Abstract
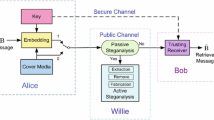
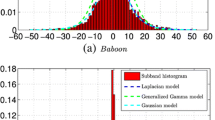
Development of digital communications systems significantly extended possibility to perform covert communications (steganography). This recalls an emerging demand in highly efficient counter-measures, i.e. steganalysis methods. Modern steganography is presented by a broad spectrum of various data-hiding techniques. Therefore development of corresponding steganalysis methods is rather a complex problem and challenging task. Moreover, in many practical steganalysis tasks second Kerckhoff’s principle is not applicable because of absence of information about the used steganography method. This motivates to use blind steganalysis, which can be applied to the certain techniques where one can specify at least statistics of the hidden data. This paper focuses on the class of supervised steganalysis techniques developed for the additive steganography, which can be described as y = f(x, s, K) = x + g(s, K), where stego image y is obtained from the cover image x by adding a low-amplitude cover image independent ((1 embedding also known as LSB matching) or cover image dependent (LSB embedding) stego signals that may be also depended on secret stego key K and the secret data s. The function g(.) represents the embedding rule.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2005 IFIP International Federation for Information Processing
About this paper
Cite this paper
Holotyak, T., Fridrich, J., Voloshynovskiy, S. (2005). Blind Statistical Steganalysis of Additive Steganography Using Wavelet Higher Order Statistics. In: Dittmann, J., Katzenbeisser, S., Uhl, A. (eds) Communications and Multimedia Security. CMS 2005. Lecture Notes in Computer Science, vol 3677. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11552055_31
Download citation
DOI: https://doi.org/10.1007/11552055_31
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-28791-9
Online ISBN: 978-3-540-31978-8
eBook Packages: Computer ScienceComputer Science (R0)