Abstract
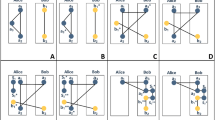
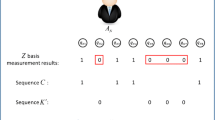
In many circumstances, a shared key is needed to realize secure communication. Based on quantum mechanics principles, quantum key agreement (QKA) is a good method to establish a shared key by every party’s fair participation. In this paper, we propose a novel three-party QKA protocol, which is designed by using Greenberger–Horne–Zeilinger (GHZ) states. To realize the protocol, the distributor of the GHZ states needs only one quantum communication with the other two parties, respectively, and everyone performs single-particle measurements simply. Then, we extend the three-party QKA protocol to arbitrary multiparty situation. At last, we discuss the security and fairness of the multiparty protocol. It shows that the new scheme is secure and fair to every participant.


Similar content being viewed by others
References
Diffie, W., Hellman, M.: New direction in cryptography. IEEE Trans. Inf. Theory 22, 644–654 (1976)
Ingemarsson, I., Tang, D.T., Wong, C.K.: A conference key distribution system. IEEE Trans. Inf. Theory 28, 714–719 (1982)
Steiner, M., Tsudik, G., Waidner, M.: Key agreement in dynamic peer groups. IEEE Trans. Parallel Distrib. Syst. 11, 769–780 (2000)
Mitchell, C.J., Ward, M., Wilson, P.: Key control in key agreement protocols. Electron. Lett. 34(10), 980–981 (1998)
Ateniese, G., Steiner, M., Tsudik, G.: New multiparty authentication services and key agreement protocols. IEEE J. Sel. Areas Commun. 18(4), 628–639 (2000)
Wang, T.Y., Wen, Q.Y., Chen, X.B.: Cryptanalysis and improvement of a multi-user quantum key distribution protocol. Opt. Commun. 283(24), 5261–5263 (2010)
Salas, P.J.: Security of plug-and-play QKD arrangements with finite resources. Quantum Inf. Comput. 13(9–10), 861–879 (2013)
Deng, F.G., Long, G.L., Liu, X.S.: Two-step quantum direct communication protocol using the Einstein-Podolsky-Rosen pairblock. Phys. Rev. A 68, 042317 (2003)
Qin, S.J., Gao, F., Wen, Q.Y., et al.: Improving the security of multiparty quantum secret sharing against an attack with a fake signal. Phys. Lett. A 357, 101–103 (2006)
Gao, F., Guo, F.Z., Wen, Q.Y., et al.: Quantum key distribution without alternative measurements and rotations. Phys. Lett. A 349, 53 (2006)
Long, G.L., Liu, X.S.: Theoretically efficient high capacity quantum key distribution scheme. Phys. Rev. A 65, 032302 (2002)
Boström, K., Felbinger, T.: Deterministic secure direct communication using entanglement. Phys. Rev. Lett. 89, 187902 (2002)
Deng, F.G., Long, G.L.: Secure direct communication with a quantum one-time pad. Phys. Rev. A 69, 052319 (2004)
Gao, F., Qin, S.J., Wen, Q.Y., Zhu, F.C.: Cryptanalysis of multiparty controlled quantum secure direct communication using Greenberger-Horn-Zeilinger state. Opt. Commun. 283, 192–195 (2010)
Huang, W., Zuo, H.J., Li, Y.B.: Cryptanalysis and improvement of a multi-user quantum communication network using type entangled states. Int. J. Theor. Phys. 52, 1354–1361 (2013)
Lin, S., Wen, Q.Y., Zhu, F.C.: Quantum secure direct communication with \(\chi \)-type entangled states. Phy. Rev. A 78, 064304 (2008)
Tseng, H.Y., Lin, J., Hwang, T.: New quantum private comparison protocol using EPR pairs. Quantum Inf. Process. 11, 373–384 (2011)
Liu, W., Wang, Y.B., Jiang, Z.T.: An efficient protocol for the quantum private comparison of equality with W state. Opt. commun. 284, 3160–3163 (2011)
Martini, F.D., Giovannetti, V., Lloyd, S., Maccone, L., et al.: Experimental quantum private queries with linear optics. Phys. Rev. A 80, 010302 (2009)
Jakobi, M., Simon, C., Gisin, N., Bancal, J.D., et al.: Practical private database queries based on a quantum-key-distribution protocol. Phys. Rev. A 83, 022301 (2011)
Zeng, G.H., Keitel, C.H.: An arbitrated quantum signature algorithm. Phys. Rev. A 65, 042312 (2002)
Lee, H., Hong, C.H., Kim, H., et al.: Arbitrated quantum signature scheme with message recovery. Phys. Rev. A 321, 295–300 (2004)
Wen, X.J., Niu, X.M., Ji, L.P.: A weak blind signature scheme based on quantum cryptography. Opt. Commun. 282, 666–669 (2009)
Wang, T.Y., Wen, Q.Y.: Fair quantum blind signatures. Chin. Phys. B 19, 060307–060311 (2010)
Wen, X.J., Tian, Y., Niu, X.M.: A group signature scheme based on quantum teleportation. Phys. Scr. 81, 055001–055006 (2010)
Liu, F., Qin, S.J., Su, Q.: An arbitrated quantum signature scheme with fast signing and verifying. Quantum Inf. Process. 13, 491–502 (2014)
Zhou, N., Zeng, G., Xiong, J.: Quantum key agreement protocol. Electron. Lett. 40, 1149–1150 (2004)
Tsai, C., Hwang, T.: On quantum key agreement protocol. Technical Report, C-S-I-E, NCKU, Taiwan, ROC (2009)
Chong, S.K., Tsai, C.W., Hwang, T.: Improvement on “quantum key agreement protocol with maximally entangled states”. Int. J. Theor. Phys. 50(6), 1793–1802 (2011)
Hsuch, C.C., Chen, C.Y.: Quantum key agreement protocol with maximally entangled states. In: Proceedings of the 14th Information Security Conference (ISC 2004), pp. 236–242. Nation Taiwan University of Science and Technology, Taipei, Taiwan, 10–11 June (2004).
Tsai, C.W., Chong, S.K., Hwang, T.: Comment on quantum key agreement protocol with maximally entangled states. In: Proceedings of the 20th Cryptology and Information Security Conference, pp. 210–213. National Chiao Tung University, Hsinchu, Taiwan, 27–28 May (2010).
Shi, R.H., Zhong, H.: Multi-party quantum key agreement with bell states and bell measurements. Quantum Inf. Process. 12, 921–932 (2013)
Liu, B., Gao, F., Huang, W., Wen, Q.Y.: Multiparty quantum key agreement with single particles. Quantum Inf. Process. 12, 1797–1805 (2013)
Huang, W., Wen, Q.Y., Liu, B., Gao, F., Sun, Y.: Quantum key agreement with EPR pairs and Single-particle measurements. Quantum Inf. Process. 13, 649–663 (2014)
Nguyen, B.A.: Quantum exam. Phys. Lett. A 350, 174 (2006)
Gao, F., Wen, Q.Y., Zhu, F.C.: Comment on: “Quantum exam”[Phys. Lett. A, 2006, (350):174]. Phys. Lett. A 360, 748–750 (2007)
Song, J., Zhang, S.: Comment on: “Quantum exam”[Phys. Lett. A, 2006, (350): 174]. Phys. Lett. A 360, 746–747 (2007)
Acknowledgments
This work is supported by NSFC (Grant Nos. 61300181, 61272057, 61202434, 61170270, 61100203, 61121061 and 61201431), Beijing Natural Science Foundation (Grant No. 4122054) and Beijing Higher Education Young Elite Teacher Project (Grant Nos. YETP0475 and YETP0477).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Xu, GB., Wen, QY., Gao, F. et al. Novel multiparty quantum key agreement protocol with GHZ states. Quantum Inf Process 13, 2587–2594 (2014). https://doi.org/10.1007/s11128-014-0816-9
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11128-014-0816-9