Abstract
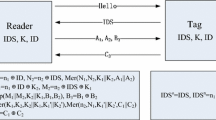
In this paper, we analyze the security of the RFID authentication protocol proposed by Choi et al. at SecUbiq 2005. They claimed that their protocol is secure against all possible threats considered in RFID systems. However, we show that the protocol is vulnerable to an impersonation attack. Moreover, an attacker is able to trace a tag by querying it twice, given the initial information from \(2^{\lceil(log_2(\ell+1)\rceil)}\) + 1( ≈ ℓ + 2) consecutive sessions and 2 · \(2^{\lceil log_2(\ell+1)\rceil}\) ( ≈ 2(ℓ + 1)) consecutive queries, where ℓ is the length of secret values (in binary).
Chapter PDF
Similar content being viewed by others
Keywords
- Pervasive Computing
- Impersonation Attack
- Ubiquitous Computing Environment
- Hash Operation
- Fair Exchange Protocol
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Avoine, G.: Cryptography in Radio Frequency Identification and Fair Exchange Protocols, PhD thesis, EPFL, Lausanne, Switzerland (December 2005)
Avoine, G., Oechslin, P.: A scalable and provably secure hash based RFID protocol. In: Workshop on Pervasive Computing and Communication Security (PerSec) 2005 (March 2005)
Choi, E.Y., Lee, S.M., Lee, D.H.: Efficient RFID Authentication Protocol for Ubiquitous Computing Environment. In: Enokido, T., Yan, L., Xiao, B., Kim, D.Y., Dai, Y.-S., Yang, L.T. (eds.) EUC-WS 2005, vol. 3823, pp. 945–954. Springer, Heidelberg (2005)
Dimitriou, T.: A lightweight RFID protocol to protect against traceability and cloning attacks. In: Conference on Security and Privacy for Emerging Areas in Communication Networks(SecureComm) 2005 (September 2005)
Henrici, D., Müller, P.: Hash-based enhancement of location privacy for radio-frequency identification devices using varying identifiers. In: Workshop on Pervasive Computing and Communication Security (PerSec) 2004 (March 2004)
Juels, A.: RFID Security and Privacy: A Research Survey, IEEE Journal on Selected Areas in Communications (to appear, 2006)
Juels, A., Rivest, R., Szydlo, M.: The blocker tag: Selective blocking of RFID tags for consumer privacy. In: Conference on Computer and Communications Security - CCS 2003, October 2003, pp. 103–111. ACM Press, New York (2003)
Lee, S.M., Hwang, Y.J., Lee, D.H., Lim, J.I.: Efficient Authenticaiton for Low-Cost RFID Systems. In: Gervasi, O., Gavrilova, M.L., Kumar, V., Laganá, A., Lee, H.P., Mun, Y., Taniar, D., Tan, C.J.K. (eds.) ICCSA 2005. LNCS, vol. 3480, pp. 619–627. Springer, Heidelberg (2005)
Ohkubo, M., Suzuki, K., Kinoshita, S.: Efficient hash-chain based RFID privacy protection scheme. In: International Conference on Ubiquitous Computing - Ubicomp, Workshop Privacy: Current Status and Future Directions (September 2004)
Rhee, K., Kwak, J., Kim, S., Won, D.: Challenge-response based RFID authentication protocol for distributed database environment. In: Hutter, D., Ullmann, M. (eds.) SPC 2005. LNCS, vol. 3450, pp. 70–84. Springer, Heidelberg (2005)
Weis, S.: Security and privacy in radio-fequency identification devices, Master thesis, Massachusetts Institute of Technology(MIT), Massachusetts, USA (May 2003)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Kwon, D., Han, D., Lee, J., Yeom, Y. (2006). Vulnerability of an RFID Authentication Protocol Proposed in at SecUbiq 2005. In: Zhou, X., et al. Emerging Directions in Embedded and Ubiquitous Computing. EUC 2006. Lecture Notes in Computer Science, vol 4097. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11807964_27
Download citation
DOI: https://doi.org/10.1007/11807964_27
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-36850-2
Online ISBN: 978-3-540-36851-9
eBook Packages: Computer ScienceComputer Science (R0)