Abstract
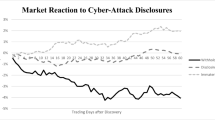
This paper adds to research on the effect of cyber events on the attacked firm’s value in light of conflicting results from previous studies. Using 536 cyberattack announcements that occurred during the 2007–2016 period, the main goal is to investigate for changes in investor reaction over time as cyberattacks have become more frequent. Empirical evidence shows that cumulative abnormal returns of attacked firms were volatile earlier in the period, became increasingly negative, but have moderated recently. This paper proposes and discusses potential explanations for this observed U-shaped pattern over the 10-year period. The relation between stock market reaction and type of attack, type of data affected, type of perpetrator and various firm level characteristics is also examined.

Similar content being viewed by others
Notes
The articles in the special issue investigate the management of IT risks by banks (Ashby et al. 2018), the perception of cyber risk by U.S. property casualty insurers (Pooser et al. 2018), the role of insurance in managing cyber risk, including the proposal of a cyber risk scoring tool (Shetty et al. 2018), and behavioural factors affecting perceptions of cyber risk by decision makers (de Smidt and Botzen 2018).
Following previous work, we use the daily value-weighted CRSP index to capture the market return Rm,t. Alternatively, using the daily equal-weighted index does not change the results.
The data type dummy variables for SSN, credit card information and personal information are not mutually exclusive since there are cases where all three of these types are affected and cases where none are.
The database is compiled from multiple sources of cyber-related incident records and carefully verified by the company’s research team. More importantly, Advisen Ltd. applies a rigorous quality assurance process, based both on pre-defined rules as well as manual examination to ensure a proper classification of these events. More information at https://www.advisenltd.com/data/cyber-loss-data/.
As suggested by previous studies, the following are considered confounding events: (1) mergers and acquisitions, (2) earnings/dividends announcements, (3) stock issuances and/or repurchases and (4) top executive changes.
To ensure our results of time-variant market reactions to cyber-related events are not affected by how we split the sample, we alternatively divide the sample into quartiles based on announcement dates and still find consistent evidence. These tests are available upon request.
We performed a rigorous check for confounding events for the shorter window used in the main part of this study. However, as in other long-horizon event studies, it is not practical to check for confounding events over long event windows. Therefore, the evidence reported in this analysis should be interpreted with caution. The same concern also applies to the buy-and-hold abnormal returns analysis reported in the later section.
References
Accenture. 2017. Cost of Cyber Crime Study. https://www.accenture.com/_acnmedia/PDF-62/Accenture-2017CostCybercrime-US-FINAL.pdf#zoom=50, Last accessed on 06/20/2018.
Acquisti, A., A. Friedman, and R. Telang. 2006. Is There A Cost to Privacy Breaches? An Event Study, ICIS 2006 Proceedings, 94. https://www.semanticscholar.org/paper/Is-There-a-Cost-to-Privacy-Breaches-An-Event-Study-Acquisti-Friedman/1a5d719687a6a0bdea269f54f25b121d509172d0.
Akey, P., S. Lewellen, and I. Liskovich. 2018. Hacking Corporate Reputations, Rotman School of Management Working Paper. https://ssrn.com/abstract=3143740.
Akey, P., V. Gregoire, and C. Martineau. 2020. Price Revelation from Insider Trading: Evidence from Hacked Earnings News, Rotman School of Management Working Paper. https://ssrn.com/abstract=3365024.
Amir, E., S. Levi, and T. Livne. 2018. Do Firms Underreport Information on Cyber-attacks? Evidence from Capital Markets. Review of Accounting Studies 23: 1177–1206.
Andriosopoulos, D., and S. Yang. 2015. The Impact Of Institutional Investors on Mergers and Acquisitions in The United Kingdom. Journal of Banking & Finance 50: 547–561.
Arcuri, M.C., M. Brogi, and G. Gandolfi. 2014. The Effect of Information Security Breaches on Stock Returns: Is the Cyber Crime a Threat to Firms? European Financial Management Meeting.
Ashby, S., T. Buck, S. Nöth-Zahn, and T. Peisl. 2018. Emerging IT Risks: Insights from German Banking. The Geneva Papers on Risk and Insurance: Issues and Practice 43 (2): 180–207.
Biener, C., M. Eling, and J.H. Wirfs. 2015. Insurability of Cyber Risk: An Empirical Analysis. The Geneva Papers on Risk and Insurance: Issues and Practice 40 (1): 131–158.
Böhme, R. 2005. Cyber-Insurance Revisited, WEIS. https://infosecon.net/workshop/pdf/15.pdf.
Bose, I., and A.C.M. Leung. 2014. Do Phishing Alerts Impact Global Corporations? A Firm Value Analysis. Decision Support Systems 64: 67–78.
Campbell, K., L.A. Gordon, M.P. Loeb, and L. Zhou. 2003. The Economic Cost of Publicly Announced Information Security Breaches: Empirical Evidence from the Stock Market. Journal of Computer Security 11 (3): 431–448.
Carhart, M. 1997. On Persistence in Mutual Fund Performance. The Journal of Finance 52 (1): 57–82.
Cavusoglu, H., B. Mishra, and S. Raghunathan. 2004. The Effect of Internet Security Breach Announcements on Market Value: Capital Market Reactions for Breached Firms and Internet Security Developers. International Journal of Electronic Commerce 9 (1): 70–104.
Chen, X., I. Bose, A.C.M. Leung, and C. Guo. 2011. Assessing the Severity of Phishing Attacks: A Hybrid Data Mining Approach. Decision Support Systems 50 (4): 662–672.
Das, S., A. Mukhopadhyay, and M. Anand. 2012. Stock Market Response to Information Security Breach: A Study Using Firm and Attack Characteristics. Journal of Information Privacy and Security 8 (4): 27–55.
De Smidt, G., and W. Botzen. 2018. Perceptions of Corporate Cyber Risks and Insurance Decision-Making. The Geneva Papers on Risk and Insurance: Issues and Practice 43 (2): 239–274.
Della Vigna, S., and J.M. Pollet. 2009. Investor Inattention and Friday Earnings Announcements. The Journal of Finance 64 (2): 709–749.
DeLong, G.L. 2001. Stockholder Gains from Focusing Versus Diversifying Bank Mergers. Journal of Financial Economics 59 (2): 221–252.
Eling, M. 2018. Cyber Risk and Cyber Risk Insurance: Status Quo and Future Research. The Geneva Papers on Risk and Insurance: Issues and Practice 43 (2): 175–179.
Eling, M., and N. Loperfido. 2017. Data Breaches: Goodness of Fit, Pricing, and Risk Measurement. Insurance: Mathematics and Economics 75: 126–136.
Fama, E.F., and K.R. French. 1996. Multifactor Explanations of Asset Pricing Anomalies. The Journal of Finance 51 (1): 55–84.
Finra. 2018. Report on Cybersecurirty Practices. https://www.finra.org/sites/default/files/p602363%20Report%20on%20Cybersecurity%20Practices_0.pdf, last accessed on 02/03/2020.
Forbes. 2014. Target Profit Falls 46% on Credit Card Breach and the Hits Could Keep on Coming. www.forbes.com/sites/maggiemcgrath/2014/02/26/target-profit-falls-46-on-credit-card-breach-and-says-the-hits-could-keep-on-coming/#4a0411827326, last accessed on 06/20/2018.
Garg, A., J. Curtis, and H. Halper. 2003. Quantifying the Financial Impact of IT Security Breaches. Information Management & Computer Security 11 (2): 74–83.
Gatzlaff, K.M., and K.A. McCullough. 2010. The Effect of Data Breaches on Shareholder Wealth. Risk Management and Insurance Review 13 (1): 61–83.
Gordon, L.A., M.P. Loeb, and L. Zhou. 2011. The Impact of Information Security Breaches: Has There Been a Downward Shift in Costs? Journal of Computer Security 19 (1): 33–56.
Greenwald, J. 2018. Stand-Alone, Package Cyber Premiums Jump: Fitch. https://www.businessinsurance.com/article/20180509/NEWS06/912321167/Stand-alone-package-cyber-premiums-jump-Fitch-Ratings#, last accessed on 06/20/2018.
Hinz, O., M. Nofer, D. Schiereck, and J. Trillig. 2015. The Influence of Data Theft on The Share Prices and Systematic Risk of Consumer Electronics Companies. Information & Management 52 (3): 337–347.
Hirshleifer, D., S.S. Lim, and S.H. Teoh. 2009. Driven to Distraction: Extraneous Events and Underreaction to Earnings News. The Journal of Finance 64 (5): 2289–2325.
Hovav, A., and J. D'Arcy. 2003. The Impact of Denial-of-Service Attack Announcements on The Market Value of Firms. Risk Management and Insurance Review 6 (2): 97–121.
Kamiya, S., J. Kang, J. Kim, A. Milidonis, and R. M. Stulz. 2018. What is the Impact of Successful Cyberattacks on Target Firms? Discussion paper, National Bureau of Economic Research. https://www.nber.org/papers/w24409.
Kannan, K., J. Rees, and S. Sridhar. 2007. Market Reactions to Information Security Breach Announcements: An Empirical Analysis. International Journal of Electronic Commerce 12 (1): 69–91.
Kvochko, E., and R. Pant. 2015. Why Data Breaches Don’t Hurt Stock Prices. Harvard Business Review 5: 2–5.
Luo, Y. 2005. Do Insiders Learn from Outsiders? Evidence from Mergers and Acquisitions. The Journal of Finance 60 (4): 1951–1982.
Makridis, C., and B. Dean. 2018. Measuring the Economic Effects of Data Breaches on Firm Outcomes: Challenges and Opportunities. Journal of Economic and Social Measurement 43: 59–83.
Malhotra, A., and C. Kubowicz Malhotra. 2011. Evaluating Customer Information Breaches as Service Failures: An Event Study Approach. Journal of Service Research 14 (1): 44–59.
Marketwatch. 2020. Cybersecurity Market Global Growth, Opportunities, Industry Analysis & Forecast to 2024. https://www.marketwatch.com/press-release/cybersecurity-market-global-growth-opportunities-industry-analysis-forecast-to-2024-2020-04-23?tesla=y, last accessed on 04/29/2020.
Marotta, A., and M. McShane. 2018. Integrating a Proactive Technique into a Holistic Cyber Risk Management Approach. Risk Management and Insurance Review 21 (3): 435–452.
McAfee. 2018. The Economic Impact of Cybercrime—No Slowing Down. www.mcafee.com/us/resources/reports/rp-economic-impact-cybercrime-summary.pdf, last accessed on 06/20/2018.
Modi, S.B., M.A. Wiles, and S. Mishra. 2015. Shareholder Value Implications of Service Failures in Triads: The Case of Customer Information Security Breaches. Journal of Operations Management 35: 21–39.
Morse, E.A., V. Raval, and J.R. Wingender Jr. 2011. Market Price Effects of Data Security Breaches. Information Security Journal: A Global Perspective 20 (6): 263–273.
Ogut, H., N. Menon, and S. Raghunathan. 2005. Cyber Insurance and IT Security Investment: Impact of Interdependence Risk, WEIS. https://www.semanticscholar.org/paper/Cyber-Insurance-and-IT-Security-Investment%3A-Impact-Ogut-Menon/7780a75c68604ca979d0fe8896ebc998ae6a02fc.
Patel, N. 2010. The Effect of IT Hack Announcements on the Market Value of Publicly Traded Corporations. Duke Journal of Economics 22: 10.
Pirounias, S., D. Mermigas, and C. Patsakis. 2014. The Relation Between Information Security Events and Firm Market Value Empirical Evidence on Recent Disclosures: An Extension of the GLZ Study. Journal of Information Security and Applications 19 (4–5): 257–271.
Pooser, D.M., M.J. Browne, and O. Arkhangelska. 2018. Growth in the Perception of Cyber Risk: Evidence from US P&C Insurers. The Geneva Papers on Risk and Insurance: Issues and Practice 43 (2): 208–223.
Ricci, O. 2015. The Impact of Monetary Policy Announcements on the Stock Price of Large European Banks During the Financial Crisis. Journal of Banking & Finance 52: 245–255.
Rosati, P., M. Cummins, P. Deeney, F. Gogolin, L. van der Werff, and T. Lynn. 2017. The Effect of Data Breach Announcements Beyond the Stock Price: Empirical Evidence on Market Activity. International Review of Financial Analysis 49: 146–154.
Sharpe, W.F. 1964. Capital Asset Prices: A Theory of Market Equilibrium under Conditions of Risk. The Journal of Finance 19 (3): 425–442.
Shetty, S., M. McShane, L. Zhang, J.P. Kesan, C.A. Kamhoua, K. Kwiat, and L.L. Njilla. 2018. Reducing Informational Disadvantages to Improve Cyber Risk Management. The Geneva Papers on Risk and Insurance: Issues and Practice 43 (2): 224–238.
Spanos, G., and L. Angelis. 2016. The Impact of Information Security Events to the Stock Market: A Systematic Literature Review. Computers & Security 58: 216–229.
Statista, 2019, Share of organizations with cyber liability insurance worldwide 2011–2018. https://www.statista.com/statistics/422463/ownership-of-cyber-liability-insurance/#statisticContainer, last accessed on 02/03/2020.
Tabuchi, H., 2018, 2017 Set a Record for Losses From Natural Disasters. It Could Get Worse. https://www.nytimes.com/2018/01/04/climate/losses-natural-disasters-insurance.html, last accessed on 06/20/2018.
The Geneva Association. 2016. Ten Key Questions on Cyber Risk and Cyber Risk Insurance. Authors: Martin Eling, Werner Schnell and Fabian Sommerrock. December. https://www.genevaassociation.org/media/954708/cyber-risk-10-key-questions.pdf.
Yayla, A.A., and Q. Hu. 2011. The Impact of Information Security Events on the Stock Value of Firms: The Effect of Contingency Factors. Journal of Information Technology 26 (1): 60–77.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
McShane, M., Nguyen, T. Time-varying effects of cyberattacks on firm value. Geneva Pap Risk Insur Issues Pract 45, 580–615 (2020). https://doi.org/10.1057/s41288-020-00170-x
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1057/s41288-020-00170-x