Abstract
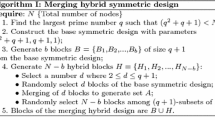
A novel key-update scheme is proposed for wireless sensor networks. The center server in a wireless sensor network first broadcasts a series of randomly generated code slices to sensor nodes. Upon receiving all the code slices, the sensor nodes find their neighboring coordinators to generate a permutation of slice numbers and send this permutation back to the center server. The center server and the sensor nodes can thus assemble a common program based on the permutation to derive their common key. Subsequent key-updates can then be done by this program based on the previous keys. The proposed scheme is simple, efficient, and is secure if the sensor nodes cannot be compromised within a short bound of time.
Chapter PDF
Similar content being viewed by others
References
Perrig, A., Szewczyk, R., Wen, V., Culler, D., Tygar, J.D.: SPINS: Security Protocols for Sensor Networks. In: The Seventh ACM Annual International Conference on Mobile Computing and Networking, pp. 189–199 (2001)
Price, A., Kosaka, K., Chatterjee, S.: A Key Pre-distribution Scheme for Wireless Sensor Networks. In: Wireless Telecommunications Symposium, pp. 253–260 (2005)
Stajano, E., Anderson, R.: The Resurrecting Duckling: Security Issues in Ad-Hoc Wireless Networks. In: The Seventh International Workshop on Security Protocols (1999)
Ramkumar, M., Memon, N., Simha, R.: Pre-Loaded Key Based Multicast and Broadcast Authentication in Mobile Ad-Hoc Networks. In: Globecom, San Fransisco, CA (2003)
Ramkumar, M., Memon, N.: On the Security of Random Key Predistribution Schemes. In: The Fifth Annual IEEE Information Assurance Workshop, NY (2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Wang, CL., Horng, G., Chen, YS., Hong, TP. (2006). An Efficient Key-Update Scheme for Wireless Sensor Networks. In: Alexandrov, V.N., van Albada, G.D., Sloot, P.M.A., Dongarra, J. (eds) Computational Science – ICCS 2006. ICCS 2006. Lecture Notes in Computer Science, vol 3991. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11758501_164
Download citation
DOI: https://doi.org/10.1007/11758501_164
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-34379-0
Online ISBN: 978-3-540-34380-6
eBook Packages: Computer ScienceComputer Science (R0)