Abstract
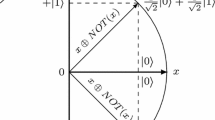
Every cryptosystem with an n-bit block length may be modeled as a system of n-bit boolean equations. The cipher is said to be nondegenerate if the equation f i that describes the output c i is nondegenerate, for 1 ≤ i ≤ n. Let N n,n be the set of nondegenerate permutations. We will derive an exact expression for |N n,n|, and show that
.
Chapter PDF
Similar content being viewed by others
References
A. Adams and S. Tavares. The structured design of cryptographically good S-boxes. Journal of Cryptology, 3(1):27–41, 1990.
F. Ayoub. Probabilistic completeness of substitution-permutation encryption networks. IEE proceedings, 129, part E(5):196–199, 1982.
D. Chaum and J. H. Everste. Cryptanalysis of DES with a reduced number of rounds. Advances in Cryptology, CRYPTO 85, H. C. Williams ed., Lecture Notes in Computer Science, vol. 218, Springer-Verlag, pages 192–211, 1986.
D. Coppersmith and E. Grossman. Generators for certain alternating groups with applications to cryptography. SIAM Journal of Applied Mathematics, 29(4):624–627, 1974.
S. Even and O. Goldreich. DES-like functions can generate the alternating group. IEEE Transactions on Information Theory, IT-29(6):863–865, 1983.
H. Feistel. Cryptography and computer privacy. Scientific American, 228(5):15–23, 1973.
H. Feistel, W. A. Notz, and J. Lynn Smith. Some cryptographic techniques for machine-to-machine data communications. proceedings of the IEEE, 63(11):1545–1554, 1975.
J. Gordon and H. Retkin. Are big S-boxes best? In T. Beth, editor, Cryptography, proceedings, Burg Feuerstein, pages 257–262, 1982.
M. A. Harrison. Introduction to Switching and Automata Theory. McGraw-Hill, Inc., 1965.
S. T. Hu. Mathematical Theory of Swithcing Circuits and Automata. Berkeley, University of California Press, 1968.
J. B. Kam and G. I. Davida. A structrued design of substitution-permutation encryption networks. IEEE Transactions on Computers, 28(10):747–753, 1979.
A. Konheim. Cryptography: a primer. Wiley, 1981.
C. Meyer. Ciphertext/plaintext and ciphertext/key dependence vs. number of rounds for the data encryption standard. In AFIPS Conference proceedings, 47, pages 1119–1126, 1978.
C. Mitchell. Enumerating boolean functions of cryptographic significance. Journal of Cryptology, 2(3):155–170, 1990.
D. S. Mitrinovic. Analytic Inequalities. Springer-Verlag, 1970.
L O’Connor. Enumerating nondegenerate permutations. Technical Report 2527, University of Waterloo, Waterloo, Ontario, Canada, 1991.
W. L. Price and D. W. Davies. Security for computer networks. Wiley, 1984.
R. A. Rueppel. Design and Analysis of Stream Ciphers. Springer-Verlag, 1986.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1991 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
O’Connor, L. (1991). Enumerating Nondegenerate Permutations. In: Davies, D.W. (eds) Advances in Cryptology — EUROCRYPT ’91. EUROCRYPT 1991. Lecture Notes in Computer Science, vol 547. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-46416-6_31
Download citation
DOI: https://doi.org/10.1007/3-540-46416-6_31
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-54620-7
Online ISBN: 978-3-540-46416-7
eBook Packages: Springer Book Archive