Abstract
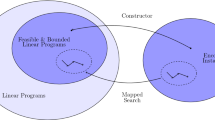
We consider the efficient generation of solved instances of computational problems. In particular, we consider invulnerable generators. Let S be a subset of 0,1* and M be a Turing Machine that accepts S; an accepting computation w of M on input x is called a “witness” that x ∈ S. Informally, a program is an α-invulnerable generator if, on input 1n, it produces instance-witness pairs <x, w>, with |x| = n, according to a distribution under which any polynomial-time adversary who is given x fails to find a witness that x ∈ S, with probability at least α, for infinitely many lengths n.
Research supported in part by NSF grant CCR-8810467.
Research supported by NSF grant CCR-8809174 and a Hewlett-Packard Corporation equipment grant.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
M. Blum and S. Micali. “How to Generate Cryptographically Strong Sequences of Pseudo-random Bits,” SIAM J. on Comput. (13), 1984, 850–864.
R. Boppana and R. Hirschfeld. “Pseudorandom Generators and Complexity Classes,” to appear in Advances in Computer Research, Silvio Micali (ed.), JAI Press (pub.), 1987.
G. Brassard and C. Crépeau. “Non-transitive Transfer of Confidence: A Perfect Zero-Knowledge Interactive Protocol for SAT and Beyond,” Proceedings of the 27th FOCS, IEEE, 1986, 188–195.
G. Brassard and C. Crépeau. “Zero-Knowledge Simulation of Boolean Circuits,” Advances in Cryptology — CRYPTO86 Proceedings, Andrew Odlyzko (ed.), Springer-Verlag (pub.), 1987, 223–233.
G. Brassard, D. Chaum, and C. Crépeau. “Minimum Disclosure Proofs of Knowledge,” to appear.
U. Feige, A. Fiat, and A. Shamir. “Zero Knowledge Proofs of Identity,” Proceedings of the 19th STOC, ACM, 1987, 210–217.
Z. Galil, S. Haber, and M. Yung. “Cryptographic Computation: Secure Fault-Tolerant Protocols and the Public-Key Model,” Advances in Crytology — CRYPTO87 Proceedings, Carl Pomerance (ed.), Springer-Verlag (pub.), 1988, 135–155.
M. Garey and D. Johnson. Computers and Intractability: A Guide to the Theory of NP-Completeness, Freeman, San Francisco, 1979.
S. Goldwasser and S. Micali. “Probabilistic Encryption,” JCSS (28), 1984, 270–299.
S. Goldwasser, S. Micali, and C. Rackoff. “The Knowledge Complexity of Interactive Proof Systems,” to appear in SIAM J. on Comput.
O. Goldreich, S. Micali, and A. Wigderson. “Proofs that Yield Nothing but their Validity and a Method of Cryptographic Protocol Design,” Proceedings of the 27 th FOCS, IEEE, 1986, 174–187.
Y. Gurevich. “Complete and Incomplete Randomized NP Problems,” Proceedings of the 28th FOCS, IEEE, 1987, 111–117.
J. Hartmanis. “Generalized Kolmogorov Complexity and the Structure of Feasible Computations,” Proceedings of the 24th FOCS, IEEE, 1983, 439–445.
M. Jerrum, L. Valiant, and V. Vazirani. “Random Generation of Combinatorial Structures from a Uniform Distribution,” TCS (43), 1986, 169–188.
D. Johnson. “The NP-Completeness Column, An Ongoing Guide,” JOA (5), 1984, 284–299.
J. Lagarias and A. Oldlyzko. “Solving Low-Density Subset Sum Problems,” JACM (32), 1985, 229–246.
L. Levin. “Average Case Complete Problems,” SIAM J. on Comput. (15), 1986, 285–286.
R. Rardin, C. Tovey, and M. Pilcher. “Polynomial Constructability and Traveling Salesman Problems of Intermediate Complexity,” ONR-URI Computational Combinatorics Report CC-88-2, Purdue University, November, 1988.
S. Rudich, private communication.
L. Sanchis and M. Fulk. “Efficient Language Instance Generation”, University of Rochester Computer Science Department TR 235, 1988.
L. Sanchis. “Test Instance Construction for NP-hard Problems,” University of Rochester Computer Science Department TR 206, 1987.
R. Venkatesan and L. Levin. “Random Instances of a Graph Coloring Problem axe Hard,” Proceedings of the 20th STOC, ACM, 1988, 217–222.
A. C. Yao. “Theory and Applications of Trapdoor Functions,” Proceedings of the 23rd FOCS, IEEE, 1982, 80–91.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1990 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Abadi, M., Allendert, E., Broder, A., Feigenbaum, J., Hemachandra, L.A. (1990). On Generating Solved Instances of Computational Problems. In: Goldwasser, S. (eds) Advances in Cryptology — CRYPTO’ 88. CRYPTO 1988. Lecture Notes in Computer Science, vol 403. Springer, New York, NY. https://doi.org/10.1007/0-387-34799-2_23
Download citation
DOI: https://doi.org/10.1007/0-387-34799-2_23
Published:
Publisher Name: Springer, New York, NY
Print ISBN: 978-0-387-97196-4
Online ISBN: 978-0-387-34799-8
eBook Packages: Springer Book Archive