.R. Stinson, Universal hashing and authentication codes, Codes, Designs and Cryptography, 4 (1994), 337–346.
M.N. Wegman and J.L. Carter, New hash functions and their use in authentication and set equality, J. Computer and System Sciences, 22 (1981), 265–279.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1997 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Johansson, T. (1997). Bucket Hashing with a Small Key Size. In: Fumy, W. (eds) Advances in Cryptology — EUROCRYPT ’97. EUROCRYPT 1997. Lecture Notes in Computer Science, vol 1233. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-69053-0_12
Download citation
DOI: https://doi.org/10.1007/3-540-69053-0_12
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-62975-7
Online ISBN: 978-3-540-69053-5
eBook Packages: Springer Book Archive