Abstract
This paper is a comprehensive survey on the role of swarm intelligence in wireless communication networks. The main aim of preparing this paper is to lead the way for the researchers in the field of wireless networks to recognize the role of swarm intelligence in optimizing the network features. The research paths are divided into four main tracks which are: network routing, network quality of service, network congestion, and network security. Swarm intelligence involves a wide range of applications but in this paper, we are focusing on its adaptability with the communication networks to accomplish performance optimization. In each of the four tracks, three standards-based networks are examined to show the effect of swarm intelligence on these networks which are IEEE 802.11, IEEE 802.16, and IEEE 802.20. At the end of each section, a graphical qualitative comparison is represented to show the performance differences in terms of network optimization.



































Similar content being viewed by others
References
Kurose, J. F., & Ross, K. W. (2001). Computer networking: A top-down approach featuring the internet. Boston: Addison-Wesley.
Qadir, J., Yau, K. A., Imran, M. A., Ni, Q., & Vasilakos, A. V. (2015). IEEE access special section editorial: Artificial intelligence enabled networking. IEEE Access, 3, 3079–3082.
Stallings, W. (2004). Wireless communications and networks (2nd ed.). Upper Saddle River: Prentice-Hall Inc.
Gu, G., & Luo, J. (2006). Some issues on computer networks: architecture and key technologies. Journal of Computer Science and Technology, 21, 708.
Brunette, E. S., Flemmer, R. C., & Flemmer, C. L. (2009). A review of artificial intelligence. In 4th International conference on Autonomous Robots and Agents, Wellington (pp. 385–392).
Kumoye, A. O., Prasad, R., & Fonkam, M. (2020). Swarm intelligence algorithm and its application: A critical review. In International conference in mathematics, computer engineering and computer science (ICMCECS), Ayobo, Ipaja, Lagos, Nigeria.
Bai, H., & Zhao, B. (2006). A survey on application of swarm intelligence computation to electric power system. In 2006 6th World congress on intelligent control and automation, Dalian (pp. 7587–7591).
Sigeti, P., & Oravec, M., & Pavlovičová, J. (2013). Some aspects of QoS in wireless networks. In Proceedings ELMAR-2013, Zadar (pp. 173–176).
Baojian, Z., & Kunhua, Z. (2009). Research on congestion control in networks based on chaos theory. In International conference on computer and communications security, Hong Kong (pp. 32–35).
Yan, F., Jian-Wen, Y., & Lin, C. (2015). Computer network security and technology research. In Seventh international conference on measuring technology and mechatronics automation, Nanchang (pp. 293–296).
AL-Mousawi, A. J., & AL-Hassani, M. H. (2018). A survey in wireless sensor network for explosives detection. Computers & Electrical Engineering, 72, 682–701.
Muruganantham, N., & El-Ocla, H. (2020). Routing using genetic algorithm in a wireless sensor network. Wireless Personal Communications, 111, 2703–2732.
Bhoskar, M. T., Kulkarni, M. O. K., Kulkarni, M. N. K., Patekar, M. S. L., Kakandikar, G. M., & Nandedkar, V. M. (2015). Genetic algorithm and its applications to mechanical engineering: A review, materials today. Proceedings, 2(45), 2624–2630.
McCall, J. (2005). Genetic algorithms for modelling and optimisation. Journal of Computational and Applied Mathematics, 184(1), 205–222.
Al-Mousawi, A. J. (2019). Evolutionary intelligence in wireless sensor network: Routing, clustering, localization, and coverage. Wireless Networks.
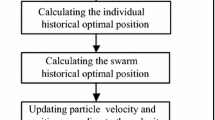
Yang, X., Chen, X., Xia, R., & Qian, Z. (2018). Wireless sensor network congestion control based on standard particle swarm optimization and single neuron PID. Sensors, 18, 1265.
Clerc, M., & Kennedy, J. (2002). The particle swarm-explosion, stability and convergence in a multidimensional complex space. IEEE Transactions on Evolutionary Computation, 6(1), 58–73.
Kennedy, J. (2002). Bare bones particle swarms. In Proceedings of the IEEE swarm intelligence symposium (pp. 80–87). Piscataway, NJ: IEEE Press.
Kennedy, J. (2006). Swarm intelligence. In A. Y. Zomaya (Ed.), Handbook of nature-inspired and innovative computing: integrating classical models with emerging technologies (pp. 187–219). New York: Springer.
Sharma, S., & Nidhi. (2019). Vehicular ad-hoc network: An overview. In 2019 International conference on computing, communication, and intelligent systems (ICCCIS), Greater Noida, India (pp. 131–134).
Karabulut, M. A., Shahen Shah, A. F. M. & Ilhan, H. (2019). Performance optimization by using artificial neural network algorithms in VANETs. In 2019 42nd International conference on telecommunications and signal processing (TSP), Budapest, Hungary (pp. 633–636).
Jain, M., & Saxena, R. (2017). Overview of VANET: Requirements and its routing protocols. In 2017 International conference on communication and signal processing (ICCSP), Chennai (pp. 1957–1961).
Gao, W., Liu, S., & Huang, L. (2012). A global best artificial bee colony algorithm for global optimization. Journal of Computational and Applied Mathematics, 236(11), 2741–2753.
Linh, N. T., & Anh, N. Q. (2010). Application artificial bee colony algorithm (ABC) for reconfiguring distribution network. In Second international conference on computer modeling and simulation.
Nozohour-leilabady, B., & Fazelabdolabadi, B. (2016). On the application of artificial bee colony (ABC) algorithm for optimization of well placements in fractured reservoirs; efficiency comparison with the particle swarm optimization (PSO) methodology. Petroleum, 2(1), 79–89.
Karaboga, D. (2005). An idea based on honey bee swarm for numerical optimization. Technical Report TR06, Erciyes University, Engineering Faculty, Computer Engineering Department.
Domínguez, O. C. (2009). An adaptation of the scout bee behavior in the Artificial Bee Colony algorithm to solve constrained optimization problems. Laboratorio Nacional de Informática Avanzada (LANIA), MsC, Thesis, Supervisor, Efrén Mezura-Montes.
Karaboga, D., Basturk, B., & Ozturk, C. (2007). Artificial bee colony (ABC) optimization algorithm for training feed-forward neural networks. In Modeling decisions for artificial intelligence, volume 4617/2007 of LNCS (pp. 318–319). Berlin: Springer.
Smith, S. C., Hammell, R. J., Parker, T. W. & Marvel, L. M. (2014). A theoretical exploration of the impact of packet loss on network intrusion detection. In 15th IEEE/ACIS international conference on software engineering, artificial intelligence, networking and parallel/distributed computing (SNPD), Las Vegas, NV (pp. 1–6).
Al-Maslamani, N., & Abdallah, M. (2020). Malicious node detection in wireless sensor network using swarm intelligence optimization. In 2020 IEEE international conference on informatics, IoT, and enabling technologies (ICIoT), Doha, Qatar (pp. 219–224).
Djenna, A., & Saïdouni, D. E. (2018). Cyber attacks classification in IoT-based-healthcare infrastructure. In 2nd Cyber security in networking conference (CSNet), Paris (pp. 1–4).
Kheyrihassankandi, J., Singh, Y. P., & Ho, C. K. (2012). A hybrid adaptive routing algorithm for mobile WiMAX using swarm intelligence. In 2012 International conference on computer and communication engineering (ICCCE), Kuala Lumpur (pp. 402–407).
Kamali, B. (2018). The IEEE 802.16 standards and the WiMAX technology. In AeroMACS: An IEEE 802.16 standard-based technology for the next generation of air transportation systems (pp. 189–258). IEEE.
Genc, V., Murphy, S., Yu, Y., & Murphy, J. (2008). IEEE 802.16J relay-based wireless access networks: An overview. IEEE Wireless Communications, 15(5), 56–63.
Shen, G., Liu, J., Wang, D., Wang, J., & Jin, S. (2009). Multi-hop relay for next-generation wireless access networks. Bell Labs Technical Journal, 13(4), 175–193.
Yonghua, Z., Jin, Z., Wentong, Y., & Yong, C. (2011). The advanced ant colony algorithm and its application. In Third international conference on measuring technology and mechatronics automation, Shangshai (pp. 664–667).
Cui, S., & Han, S. (2013). Ant colony algorithm and its application in solving the traveling salesman problem. In Third international conference on instrumentation, measurement, computer, communication and control, Shenyang (pp. 1200–1203).
Wei, W., Yi, M., Feng, Y., & Lei, Z. (2011). Application of individual differences ant colony algorithm in transmission network expansion planning. In 2011 International conference on electric information and control engineering, Wuhan (pp. 4798–4802).
Long, F., & Sun, F. (2006). An improved ant colony algorithm and its application in routing computation of satellite networks. In The proceedings of the multiconference on "computational engineering in systems applications", Beijing (pp. 1567–1573).
Caro, D., & Dorigo, M. (1998). AntNet: Distributed stigmergetic control for communications networks. Journal of Artificial Intelligence Research, 9, 317–365.
Dorigo, M., & Blum, C. (2005). Ant colony optimization theory: A survey. Theoretical Computer Science, 344(2–3), 243–278.
Dorigo, M., & Stützle, T. (2005). Ant colony optimization. Cambridge, MA: MIT Press.
Chandra Mohan, B., & Baskaran, R. (2012). A survey: Ant colony optimization based recent research and implementation on several engineering domain. Expert Systems with Applications, 39(4), 4618–4627.
Karaboga, D., & Akay, B. (2009). a comparative study of artificial bee colony algorithm. Applied Mathematics and Computation, 214(1), 108–132.
Suliman, I. A., & Abdalla, G. M. T. (2016). Comparative study of wireless LAN using OPNET and NS-2. In Conference of basic sciences and engineering studies (SGCAC), Khartoum (pp. 196–200).
Sureshkumar, A., Ellappan, V., & Manivel, K. (2017). A comparison analysis of DSDV and AODV routing protocols in mobile AD HOC networks. In Conference on emerging devices and smart systems (ICEDSS), Tiruchengode (pp. 234–237)
Dosciatti, E. R., & Foronda, A. (2015). Time frame optimization using PSO to guarantee QoS in IEEE 802.16 networks. In 2015 Science and information conference (SAI), London (pp. 506–513).
Tang, T. W., Green, D., Rumsewicz, M., & Bean, N. (2007). An architecture for IEEE 802.16 MAC scheduler design. In 2007 15th IEEE international conference on networks, Adelaide, SA (pp. 89–94).
IEEE Standard for Air Interface for Broadband Wireless Access Systems. IEEE Std 802.16–2012 (Revision of IEEE Std 802.16–2009), 2012, pp. 1–2542.
Zhang, J., Li, W., Cui, D., Zhao X, & Yin, Z. (2009). The NS2-based simulation and research on wireless sensor network route protocol. In 2009 5th International conference on wireless communications, networking and mobile computing, Beijing (pp. 1–4).
Son, P., Satria, M., & Kang, A. (2019). A new method for congestion avoidance in wireless mesh networks. Journal of Physics: Conference Series., 1192, 012062. https://doi.org/10.1088/1742-6596/1192/1/012062.
Anuj, G., Harsh, S., & Anil, V. (2012). Computation of pheromone values in AntNet algorithm. International Journal of Computer Network & Information Security., 4, 47–54. https://doi.org/10.5815/ijcnis.
Ranjana, V. (2014). Optimization with congestion aware routing in mesh topology topology. IJREAT International Journal of Research in Engineering & Advanced Technology, 2(2), 2014.
Negoita, M. G. (2007). Artificial immune systems—An emergent technology performing the defence of complex systems. In 2007 ECSIS symposium on bio-inspired, learning, and intelligent systems for security (BLISS 2007), Edinburgh (pp. 145–150).
Dasgupta, D. (2006). Advances in artificial immune systems. IEEE Computational Intelligence Magazine, 1(4), 40–49.
Mohammed, A. (2014). A study on IEEE 802.16 (WiMAX) and its security issues. International Journal of Advanced Technology & Engineering Research, 2250–3536, 55–62.
Mehrafrooz, R., Vahid, A., & Mohsen, S. Z. (2018). Intrusion detection against DDoS attack in WiMAX network by artificial immune system. International Journal of Computer Applications Technology and Research, 07, 175–184. https://doi.org/10.7753/IJCATR0704.1004.
Zhou, B. (2011). An intrusion detection system based on WiMAX. In Proceedings of 2011 international conference on computer science and network technology, Harbin (pp. 2448–2451).
Kim, Y., Lim, H., & Bahk, S. (2008). Shared authentication information for preventing DDoS attacks in mobile WiMAX networks. In 5th IEEE consumer communications and networking conference, Las Vegas, NV (pp. 765–769).
EshghiShargh, A. (2009). Using artificial immune system on implementation of intrusion detection systems. In Third UKSim European symposium on computer modeling and simulation, Athens (pp. 164–168).
Idris, I., & Selamat, A. (2011). Negative selection algorithm in artificial immune system for spam detection. In Malaysian conference in software engineering, Johor Bahru (pp. 379–382).
Bolton, W., Xiao, Y., & Guizani, M. (2005). IEEE 80220: Mobile broadband wireless access. IEEE Wireless Communications, 14(1), 84–95.
Saad, M., & Muhaureq, S. (2011). Joint routing and radio resource management in multihop cellular networks using particle swarm optimization. Intelligent Automation & Soft Computing, 17(1), 61–70.
Ng, T. C., & Yu, W. (2007). Joint optimization of relay strategies and resource allocations in cooperative cellular networks. IEEE Journal on Selected Areas in Communications, 25(2), 328–339.
Shoukath, K., & Sampath, P. (2019). Particle swarm optimization-based power allocation for Alamouti amplify and forward relaying protocol. International Journal of Communication Systems. https://doi.org/10.1002/dac.3954.
Benyamina, D., Hafid, A., & Gendreau, M. (2011). Throughput gateways-congestion trade-off in designing multi-radio wireless networks. Mobile Network Application, 16, 109–121.
Datta, R., & Marchang, N. (2012). Chapter 7—Security for mobile ad hoc networks. In S. K. Das, K. Kant, N. Zhang (Eds.), Handbook on securing cyber-physical critical infrastructure (pp. 147–190). Morgan Kaufmann. ISBN 9780124158153.
Mazhar, N., & Farooq, M. (2007). BeeAIS: Artificial immune system security for nature inspired, MANET routing protocol, BeeAdHoc. In L. N. de Castro, F. J. Von Zuben, H. Knidel (Eds.), Artificial immune systems. ICARIS 2007. Lecture notes in computer science (Vol. 4628). Berlin: Springer.
Rao, P. C. S., Jana, P. K., & Banka, H. (2016). A particle swarm optimization based energy efficient cluster head selection algorithm for wireless sensor networks. Wireless Networks, 23, 2005–2020.
Srinivasa Rao, P. C., & Banka, H. (2017). Energy-efficient clustering algorithms for wireless sensor networks: Novel chemical reaction optimization approach. Wireless Networks, 23, 433–452.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Human and animal rights
This article does not contain any studies with human participants or animals performed by any of the authors.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Al-Mousawi, A.J. Wireless communication networks and swarm intelligence. Wireless Netw 27, 1755–1782 (2021). https://doi.org/10.1007/s11276-021-02545-x
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11276-021-02545-x