Abstract
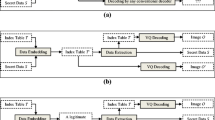
Data hiding is a technique for secret and secure data storing and transmission that embeds data into a media such as an image, audio, video and so on, with minimal quality degradation of the media. Some developed data hiding schemes are reversible. Reversibility property allows the media to be recovered completely after extraction of the embedded data. Vector Quantization (VQ)-based image data hiding is one of the most popular study areas in the literature. However, most VQ-based reversible data hiding schemes generate non-legitimate codes as output. In other words output codes generated by such schemes could not be decoded by the conventional VQ or VQ based decoders and may arouse the attention of interceptors. On the other hand, the existing VQ based reversible data hiding schemes that generate legitimate VQ codes as output, suffer from low capacity and poor quality of stego-image. In this paper a novel reversible data hiding scheme for VQ-compressed images based on locally adaptive data compression scheme (LAS) is proposed. Unlike other schemes, the proposed scheme doesn’t change the VQ indices; data is embedded by choosing one of the possible ways to encode each index. As a result, in comparison with the schemes that embed data by index replacement, in the proposed scheme no extra distortion is made by data embedding and the outputted codes are compatible with the conventional LAS decoder. These properties help to hide the existence of secret data and make the scheme suitable for steganography. Moreover, a framework to combine the proposed scheme with some other schemes to improve their capacity and embedding side information is proposed. Since LAS is a general data compression scheme, the proposed scheme could be used to embed data into any data formats. All existing LAS based data hiding schemes produce non-legitimate codes as their outputs and the proposed scheme is the first and only one that produces legitimate codes as output. Experimental results show that the proposed scheme outperforms the existing LAS based schemes and some other VQ based data hiding schemes. On average, the proposed scheme embeds 2.14 bits per index with almost the same bit-rate as the bit-rate of the VQ index table.






Similar content being viewed by others
References
Bentley, J. L., Sleator, D. D., Tarjan, R. E., & Wei, V. K. (1986). A locally adaptive data compression scheme. Communications of the ACM, 29(4), 320–330. doi:10.1145/5684.5688.
Chang, C. C., Sung, C. H., & Chen, T. S. (1997). A locally adaptive scheme for image index compression. In Proceedings of the 1997 Conference on Computer Vision, Graphics, and Image Processing, Taichung,Taiwan, 1997, (pp. 93–99).
Chang, C. C., Tai, W. L., & Lin, C. C. (2006). A reversible data hiding scheme based on side match vector quantization. IEEE Transactions on Circuits and Systems for Video Technology, 16(10), 1301–1308. doi:10.1109/TCSVT.2006.882380.
Chang, C. C., & Lin, C. Y. (2006). Reversible steganography for VQ-compressed images using side matching and relocation. IEEE Transactions on Information Forensics and Security, 1(4), 493–501. doi:10.1109/TIFS.2006.885034.
Chang, C. C., Hsieh, Y. P., & Lin, C. Y. (2007a). Lossless data embedding with high embedding capacity based on declustering for VQ-compressed codes. IEEE Transactions on Information Forensics and Security, 2(3), 341–349. doi:10.1109/TIFS.2007.902683.
Chang, C. C., Lin, C. C., Tseng, C. S., & Tai, W. L. (2007b). Reversible hiding in DCT-based compressed images. Information Sciences, 177(13), 2768–2786. doi:10.1016/j.ins.2007.02.019.
Chang, C. C., Kieu, T. D., & Chou, Y. C. (2009). Reversible information hiding for VQ indices based on locally adaptive coding. Journal of Visual Communication and Image Representation, 20(1), 57–64. doi:10.1016/j.jvcir.2008.08.005.
Chang, C. C., Nguyen, T. S., & Lin, C. C. (2011). A reversible data hiding scheme for VQ indices using locally adaptive coding. Journal of Visual Communication and Image Representation, 22(7), 664–672. doi:10.1016/j.jvcir.2011.06.005.
Chang, C. C., Lin, C. Y., & Hsieh, Y. P. (2012). Data hiding for vector quantization images using mixed-base notation and dissimilar patterns without loss of fidelity. Information Sciences, 201, 70–79. doi:10.1016/j.ins.2011.12.025.
Chang, C. C., Chen, K. N., Wang, Z. H., & Li, M. C. (2013). Lossless information hiding in the VQ index table. Journal of Software, 8(3), 547–553. doi:10.4304/jsw.8.3.547-553.
Chen, W. J., & Huang, W. T. (2009). VQ indexes compression and information hiding using hybrid lossless index coding. Digital Signal Processing, 19(3), 433–443. doi:10.1016/j.dsp.2008.11.003.
Chiang, Y. K., & Tsai, P. (2008). Steganography using overlapping codebook partition. Signal Processing, 88(5), 1203–1215. doi:10.1016/j.sigpro.2007.11.009.
Du, W. C., & Hsu, W. J. (2003). Adaptive data hiding based on VQ compressed images. IEE Proceedings on Vision, Image and Signal Processing, 150(4), 233–238. doi:10.1049/ip-vis:20030525.
Gray, R. M. (1984). Vector quantization. IEEE Acoustics, Speech and Signal Processing Magazine, 1(2), 4–29. doi:10.1109/MASSP.1984.1162229.
Hsieh, C. H., & Tsai, J. C. (1996). Lossless compression of VQ index with search-order coding. IEEE Transactions on Image Processing, 5(11), 1579–1582. doi:10.1109/83.541428.
Jo, M., & Kim, H. D. (2002). A digital image watermarking scheme based on vector quantization. IEICE Transactions on Information and Systems, E85–D(6), 1054–1056.
Kim, T. (1992). Side match and overlap match vector quantizers for images. IEEE Transactions on Image Processing, 1(2), 170–185. doi:10.1109/83.136594.
Lee, S., Yoo, C. D., & Kalker, T. (2007). Reversible image watermarking based on integer-to-integer wavelet transform. IEEE Transactions on Information Forensics and Security, 2(3), 321–330. doi:10.1109/TIFS.2007.905146.
Lee, C. F., Chen, H. L., & Lai, S. H. (2010). An adaptive data hiding scheme with high embedding capacity and visual image quality based on SMVQ prediction through classification codebooks. Image and Vision Computing, 28(8), 1293–1302. doi:10.1016/j.imavis.2010.01.006.
Lee, J. D., Chiou, Y. H., & Guo, J. M. (2013). Lossless data hiding for VQ indices based on neighboring correlation. Information Sciences, 221, 419–438. doi:10.1016/j.ins.2012.09.020.
Lin, C. C., Chen, S. C., & Hsueh, N. L. (2009). Adaptive embedding techniques for VQ-compressed images. Information Sciences, 179(1–2), 140–149. doi:10.1016/j.ins.2008.09.001.
Linde, Y., Buzo, A., & Gray, R. M. (1980). An algorithm for vector quantizer design. IEEE Transactions on Communications, 28(1), 84–95. doi:10.1109/TCOM.1980.1094577.
Lu, Z. M., Wang, J. X., & Liu, B. B. (2009). An improved lossless data hiding scheme based on image VQ-index residual value coding. Journal of Systems and Software, 82(6), 1016–1024. doi:10.1016/j.jss.2009.01.010.
Ni, Z., Shi, Y. Q., Ansari, N., & Su, W. (2006). Reversible data hiding. IEEE Transactions on Circuits and Systems for Video Technology, 16(3), 354–362. doi:10.1109/TCSVT.2006.869964.
Pan, Z., Ma, X., Deng, X., & Hu, S. (2013). Low bit-rate information hiding method based on search-order-coding technique. Journal of Systems and Software, 86(11), 2863–2869. doi:10.1016/j.jss.2013.06.066.
Qin, C., Chang, C. C., & Chen, Y. C. (2013). Efficient reversible data hiding for VQ-compressed images based on index mapping mechanism. Signal Processing, 93(9), 2687–2695. doi:10.1016/j.sigpro.2013.03.036.
Rahmani, P., & Dastghaibyfard, G. (2012). Reversible data hiding for VQ-compressed images based on an index replacement technique. International Journal of Computer and Electrical Engineering, 4(3), 359–362.
Rahmani, P., & Dastghaibyfard, G. (2014). A low distortion reversible data hiding scheme for search order coding of VQ indices. Multimedia Tools and Applications. doi:10.1007/s11042-014-2200-2.
Rahmani, P., Dastghaibyfard, G., & Rahmani, E. (2011b). A reversible data embedding scheme based on search order coding for VQ index tables. In Proceedings of 8th International ISC Conference on Information Security and Cryptography, Mashhad, Iran, 2011, (pp. 79–82), doi:10.1109/ISCISC.2011.6062332.
Rahmani, P., Rahmani, E., & Dastghaibyfard, G. (2011a). A location map free reversible data hiding scheme for VQ-compressed images based on search order coding. In Proceedings of Seventh International Conference on Intelligent Information Hiding and Multimedia Signal Processing, Dalian, China, 2011, (pp. 189–192). doi:10.1109/IIHMSP.2011.75.
Shen, J. J., & Ren, J. M. (2010). A robust associative watermarking technique based on vector quantization. Digital Signal Processing, 20(5), 1408–1423. doi:10.1016/j.dsp.2009.10.015.
Shie, S. C., & Lin, S. D. (2009). Data hiding based on compressed VQ indices of images. Computer Standards & Interfaces, 31(6), 1143–1149. doi:10.1016/j.csi.2008.12.003.
Tian, J. (2003). Reversible data embedding using a difference expansion. IEEE Transactions on Circuits and Systems for Video Technology, 13(8), 890–896. doi:10.1109/TCSVT.2003.815962.
Tsai, Y. S., & Tsai, P. (2011). Adaptive data hiding for vector quantization images based on overlapping codeword clustering. Information Sciences, 181(15), 3188–3198. doi:10.1016/j.ins.2011.03.017.
Wang, F. H., Jain, L. C., & Pan, J. S. (2007). VQ-based watermarking scheme with genetic codebook partition. Journal of Network and Computer Applications, 30(1), 4–23. doi:10.1016/j.jnca.2005.08.002.
Wang, J. X., & Lu, Z. M. (2009). A path optional lossless data hiding scheme based on VQ joint neighboring coding. Information Sciences, 179(19), 3332–3348. doi:10.1016/j.ins.2009.05.021.
Wang, W. J., Huang, C. T., Liu, C. M., Su, P. C., & Wang, S. J. (2013). Data embedding for vector quantization image processing on the basis of adjoining state-codebook mapping. Information Sciences, 246, 69–82. doi:10.1016/j.ins.2013.05.007.
Yang, C. H., & Lin, Y. C. (2009). Reversible data hiding of a VQ index table based on referred counts. Journal of Visual Communication and Image Representation, 20(6), 399–407. doi:10.1016/j.jvcir.2009.04.001.
Yang, C. H., & Lin, Y. C. (2010). Fractal curves to improve the reversible data embedding for VQ-indexes based on locally adaptive coding. Journal of Visual Communication and Image Representation, 21(4), 334–342. doi:10.1016/j.jvcir.2010.02.008.
Yang, C. H., Wang, W. J., Huang, C. T., & Wang, S. J. (2011a). Reversible steganography based on side match and hit pattern for VQ-compressed images. Information Sciences, 181(11), 2218–2230. doi:10.1016/j.ins.2011.01.015.
Yang, C. H., Wu, S. C., Huang, S. C., & Lin, Y. K. (2011b). Huffman-code strategies to improve MFCVQ-based reversible data hiding for VQ indexes. Journal of Systems and Software, 84(3), 388–396. doi:10.1016/j.jss.2010.11.924.
Yue, S., Wang, Z. H., & Chang, C. C. (2013). An image data hiding scheme based on vector quantization and graph coloring. Recent Advances in Information Hiding and Applications, 40, 1–17. doi:10.1007/978-3-642-28580-6_1.
Zhang, X., & Wang, S. (2005). Steganography using multiple-base notational system and human vision sensitivity. IEEE Signal Processing Letters, 12(1), 67–70. doi:10.1109/LSP.2004.838214.
Acknowledgments
The authors would say thanks to Prof. C. H. Yang and Mr Y. C. Lin for their help and support. Also the authors thank Mr Lucas Helms for proofreading the paper.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Rahmani, P., Norouzzadeh, M.S. & Dastghaibyfard, G. A novel legitimacy preserving data hiding scheme based on LAS compressed code of VQ index tables. Multidim Syst Sign Process 27, 433–452 (2016). https://doi.org/10.1007/s11045-014-0309-0
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11045-014-0309-0