Abstract
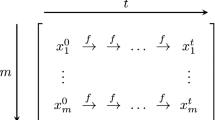
In 1980, Martin Hellman [1] introduced the concept of cryptanalytic time-memory tradeoffs, which allows the cryptanalysis of any N key symmetric cryptosystem in O(N 2/3) operations with O(N 2/3) storage, provided a precomputation of O(N) is performed beforehand. This procedure is well known but did not lead to realistic implementations. This paper considers a cryptanalytic time-memory tradeoff using distinguished points, a method referenced to Rivest [2]. The algorithm proposed decreases the expected number of memory accesses with sensible modifications of the other parameters and allows much more realistic implementations of fast key search machines.We present a detailed analysis of the algorithm and solve theoretical open problems of previous models. We also propose efficient mask functions in terms of hardware cost and probability of success. These results were experimentally confirmed and we used a purpose-built FPGA design to perform realistic tradeoffs against DES. The resulting online attack is feasible on a single PC and we recover a 40-bit key in about 10 seconds.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
M. Hellman, A Cryptanalytic Time-Memory Tradeoff, IEEE transactions on Information Theory, Vol 26, 1980, pp.401–406.
D. Denning, Cryptography and Data Security, p.100, Addison-Wesley, 1982, Out of Print.
J. Borst, B. Preneel and J. Vandewalle, On the Time-Memory Tradeoff Between exhaustive key search and table precomputation, Proc. of the 19th Symposium in Information Theory in the Benelux, WIC, 1998, pp.111–118.
J. Borst, B. Preneel and J. Vandewalle, A Time-Memory Tradeoff using Distinguished Points, Technical report ESAT-COSIC Report 98-1, Departement of Electrical Engineering, Katholieke Universiteit Leuven, 1998.
J. Borst, Block Ciphers: Design, Analysis and Side-Channel Analysis, Chapter 3: A Time-Memory Tradeoff attack, Phd Thesis, Departement of Electrical Engineering, Katholieke Universiteit Leuven, 2001.
J.J. Quisquater, F.X. Standaert, G. Rouvroy, J.P. David, J.D. Legat, A Cryptanalytic Time-Memory Tradeoff: First FPGA Implementation, To appear in the Proceedings of FPL 2002 (The Field Programmable Logic Conference).
K. Kusuda and T. Matsumoto, Optimization of Time-Memory Tradeoff Cryptanalysis and its Applications to DES, FEAL-32 and Skipjack, IEICE Transactions on Fundamentals of Electronics, Communications and Computer Science, EP79-A, 1996, pp.35–48.
S.D. Conte, C. de Boor, Elementary of Numerical Analysis, Chapter 8.4, Mc Graw-Hill, 1981.
Amos Fiat and Moni Naor, Rigorous Time/Space Tradeoffs for Inverting Functions, SIAM J. Computing 29(3), 1999 pp. 790–803.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2003 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Standaert, FX., Rouvroy, G., Quisquater, JJ., Legat, JD. (2003). A Time-Memory Tradeo. Using Distinguished Points: New Analysis & FPGA Results. In: Kaliski, B.S., Koç, ç.K., Paar, C. (eds) Cryptographic Hardware and Embedded Systems - CHES 2002. CHES 2002. Lecture Notes in Computer Science, vol 2523. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-36400-5_43
Download citation
DOI: https://doi.org/10.1007/3-540-36400-5_43
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-00409-7
Online ISBN: 978-3-540-36400-9
eBook Packages: Springer Book Archive