Abstract
It was shown very recently in [1] that there are no multimedia digital fingerprinting codes capable of fully recovering a coalition of malicious users under the general linear attack and adversarial noise. We show that such codes exist if the class of attacks is narrowed to the averaging attack. The arising mathematical problem is close to the problem of constructing signature codes for a noisy binary adder channel.
Similar content being viewed by others
References
Fan, J., Gu, Y., Hachimori, M., and Miao, Y., Signature Codes for Weighted Binary Adder Channel and Multimedia Fingerprinting, IEEE Trans. Inform. Theory, 2020 (to appear).
Wagner, N.R., Fingerprinting, in Proc. 1983 IEEE Symp. on Security and Privacy, Oakland, CA, USA, Apr. 25–27, 1983, pp. 18–22.
Blakley, G.R., Meadows, C., and Purdy, G.B., Fingerprinting Long Forgiving Messages Advances in Cryptology—CRYPTO’85 (Proc. Conf. on the Theory and Application of Cryptographic Techniques, Santa Barbara, CA, USA, Aug. 18–22, 1985), Williams, H.C., Ed., Lect. Notes Comp. Sci., vol. 218, Berlin: Springer, 1986, pp. 180–189.
Chor, B., Fiat, A., and Naor, M., Tracing Traitors, Advances in Cryptology—CRYPTO’94 (Proc. 14th Annu. Int. Cryptology Conf., Santa Barbara, CA, Aug. 21–25, 1994), Desmedt, Y.G., Ed., Lect. Notes Comp. Sci., vol. 839, Berlin: Springer, 1994, pp. 257–270.
Hollmann, H.D.L., van Lint, J.H., Linnartz, J.-P., and Tolhuizen, L.M.G.M., On Codes with the Identifiable Parent Property, J. Combin. Theory Ser. A, 1998, vol. 82, no. 2, pp. 121–133.
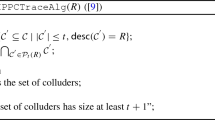
Boneh, D. and Shaw, J., Collusion-Secure Fingerprinting for Digital Data, IEEE Trans. Inform. Theory, 1998, vol. 44, no. 5, pp. 1897–1905.
Barg, A., Blakley, G.R. and Kabatiansky, G.A., Digital Fingerprinting Codes: Problem Statements, Constructions, Identification of Traitors, IEEE Trans. Inform. Theory, 2003, vol. 49, no. 4, pp. 852–865.
Tardos, G., Optimal Probabilistic Fingerprint Codes, in Proc. 35th Annu. ACM Symp. on Theory of Computing (STOC’03), San Diego, CA, June 9–11, 2003, pp. 116–125.
Trappe, W., Wu, M., Wang, Z.J., and Liu, K.J.R., Anti-Collusion Fingerprinting for Multimedia, IEEE Trans. Signal Process., 2003, vol. 51, no. 4, pp. 1069–1087.
Liu, K.J.R., Trappe, W., Wang, Z.J., Wu, M., and Zhao, H., Multimedia Fingerprinting Forensics for Traitor Tracing, Cairo, Egypt: Hindawi, 2005.
Chang, S.-C. and Wolf, J.K., On the T-User M-Frequency Noiseless Multiple-Access Channels with and without Intensity Information, IEEE Trans. Inform. Theory, 1981, vol. 27, no. 1, pp. 41–48.
Cheng, M. and Miao, Y., On Anti-Collusion Codes and Detection Algorithms for Multimedia Fingerprinting, IEEE Trans. Inform. Theory, 2011, vol. 57, no. 7, pp. 4843–4851.
Egorova, E., Fernandez, M., Kabatiansky, G., and Lee, M.H., Signature Codes for the A-Channel and Collusion-Secure Multimedia Fingerprinting Codes, in Proc. 2016 IEEE Int. Symp. on Information Theory (ISIT’2016), Barcelona, Spain, July 10–15, 2016, pp. 3043–3047.
Egorova, E., Fernandez, M., Kabatiansky, G. and Lee, M.H., Signature Codes for Weighted Noisy Adder Channel, Multimedia Fingerprinting and Compressed Sensing, Des. Codes Cryptogr., 2019, vol. 87, no. 2–3, pp. 455–462.
Györfi, L., Győri, S., Laczay, B., and Ruszinkó, M., Lectures on Multiple Access Channels, book draft, 2005. Available at http://www.szit.bme.hu/gyori/AFOSR_05/book.pdf.
D’yackov, A.G., On a Search Model of False Coins, Topics in Information Theory (Proc. 2nd Colloq. on Inf. Theory, Keszthely, Hungary, Aug. 25–30, 1975), Csiszár, I. and Elias, P., Eds., Colloq. Math. Soc. János Bolyai, vol. 16, Amsterdam: North-Holland, 1977, pp. 163–170.
MacWilliams, F.J. and Sloane, N.J.A., The Theory of Error-Correcting Codes, Amsterdam: North-Holland, 1977. Translated under the title Teoriya kodov, ispravlyayushchikh oshibki, Moscow: Svyaz’, 1979.
Kabatiansky, G., Fernandez, M., and Egorova, E., Multimedia Fingerprinting Codes Resistant against Colluders and Noise, in Proc. 8th IEEE Int. Workshop on Information Forensics and Security (WIFS’2016), Abu Dhabi, UAE, Dec. 4–7, 2016, pp. 1–5.
Ericson, T. and Levenshtein, V.I., Superimposed Codes in the Hamming Space, IEEE Trans. Inform. Theory, 1994, vol. 40, no. 6, pp. 1882–1893.
Vlǎduţ, S.G., Kabatiansky, G.A., and Lomakov, V.V., On Error Correction with Errors in Both the Channel and Syndrome, Probl. Peredachi Inf., 2015, vol. 51, no. 2, pp. 50–56 [Probl. Inf. Transm. (Engl. Transl.), 2015, vol. 51, no. 2, pp. 132–138].
Kautz, W.H. and Singleton, R.C., Nonrandom Binary Superimposed Codes, IEEE Trans. Inform. Theory, 1964, vol. 10, no. 4, pp. 363–377.
D’yachkov, A.G. and Rykov, V.V., Bounds on the Length of Disjunctive Codes, Probl. Peredachi Inf., 1982, vol. 18, no. 3, pp. 7–13 [Probl. Inf. Transm. (Engl. Transl.), 1982, vol. 18, no. 3, pp. 166–171].
Erdős, P., Frankl, P. and Füredi, Z., Families of Finite Sets in Which No Set Is Covered by the Union of Two Others, J. Combin. Theory Ser. A, 1982, vol. 33, no. 2, pp. 158–166.
Erdős, P., Frankl, P. and Füredi, Z., Families of Finite Sets in Which No Set Is Covered by the Union of r Others, Israel J. Math., 1985, vol. 51, no. 1–2, pp. 79–89.
Ericson, T. and Györfi, L., Superimposed Codes in \({{\mathbb{R}}}^{n}\), IEEE Trans. Inform. Theory, 1988, vol. 34, no. 4, pp. 877–880.
Füredi, Z. and Ruszinkó, M., An Improved Upper Bound of the Rate of Euclidean Superimposed Codes, IEEE Trans. Inform. Theory, 1999, vol. 45, no. 2, pp. 799–802.
Acknowledgments
The authors consider it a pleasant duty to express their gratitude to I.V. Vorob’ev for valuable discussions.
Funding
The research of E. Egorova and G. Kabatiabsky was supported in part by the Russian Foundation for Basic Research, project nos. 20-51-50007 and 20-07-00652. The research of M. Fernandez was supported by the Spanish Government Grant TCO-RISEBLOCK (PID2019-110224RB-I00) (MINECO/FEDER) and Catalan Government Grant 2017 SGR 782. The research of Y. Miao was supported by the Japan Society for the Promotion of Science (JSPS), research project JPJSBP120204802.
Author information
Authors and Affiliations
Rights and permissions
About this article
Cite this article
Egorova, E., Fernandez, M., Kabatiansky, G. et al. Existence and Construction of Complete Traceability Multimedia Fingerprinting Codes Resistant to Averaging Attack and Adversarial Noise. Probl Inf Transm 56, 388–398 (2020). https://doi.org/10.1134/S0032946020040080
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1134/S0032946020040080