Abstract
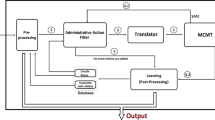
Avoiding unauthorized access in an information system usually means enforcing access control mechanisms. Traditional access control only aims at deciding if an access can be granted or not. Dynamic access control goes further as it aims at controlling also if an ongoing access is still authorized while it is running. Rights Expression Languages, such as MPEG-REL, take into account dynamic aspects of access control policy. However, existing access control architectures are not adequate to enforce such dynamic access control. In this paper, we first explain what dynamic access control involves and why existing architectures are not appropriate. We then provide a flexible and distributed architecture where different components interact to enforce dynamic access control. Using temporal logic of actions, we specify the different interactions between components in the architecture and specify more precisely the component in charge of giving the decision. Finally, we discuss about technical and security issues about how the architecture can be implemented to enable Digital Rights Management (DRM) applications.
This work was funded by the “ACI Sécurité Informatique: CASC Project”.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
G. Alonso, F. Casati, H. Kuno, and V. Machiraju. Web Services: Concepts, Architectures and Applications. Springer-Verlag, 2004.
Eberhard Becker, Willms Buhse, Dirk Gnnewig, and Niels Rump, editors. Digital Rights Management: Technological, Economic, Legal and Political Aspects. Springer-Verlag GmbH, 2003.
M. Blaze, J. Feigenbaum, and J. Lacy. Decentralized Trust Management. In The IEEE Symposium on Security and Privacy (SSP’96), Oakland, CA, May 1996.
C.T.A.M de Laat, G.M. Gross, L. Gomans, J.R. Vollbrecht, and D.W. Spence. Generic AAA architecture, RFC 2903. Technical report, IETF Internet Working Group, August 2000.
Thomas Erl. Service-oriented Architecture: Concepts, Technology, And Design. Prentice Hall PTR, 2005.
Susanne Guth. Digital Rights Management: Technological, Economic, Legal and Political Aspects, volume Volume 2770, chapter 2.3.5 Rights Expression Languages, pages 101–112. Springer-Verlag GmbH, 2003.
J.Y. Halpern and V. Weissman. Using First-Order Logic to Reason about policies. In 16th IEEE Computer Security Foundation Workshop (CSFW’03), Pacific Grove, California, June 2003.
J.Y. Halpern and V. Weissman. A Formal Foundation for XrML. In 17th IEEE Computer Security Foundation Workshop (CSFW’04), Pacific Grove, California, June 2004.
J. Hughes and E. Maler. Security Assertion Markup Language (SAML) Version 2.0. Technical report, OASIS, February 2005. www.oasis-open.org.
International Organization for Standardization (ISO). ISO/IEC 21000-5:2004 Information technology — Multimedia framework (MPEG-21) — Part 5: Rights Expression Language, 2004. www.iso.ch/iso/fr/prods-services/popstds/mpeg.html.
ISO International Organization for Standardization. Information technology — Open Systems Interconnection — Security Frameworks in Open Systems — Part 3:Access Control, ISO/IEC 10181-3. Technical report, ISO JTC 1, August 2001.
S. Jajodia, M. Kudo, and V.S. Subrahmanian. Provisional Authorizations. In A. Ghosh, editor, Security and Privacy in E-Commerce, pages 133–159, Athens, Greece, November 2000. Kluwer Academic Publishers.
L. Korba and S. Kenny. Applying Digital Rights Management Systems to Privacy Right Management. Journal of Computer and Security, 2002.
Leslie Lamport. Specifying Systems. Addison-Wesley Professional, July 2002.
Alexandra Miège. Definition of a formal framework for specifying security policies. The Or-BAC model and extensions. PhD thesis, ENST, 2005.
Tim Moses, eXtensible Access Control Markup Language (XACML) Version 2.0. Technical report, OASIS, February 2005. www.oasis-open.org.
J. Park and R. Sandhu. The UCON ABC Usage Control Model. ACM Transactions on Information and System Security, 7(1), February 2004.
Siani Pearson. Trusted Computing Platforms: TCPA Technology In Context. Prentice Hall PTR, July 2002.
J. Rosenberg and D. Remy. Securing Web Services With Ws-Security. Sams, 2004.
W. Rosenblatt, B. Rosenblatt, and W. Trippe. Digital Rights Management: Business and Technology. Wiley, Decembre 2001.
J. Zhou and D. Gollman. A fair non-repudiation protocol. In SP’ 96: Proceedings of the 1996 IEEE Symposium on Security and Privacy, page 55, Washington, DC, USA, 1996. IEEE Computer Society.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 International Federation for Information Processing
About this paper
Cite this paper
Sans, T., Cuppens, F., Cuppens-Boulahia, N. (2006). A Flexible and Distributed Architecture to Enforce Dynamic Access Control. In: Fischer-Hübner, S., Rannenberg, K., Yngström, L., Lindskog, S. (eds) Security and Privacy in Dynamic Environments. SEC 2006. IFIP International Federation for Information Processing, vol 201. Springer, Boston, MA. https://doi.org/10.1007/0-387-33406-8_16
Download citation
DOI: https://doi.org/10.1007/0-387-33406-8_16
Publisher Name: Springer, Boston, MA
Print ISBN: 978-0-387-33405-9
Online ISBN: 978-0-387-33406-6
eBook Packages: Computer ScienceComputer Science (R0)