Abstract
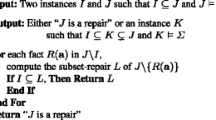
Controlled query evaluation preserves confidentiality in information systems at runtime. A security policy defines a set of potential secrets to be hidden from a certain user. Each time the user issues a query, a censor checks whether the correct answer would enable the user to infer any of those potential secrets. Given an incomplete information system, the following problem arises: Is it safe to admit that the database cannot provide an answer to a certain query because it lacks the requested information? We show that the answer needs to be refused more often than necessary at first glance, as otherwise the user would be able to make meta level inferences that would lead to a violation of the security policy. A maximally cooperative censor, which preserves confidentiality but only refuses the answer when absolutely necessary, is presented and analyzed.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Joachim Biskup and Piero A. Bonatti. Lying versus refusal for known potential secrets. Data & Knowledge Engineering, 38:199–222, 2001.
Joachim Biskup and Piero A. Bonatti. Confidentiality policies and their enforcement for controlled query evaluation. In Proc. of ESORICS 02, Zürich, Switzerland, October 14–16, 2002, volume 2502 of Lecture Notes in Computer Science, pages 39–54. Springer, 2002.
Joachim Biskup and Piero A. Bonatti. Controlled query evaluation for known policies by combining lying and refusal. In Proc. of FoIKS 02, Schloss Salzau, Germany, February 20–23, 2002, volume 2284 of Lecture Notes in Computer Science, pages 49–66. Springer, 2002.
Joachim Biskup and Piero A. Bonatti. Controlled query evaluation for enforcing confidentiality in complete information systems. To appear in International Journal of Information Security, 2004.
Joachim Biskup and Piero A. Bonatti. Controlled query evaluation for known policies by combining lying and refusal. Annals of Math. and Artificial Intelligence, 40:37–62, 2004.
P.A. Bonatti, S. Kraus, and V.S. Subrahmanian. Foundations of secure deductive databases. IEEE Transactions on Knowledge and Data Engineering, 7(3):406–422, 1995.
J. Chomicki and G. Saake, editors. Logics for Databases and Information Systems, chapter 10. Kluwer Academic Publishers, 1998.
George L. Sicherman, Wiebren de Jonge, and Reind P. van de Riet. Answering queries without revealing secrets. ACM Transactions on Database Systems, 8(1):41–59, 1983.
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2004 Springer Science + Business Media, Inc.
About this paper
Cite this paper
Biskup, J., Weibert, T. (2004). Refusal in Incomplete Databases. In: Farkas, C., Samarati, P. (eds) Research Directions in Data and Applications Security XVIII. IFIP International Federation for Information Processing, vol 144. Springer, Boston, MA. https://doi.org/10.1007/1-4020-8128-6_10
Download citation
DOI: https://doi.org/10.1007/1-4020-8128-6_10
Publisher Name: Springer, Boston, MA
Print ISBN: 978-1-4020-8127-9
Online ISBN: 978-1-4020-8128-6
eBook Packages: Springer Book Archive