Abstract
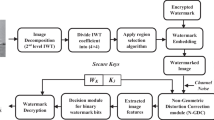
This paper is aimed to address the issue of ownership rights of digital data like images and audio signals. This is achieved by inserting a perceptually transparent unique digital pattern in the digital host signal. The digital pattern is generated by a methodical fusion of features extracted from iris image and fingerprint image. The fusion is done in such a way that the individual templates can be later decomposed from the digital pattern and can be used for identification. The pattern is optimized to a size which has acceptable payload under the perceptual transparency constraints of design requirements. The embedding is done using the singular value decomposition method for the audio signals and using discrete cosine transform method for the images. The recovered pattern is subjected to decomposition to individual templates, i.e. fingerprint and iris templates which were subjected to unique identification tests. Experimental results indicate that the embedding of the digital tag in the image or audio do not tamper the perceptual transparency and is also robust to signal processing attacks. The SNR of the watermarked signal is very good and the BER and Normalized correlation of the extracted watermark are very encouraging. The templates which were decomposed from the extracted digital watermark were mapped for unique identification even under serious attacks. Use of two biometric features for generating a digital watermark is a novel attempt for accurate identification of ownership of the digital data as these biometric features will be unique for every subject and hence this can be considered as a significant development towards digital right management (DRM) control.












Similar content being viewed by others
References
Agarwal H, Raman B, Venkat I (2014) Blind reliable invisible watermarking method in wavelet domain for face image watermark. Multimed Tools Appl, Springer Sci 1–39
Al-yaman MS, Al-Taee MA, Shahrour AT, Al-husseini IA (2011) Biometric based audio ownership verification using discrete wavelet transform and SVD techniques. 8th Int Multi-Conf Syst Signals Devices (SSD) 1–5
Casia-irisv3, nst. of Automation, Chinese Academy of Sciences (2006) http://www.cbsr.ia.ac.cn/IrisDatabase.htm
Charfeddine M, El’arbi M, Amar CB (2014) A new DCT audio watermarking scheme based on preliminary MP3 study. Multimedia Tools and Applications, Springer Verlag, 70(3):1521–1557
Chen M, Chen Z, Zeng X, Xiong Z (2010) Model order selection in reversible image watermarking. Sel Top Signal Process IEEE J. 4(3):592–604. doi: 10.1109/JSTSP.2010.2049222
Daugman J (1993) High confidence visual recognition of persons by a test of statistical independence. IEEE Trans Pattern Anal Mach Intell 15(11)
Daugman J (2002) How iris recognition works. Proc 2002 Int Conf Image Process 1
Dutta MK, Gupta P, Pathak VK (2009) Blind watermarking in audio signals using biometric features in wavelet domain. Int Conf IEEE Region 10, TENCON, 1–5
Dutta MK, Gupta P, Pathak VK (2009) Biometric based unique key generation for audio watermarking. Int Conf Pattern Recog Mach Intell LNCS 5909:458–463
Dutta MK, Gupta P, Pathak VK (2010) Audio watermarking using pseudorandom sequences based on biometric templates. J Comput 5(3):372–379
Dutta MK, Singh A, Burget R, Attasi H, Choudhary A, Soni KM (2013) Generation of biometric based unique digital watermark from iris image. 36th IEEE Int Conf Telecommun Signal Process , Rome, Italy 685–689
Dutta MK, Singh A, Soni KM, Burget R, Riha K (2013) Watermark generation from fingerprint features for digital right management control. 36th IEEE International Conference on Telecommunications and Signal Processing, Rome, Italy 717–721
Dutta MK, Singh A, Soni KM (2014) A secure algorithm for biometric-based digital image watermarking in DCT domain. Int J Comput Vis Robot (IJCVR) 4(1/2)
Dutta MK, Singh A, Zia TA (2013) An efficient and secure digital image watermarking using features from iris image. Int Conf Control Commun Comput (ICCC) 451–456
Katzenbeisser S, Petitcolas FAP ed (2000) Information hiding techniques for steganography and digital watermarking. Artech House, Inc
Khalili M, Asatryan D (2013) Colour spaces effects on improved discrete wavelet transform-based digital image watermarking using Arnold transform map. Signal Process, IET 7(3):177–187. doi:10.1049/iet-spr.2012.0380
Kirovski D, Malvar HS (2003) Spread-spectrum watermarking of audio signals. IEEE Trans Signal Process 51(4):1020–1033
Kishore Kumar NK, Sheeba VS (2012) Blind biometric watermarking based on contourlet transform. Third Int Conf Comput Commun Netw Technol (ICCCNT) 1–6
Lai C-C, Tsai C-C (2010) Digital image watermarking using discrete wavelet transform and singular value decomposition. IEEE Trans Instrum Meas 59(11):3060–3063
Li Z, Yap K-H, Lei B-Y (2011) A new blind robust image watermarking scheme in SVD-DCT composite domain. Image Process (ICIP), 2011 18th IEEE International Conference on 2757–2760, 11–14. doi: 10.1109/ICIP.2011.6116241
Ma B, Wang Y, Li C, Zhang Z, Huang D (2014) Secure multimodal biometric authentication with wavelet quantization based fingerprint watermarking. Multimed Tools Appl, Springer Sci 637–666
Majumder S, Devi KJ, Sarkar SK (2013) Singular value decomposition and wavelet-based iris biometric watermarking. Biometrics, IET. 2(1):21–27. doi:10.1049/iet-bmt.2012.0052
Maltoni D, Maio D, Jain AK, Prabhakar S (2009) Handbook of fingerprint recognition. Springer Professional Computing, 2nd edition
Masek L, Kovesi P, thesis on “Recognition of Human Iris Patterns for Biometric Identification” http://www.csse.uwa.edu.au/~pk/studentprojects/libor/LiborMasek Thesis.pdf
MK Dutta, P Gupta, Pathak VK (2014) A perceptible watermarking algorithm for audio signals. Multimedia Tools and Applications, Springer Verlag 73(2):691–713
Rao NN, Thrimurthy P, Babu BR (2009) An efficient copyright protection scheme for digital images using biometrics and watermarking. 2nd IEEE Int Conf Comput Sci Inf Technol 69–74
Ratha N, Connell JH, Bolle RM (2001) An analysis of minutiae matching strength. In: Proc. Audio and Video-based Biometric Person Authentication (AVBPA), 223–228, (Halmstad, Sweden)
Shaw AK, Majumder S, Sarkar S, Sarkar SK (2013) A novel EMD based watermarking of fingerprint biometric using GEP. First Int Conf Comput Intell: Model Tech Appl (CIMTA) 10:172–183
Wang D-S, Li J-P, Yan Y-H (2008) A novel authentication scheme of the DRM system based on multimodal biometric verification and watermarking technique. Int Conf Apperceiving Comput Intell Anal 212–215
Xiang S, Kim HJ, Huang J (2008) Invariant image watermarking based on statistical features in the low-frequency domain. IEEE Trans Circ Syst Video Technol 18(6):777–790
Zhang F, Liu W, Lin W, Ngi Ngan K (2011) Spread spectrum image watermarking based on perceptual quality metric. Image Process, IEEE Trans 20(11):3207–3218. doi:10.1109/TIP.2011.2146263
Zhang X, Qian Z, Ren Y, Feng G (2011) Watermarking with flexible self-recovery quality based on compressive sensing and compositive reconstruction. IEEE Trans Inf Forensics Secur 6(4):1223–1232
Acknowledgments
This work is supported in part by the Grants from Department of Science and Technology, No.DST/TSG/NTS/2011/173,Government of India & National Sustainability Program under Grant LO1401. For the research, Infrastructure of the Six Center was used.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Dutta, M.K., Singh, A. & Burget, R. Digital ownership tags based on biometric features of iris and fingerprint for content protection and ownership of digital images and audio signals. Multimed Tools Appl 75, 16287–16313 (2016). https://doi.org/10.1007/s11042-015-2931-8
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-015-2931-8