Abstract
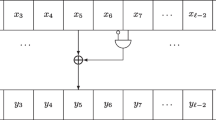
Techniques for fast exponentiation (multiplication) in various groups have been extensivelystudied for use in cryptographic primitives. Specifically, the coding of the exponent (multiplier) plays an important role in the performances of the algorithms used. The crucial optimization relies in general on minimizing the Hamming weight of the exponent (multiplier). This can be performed optimallywith nonadjacent representations. This paper introduces a compact encoding of non-adjacent representations that allows to skip the exponent recoding step. Furthermore, a straightforward technique for picking random numbers that alreadysatisfythe non-adjacence propertyis proposed. Several examples of application are given, in particular in the context of scalar multiplication on elliptic curves.
Some techniques presented in this paper are patent pending.
Chapter PDF
Similar content being viewed by others
References
W. Diffe and M. E. Hellman, “New directions in cryptography,” IEEE Trans. on Information Theory, vol. 22, pp. 644–654, 1976.
T. El Gamal, “A public key cryptosystem and a signature scheme based on discrete logarithms,” IEEE Trans. on Information Theory, vol. 31, pp. 469–472, 1985.
D. M. Gordon, “A surveyof fast exponentiation methods,” J. Algorithms, vol. 27, pp. 129–146, 1998.
4. IEEE Std P1363-2000, IEEE Standard Specifications for Public-Key Cryptography, IEEE Computer Society, August 20, 2000.
M. Joye and S.-M. Yen, “Optimal left-to-right binary signed-digit recoding,” IEEE Trans. Computers, vol. 49, pp. 740–748, 2000.
N. Koblitz, “CM-curves with good cryptographic properties,” Advances in Cryptology-CRYPTO’91, LNCS 576, pp. 279–287, Springer-Verlag, 1992.
W. Meier and O. Staffelbach, “Efficient multiplication on certain non-supersingular elliptic curves,” Advances in Cryptology-CRYPTO’92, LNCS 740, pp. 333–344, Springer-Verlag, 1993.
F. Morain and J. Olivos, “Speeding up the computations on an elliptic curve using addition-subtraction chains,” Theoretical Informatics and Applications, vol. 24, pp. 531–543, 1990.
P. Nguyen and J. Stern, “The hardness of the hidden subset sum problem and its cryptographic implications,” Advances in Cryptology-CRYPTO’99, LNCS 1666, pp. 31–46, Springer-Verlag, 1999.
A. Pinkus and S. Zafrany, Fourier Series and Integral Transforms, Cambridge UniversityPress, 1997.
G. W. Reitwiesner, “Binaryarithmetic,” Advances in Computers, vol. 1, pp. 231–308, 1960.
J. H. Silverman, The Arithmetic of Elliptic Curves, GTM 106, Springer-Verlag, 1986.
J. A. Solinas, “An improved algorithm for arithmetic on a familyof elliptic curves,” Advances in Cryptology-CRYPTO’97, LNCS 1294, pp. 357–371, Springer-Verlag, 1997.
J. H. van Lint, Introduction to Coding Theory, GTM 86, Springer-Verlag, 3rd edition, 1999.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2001 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Joye, M., Tymen, C. (2001). Compact Encoding of Non-adjacent Forms with Applications to Elliptic Curve Cryptography. In: Kim, K. (eds) Public Key Cryptography. PKC 2001. Lecture Notes in Computer Science, vol 1992. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-44586-2_26
Download citation
DOI: https://doi.org/10.1007/3-540-44586-2_26
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-41658-6
Online ISBN: 978-3-540-44586-9
eBook Packages: Springer Book Archive