Abstract
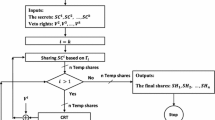
For some secret sharing applications, the secret reconstructed is not revealed to the participants, and therefore, the secret/shadows can be repeatedly used without having to be changed. But for other applications, in which the secret reconstructed is revealed to participants, a new secret must be chosen and its corresponding shadows must be regenerated and then secretly distributed to participants again, in order to enforce the same secret sharing policy. This is inefficient because of the overhead in the generation and distribution of shadows. In this paper, an l-span secret sharing scheme for the general sharing policy is proposed to solve the secret/shadows regeneration problem by extending the life span of the shadows from 1 to l, i. e., the shadows can be repeatedly used for l times to generate l different secrets.
Chapter PDF
Similar content being viewed by others
References
A. Shamir, “How to Share a Secret”, Communication ACM 22, 11, Nov. 1979, 612–613.
M. Ito, A. Saito, and T. Nishizeki, “Secret Sharing Scheme Realizing General Access Structure”, Proc. Glob. Com (1987).
J. Benaloh, and J. Leichter, “Generalized Secret Sharing and Monotone Functions”, Proc. Crypto’ 88, Springer-Verlag, 27–35.
H. Y. Lin and L. Harn, “A Generalized Secret Sharing Scheme with Cheater Detection”, Proc. Asiacrypt’ 91, Nov. 1991, Japan.
C. S. Laih, L. Harn, J. Y. Lee and T. Hwang, “Dynamic Threshold Scheme Based on the Definition of Cross-Product in an N-Dimensional Linear Space”, Proc. Crypto’ 89, Springer-Verlag, 286–297.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1993 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Harn, L., Lin, HY. (1993). An l-Span Generalized Secret Sharing Scheme. In: Brickell, E.F. (eds) Advances in Cryptology — CRYPTO’ 92. CRYPTO 1992. Lecture Notes in Computer Science, vol 740. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-48071-4_40
Download citation
DOI: https://doi.org/10.1007/3-540-48071-4_40
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-57340-1
Online ISBN: 978-3-540-48071-6
eBook Packages: Springer Book Archive