Abstract
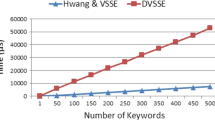
The advantages of cloud computing encourage individuals and enterprises to outsource their local data storage and computation to cloud server, however, data security and privacy concerns seriously hinder the practicability of cloud storage. Although searchable encryption (SE) technique enables cloud server to provide fundamental encrypted data retrieval services for data-owners, equipping with a result verification mechanism is still of prime importance in practice as semi-trusted cloud server may return incorrect search results. Besides, single keyword search inevitably incurs many irrelevant results which result in waste of bandwidth and computation resources. In this paper, we are among the first to tackle the problems of data-owner updating and result verification simultaneously. To this end, we devise an efficient cryptographic primitive called as verifiable multi-keyword search over encrypted cloud data for dynamic data-owner scheme to protect both data confidentiality and integrity. Rigorous security analysis proves that our scheme is secure against keyword guessing attack (KGA) in standard model. As a further contribution, the empirical experiments over real-world dataset show that our scheme is efficient and feasible in practical applications.








Similar content being viewed by others
References
Khalil I, Khreishah A, Azeem M (2014) Cloud computing security: a survey. Computers 3(1):1–35
Wei L F, Zhu H J, Cao Z F, Dong X L, Jia W W, Chen Y L, Vasilakos A (2014) Security and privacy for storage and computation in cloud computing. Inf Sci 258:371–386
Wei L F, Zhu H J, Cao Z F, Jia W W, Vasilakos A (2010) Seccloud: Bridging Secure Storage and Computation in Cloud. IEEE International Conference on Distributed Computing Systems Workshops. IEEE:52–61
Boneh D, Crescenzo G D, Ostrovsky R, Persiano G (2004) Public key encryption with keyword search. International Conference on the Theory and Applications of Cryptographic Techniques. Springer, pp 506–522
Li H W, Liu D X, Dai Y S, Luan T H (2015) Engineering searchable encryption of mobile cloud networks: when QoE meets QoP. IEEE Wirel Commun 22(4):74–80
Chai Q, Gong G (2012) Verifiable symmetric searchable encryption for semi-honest-but-curious cloud servers. IEEE International Conference on Communications. IEEE:917–922
Hsien W F, Yang C C, Hwang M S (2016) A survey of public auditing for secure data storage in cloud computing. I J Network Security 18(1):133–142
Ren Y J, Shen J, Wang J, Han J, Lee S Y (2015) Mutual verifiable provable data auditing in public cloud storage. J Internet Tech 16(2):317–323
Song D X, Wagner D, Perrig A (2000) Practical techniques for searches on encrypted data. IEEE Symposium on Security and Privacy. IEEE:44–55
Miao Y B, Ma J F, Liu Z Q (2016) Revocable and anonymous searchable encryption in multi-user setting. Concurrency and Computation: Practice and Experience 28(4):1204–1218
Xia Z H, Wang X H, Sun X M, Wang Q (2016) A secure and dynamic Multi-Keyword ranked search scheme over encrypted cloud data. IEEE Trans Parallel Distrib Syst 27(2):340–352
Miao Y B, Liu J, Ma J F (2015) Fine-grained searchable encryption over encrypted data in multi-clouds. IEEE International Conference on Wireless Algorithms, Systems, and Applications. IEEE:407–416
Fu Z J, Ren K, Shu J G, Sun X M, Huang F X (2015) Enabling Personalized Search over Encrypted Outsourced Data with Efficiency Improvement. IEEE Transactions on Parallel and Distributed Systems
Li J, Wang Q, Wang C, Cao N, Ren K, Lou W J (2010) Fuzzy keyword search over encrypted data in cloud computing. IEEE International Conference on Computer Communications. IEEE:441–445
Wang C, Cao N, Ren K, Lou W J (2012) Enabling Secure and Efficient Ranked Keyword Search over Outsourced Cloud data. IEEE Trans Parallel Distrib Syst 23(8):1467–1479
Fu Z J, Sun X M, Liu Q, Zhou L, Shu J G (2015) Achieving efficient cloud search services: multi-keyword ranked search over encrypted cloud data supporting parallel computing. IEICE Trans 98-B(1):190–200
Boneh D, Waters B (2007) Conjunctive, subset, and range queries on encrypted data. International Conference on Theory of Cryptography. Springer, pp 535–554
Hwang Y H, Lee P J (2007) Public key encryption with conjunctive keyword search and its extension to a multi-user system. International Conference on Theory of Cryptography. Springer, pp 2–22
Lee C C, Hsu S T, Hwang M S (2013) A study of conjunctive keyword searchable schemes. I J Network Security 15(5):321–330
Li H W, Yang Y, Luan T H, Liang X H, Zhou l, Shen X M (2015) Enabling Fine-Grained Multi-keyword Search Supporting Classified Subdictionaries over Encrypted Cloud Data. IEEE Transactions on Dependable and Secure Computing. doi:10.1009/tdsc.2015.2406704
Golle P, Staddon J, Waters B (2004) Secure conjunctive keyword search over encrypted data. IEEE International Conference on Applied Cryptography and Network Security. IEEE:31–45
Zheng Q J, Xu S H, Ateniese G (2014) VABKS: Verifiable Attribute-based keyword search over outsourced encrypted data. IEEE International Conference on Computer Communications. IEEE:522–530
Sun W H, Yu S C, Lou W J, Hou Y T, Li H (2016) Protecting your right: verifiable attribute-based keyword search with fine-grained owner-enforced search authorization in the cloud. IEEE Trans Parallel Distrib Syst 27(4):1187–1198
Goyal V, Pandey O, Sahai A, Waters B (2006) Attribute-based encryption for fine-grained access control of encrypted data. ACM Conference on Computer and Communications Security. ACM:89–98
Bethencourt J, Sahai A, Waters B (2007) Ciphertext-policy attribute-based encryption. IEEE Symposium on Security and Privacy. IEEE:321–334
Waters B (2011) Ciphertext-policy attribute-based encryption: an expressive, efficient, and provably secure realization. International Conference on Practice and Theory in Public Key Cryptography. Springer, pp 53–70
Sun W H, Liu X F, Lou W J, Hou Y T, Li H (2015) Catch you if you lie to me: efficient verifiable conjunctive keyword search over large dynamic encrypted cloud data. IEEE International Conference on Computer Communications. IEEE:2110–2118
Miao Y B, Ma J F, Wei F S, Liu Z Q, Wang X A, Lu C B (2016) VCSE: Verfiable Conjunctive Keywords Search over Encrypted Data without Secure-channel. Peer-to-Peer Networking and Applications. doi:10.1007/s12083-016-0458-z
Shao J, Cao Z F, Liang X H, Lin H (2010) Proxy re-encryption with keyword search. Inf Sci 180 (13):2576–2587
Fang L M, Susilo W, Ge C P, Wang J D (2012) Chosen-ciphertext secure anonymous conditional proxy re-encryption with keyword search. Theor Comput Sci 462:39–58
Wang X A, Huang X Y, Yang X Y, Liu L F, Wu X G (2012) Further observation on proxy re-encryption with keyword search. J Syst Softw 85(3):643–654
Guo L F, Lu B, Li X Y, Xu H (2013) A verifiable proxy re-encryption with keyword search without random oracle. IEEE International Conference on Computational Intelligence and Security. IEEE:474–478
Yang Y, Ma M D (2016) Conjunctive keyword search with designated tester and timing enabled proxy re-encryption function for e-health clouds. IEEE Trans Inf Forensics Secur 11(4):746–759
Hu C Y, Liu P T (2011) A secure searchable public key encryption scheme with a designated tester against keyword guessing attacks and its extension. IEEE International Conference on Advances in Computer Science, Environment, Ecoinformatics, and Education. IEEE:131–136
Rhee H S, Park J H, Lee D H (2012) Generic construction of designated tester public-key encryption with keyword search. Inf Sci 205:93–109
Yau W C, Phan R C, Heng S H, Goi B M (2013) Keyword guessing attacks on secure searchable public key encryption schemes with a designated tester. Int J Comput Math 90(12):2581–2587
Yang Y (2012) A communication efficient group key distribution scheme for mANETs. IEEE International Conference on Network and System Security. IEEE:361–372
Wang B Y, Li B C, Li H (2014) Oruta: privacy-preserving public auditingfor shared data in the cloud. IEEE Trans Cloud Computing 2(1):43–56
Acknowledgments
This work was supported by the National High Technology Research and Development Program (863 Program) (No. 2015AA016007, No. 2015AA017203), the Key Program of NSFC (No. U1405255, No. U1135002), the Changjiang Scholars and Innovation Research Team in University (No. IRT1078), the Fundamental Research Funds for the Center Universities (No. JY10000903001) and the Major Nature Science Foundation of China (No. 61370078, No. 61309016).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Miao, Y., Ma, J., Liu, X. et al. VMKDO: Verifiable multi-keyword search over encrypted cloud data for dynamic data-owner. Peer-to-Peer Netw. Appl. 11, 287–297 (2018). https://doi.org/10.1007/s12083-016-0487-7
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12083-016-0487-7