Abstract
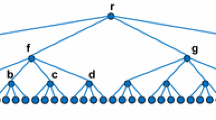
This paper describes a simple candidate one-way hash function which satisfies a quasi-commutative property that allows it to be used as an accumulator. This property allows protocols to be developed in which the need for a trusted central authority can be eliminated. Space-efficient distributed protocols are given for document time stamping and for membership testing, and many other applications are possible.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Beaver, D. “Efficient Multiparty Protocols Using Circuit Randomization.” Advances in Cryptology — Crypto’ 91, ed. by J. Feigenbaum in Lecture Notes in Computer Science, vol. 576, ed. by G. Goos and J. Hartmanis. Springer-Verlag, New York (1992), 420–432.
Beaver, D. “Multiparty Protocols Tolerating Half Faulty Processors.” Advances in Cryptology — Crypto’ 89, ed. by G. Brassard in Lecture Notes in Computer Science, vol. 435, ed. by G. Goos and J. Hartmanis. Springer-Verlag, New York (1990), 560–572.
Beaver, D. and Goldwasser, S. “Multiparty Computation with Faulty Majority.” Proc. 30thIEEE Symp. on Foundations of Computer Science, Research Triangle Park, NC (Oct.–Nov. 1989), 468–473.
Benaloh, J. and de Mare, M. “Efficient Broadcast Time-Stamping.” Clarkson University Department of Mathematics and Computer Science TR 91-1. (Aug. 1991).
Ben-Or, M. “Another Advantage of Free Choice: Completely Asynchronous Agreement Protocols.” Proc. 2ndACM Symp. on Principles of Distributed Computing, Montreal, PQ (Aug. 1983), 27–30.
Ben-Or, M., Goldwasser, S., and Wigderson, A. “Completeness Theorems for Non-Cryptographic Fault-Tolerant Distributed Computation.” Proc. 20stACM Symp. on Theory of Computation, Chicago, IL (May 1988), 1–10.
de Bruijn, N. “The Asymptotic Behaviour of a Function Occurring in the Theory of Primes.” Journal of the Indian Mathematical Society 15. (1951), 25–32.
Chaum, D., Crépeau, C., and Damgård, I. “Multiparty Unconditionally Secure Protocols.” Proc. 20stACM Symp. on Theory of Computation, Chicago, IL (May 1988), 11–19.
Chor, B., Goldwasser, S., Micali, S., and Awerbuch, B. “Verifiable Secret Sharing and Achieving Simultaneity in the Presence of Faults.” Proc. 26thIEEE Symp. on Foundations of Computer Science, Portland, OR (Oct. 1985), 383–395.
Denning, D. Cryptography and Data Security, Addison-Wesley, Reading, Massachusetts (1982).
Fischer, M. “The Consensus Problem in Unreliable Distributed Systems”, Proc. 1983 International FCT-Conference, Borgholm, Sweeden (Aug. 1983), 127–140. Published as Foundations of Computation Theory, ed. by M. Karpinski in Lecture Notes in Computer Science, vol. 158, ed. by G. Goos and J. Hartmanis. Springer-Verlag, New York (1983).
Goldreich, O., Micali, S., and Wigderson, A “Proofs that Yield Nothing but Their Validity and a Methodology of Cryptographic Protocol Design.” Proc. 27thIEEE Symp. on Foundations of Computer Science, Toronto, ON (Oct. 1986), 174–187.
Goldreich, O., Micali, S., and Wigderson, A “How to Play Any Mental Game or A Completeness Theorem for Protocols with Honest Majority.” Proc. 19stACM Symp. on Theory of Computation, New York, NY (May 1987), 218–229.
Goldwasser, S. and Levin, L. “Fair Computation of General Functions in Presence of Immoral Majority.” Advances in Cryptology — Crypto’ 90, ed. by A. Menezes and S. Vanstone in Lecture Notes in Computer Science, vol. 537, ed. by G. Goos and J. Hartmanis. Springer-Verlag, New York (1991), 77–93.
Haber, S. and Stornetta, W. “How to Time-Stamp a Digital Document.” Journal of Cryptology 3. (1991), 99–112.
Knuth, D. and Trabb Pardo, L. “Analysis of a Simple Factorization Algorithm.” Theoretical Computer Science 3. (1976), 321–348.
Impagliazzo, R., Levin, L., and Luby, M. “Pseudorandom Generation from One-Way Functions.” Proc. 21stACM Symp. on Theory of Computation, Seattle, WA (May 1989), 12–24.
van de Lune, J. and Wattel, E. “On the Numerical Solution of a Differential-Difference Equation Arising in Analytic Number Theory.” Mathematics of Computation 23. (1969), 417–421.
Merkle, R. “Protocols for Public Key Cryptosystems.” Proc. 1980 Symp. on Security and Privacy, IEEE Computer Society (April 1980), 122–133.
Micali, T. and Rabin, T. “Collective Coin Tossing Without Assumptions nor Broadcasting.” Advances in Cryptology — Crypto’ 90, ed. by A. Menezes and S. Vanstone in Lecture Notes in Computer Science, vol. 537, ed. by G. Goos and J. Hartmanis. Springer-Verlag, New York (1991), 253–266.
Mitchell, W. “An Evaluation of Golomb’s Constant.” Mathematics of Computation 22. (1968), 411–415.
Naor, M. and Yung, M. “Universal One-Way Hash Functions and their Cryptographic Applications.” Proc. 21stACM Symp. on Theory of Computation, Seattle, WA (May 1989), 33–43.
Rabin, T. and Ben-Or, M. “Verifiable Secret Sharing and Multiparty Protocols with Honest Majority.” Proc. 21stACM Symp. on Theory of Computation, Seattle, WA (May 1989), 73–85.
Rabin, M. “Randomized Byzantine Generals.” Proc. 24thIEEE Symp. on Foundations of Computer Science, Tucson, AZ (Nov. 1983), 403–409.
Rompel, J. “One-Way Functions are Necessary and Sufficient for Secure Signatures.” Proc. 22ndACM Symp. on Theory of Computation, Baltimore, MD (May 1990).
Rivest, R., Shamir, A., and Adleman, L. “A Method for Obtaining Digital Signatures and Public-key Cryptosystems.” Comm. ACM 21,2 (Feb. 1978), 120–126.
Shamir, A. “On the Generation of Cryptographically Strong Pseudo-Random Sequences.” Proc. ICALP, (1981).
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1994 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Benaloh, J., de Mare, M. (1994). One-Way Accumulators: A Decentralized Alternative to Digital Signatures. In: Helleseth, T. (eds) Advances in Cryptology — EUROCRYPT ’93. EUROCRYPT 1993. Lecture Notes in Computer Science, vol 765. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-48285-7_24
Download citation
DOI: https://doi.org/10.1007/3-540-48285-7_24
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-57600-6
Online ISBN: 978-3-540-48285-7
eBook Packages: Springer Book Archive