Abstract
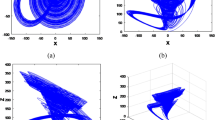
This paper introduces a secure chaos-based model for ciphering and deciphering of digital images. The proposed approach is composed of successive confusion and diffusion stages. The confusion stage is repeated n rounds using a different key in each round. The output of the confusion stage is subjected to diffusion stage which is repeated m rounds with a different key for each round. The nested iterations in the confusion and diffusion stages with a different key for each round enlarges the key space which enhances the proposed image cryptosystem security level. A security investigation is done on a family of 2D chaotic confusion maps to select the one with highest security level to be used with the proposed image cryptosystem. The results demonstrated that the Standard map has the highest security level among the examined 2D chaotic confusion maps because it is more complicated and it has a large key space. The proposed image cryptosystem is compared to other three recent image cryptosystems using different security analysis factors including statistical tests, key space analysis, information entropy test, maximum deviation analysis, irregular deviation analysis, and avalanche effect differential analysis. The results demonstrated that, the proposed image cryptosystem with Standard map outperforms all of the other examined image encryption techniques from security point of view.












Similar content being viewed by others
References
Abuturab MR (2013) Color image security system based on discrete Hartley transform in gyrator transform domain. Opt Lasers Eng 51(3):317–324
Alvarez G, Li S (2009) Cryptanalyzing a nonlinear chaotic algorithm (NCA) for image encryption. Commun Nonlinear Sci Numer Simul. doi:10.1016/j.cnsns. 2009.02.033
Amin M, Faragallah OS, Abd El-Latif AA (2009) Chaos-based hash function (CBHF) for cryptographic applications. Chaos, Solitons Fractals. doi:10.1016/j.chaos.2009.02.001
Askar SS, Karawia AA, Alshamrani A (2015) Image encryption algorithm based on chaotic economic model. Math Probl Eng. Article ID 341729, 1–10
Asmita, Lade S (2014) Chaotic encryption technique for color images by coupling two chaotic maps. IJCSNS Int J Comput Sci Netw Sec 14(10)
Behnia S, Akhshani A, Mahmodi H, Akhavan A (2008) A novel algorithm for image encryption based on mixture of chaotic maps. Chaos, Solitons Fractals 35:408–19
Behnia S, Akshshani A, Mahmodi H, Akhavan A (2008) A novel algorithm for image encryption based on mixture of chaotic maps. Chaos, Solitons Fractals 35:40
Chen G, Mao Y, Chui CK (2004) A symmetric image encryption scheme based on 3D chaotic cat maps. Chaos, Solitons Fractals 21:749–61
Crutchfield JP (1998) Spatio-temporal complexity in nonlinear image processing. IEEE Trans Circ Syst 35:770–80
Elashry IF, Faragallah OS, Abbas AM, El-Rabaie S, Abd El-Samie FE. Homomorphic image encryption. J Electron Imaging 18(3):033002
Elkamchouchi H, Makar MA (2005) Measuring encryption quality of Bitmap images encrypted with Rijndael and KAMKAR block ciphers. Proceedings of Twenty second National Radio Science Conference (NRSC 2005). pp. C11, Cairo Egypt 15–17
Fridrich J (1998) Symmetric ciphers based on two-dimensional chaotic maps. Int J Bifurcat Chaos 8(6):1259–84
Gai S, Yang G, Wan M (2013) Employing quaternion wavelet transform for banknote classification. Neurocompuing 118(8):171–178
Gai S, Yang G, Zhang S (2013) Multiscale texture classification using reduced quaternion wavelet transform. Int J Electron Commun 67(3):233–241
Gao T, Chen Z (2008) A new image encryption algorithm based on hyper-chaos. Phys Lett A 372:394–400
Gao HJ, Zhang YS, Liang SY, Li D (2006) A new chaotic algorithm for image encryption. Chaos, Solitons Fractals 29:393–9
Gong L, Liu X, Zheng F, Zhou N (2013) Flexible multiple-image encryption algorithm based on log-polar transform and double random phase encoding technique. J Mod Opt 60(13):1074–1082
Guan Z, Huang F, Guan W (2005) Chaos-based image encryption algorithm. Phys Lett A 346:153–7
Huang CK, Nien HH, Changchien SK, Shieh HW (2007) Image encryption with chaotic random codes by grey relational grade and Taguchi method. Opt Commun 280:300–10
Hwang H-E (2012) Optical color image encryption based on the wavelength multiplexing using cascaded phase-only masks in Fresnel transform domain. Opt Commun 285(5):567–573
Khan M, Shah T (2014) A literature review on image encryption techniques. 3D Res, 5, 29, 2014. doi:10.1007/s13319-014-0029-0
Kwok HS, Tang KS (2007) A fast image encryption system based on chaotic maps with finite precision representation. Chaos, Solitons Fractals 32(4):1518–29
Li C (2007) On the security of a class of image encryption schemes. IACR’s Cryptology ePrint Archive, Report 2007/339
Lian S (2009) Efficient image or video encryption based on spatiotemporal chaos system. Chaos, Solitons Fractals 40:2509–2519
Lian S, Sun J, Wang Z (2005) A block cipher based on a suitable use of the chaotic standard map. Chaos, Solitons Fractals 26:117–29
Lian SG, Sun J, Wang Z (2005) A block cipher based on a suitable use of chaotic standard map. Chaos, Solitons Fractals 26(1):117–29
Luo Y, Du M (2012) A novel digital image encryption scheme based on spatial-chaos. J Converg Inf Technol (JCIT) 7:3
Mao Y, Chen G, Lian S (2003) A novel fast image encryption scheme based on 3D chaotic baker maps. Int J Bifurcation Chaos
Mishra M, Singh P, Garg C (2014) A New algorithm of encryption and decryption of images using chaotic mapping. Int J Inf Comput Technol 4(7):741–746
Nien HH, Huang CK et al (2007) Digital color image encoding and decoding using a novel chaotic random generator. Chaos, Solitons Fractals 32:1070–80
Pareek NK, Patidar V, Sud KK (2006) Image encryption using chaotic logistic map. Image Vision Comput 24:926–34
Pareek NK, Patidar V, Sud KK (2006) Image encryption using chaotic logistic map. Image Vision Comput 24:926–34
Pisarchik AN, Flores-Camona NJ, Carpio-Valadez M (2006) Encryption and decryption of images with chaotic map lattices. Chaos 16:033118-1–6
Rhouma R, Belghith S (2008) Cryptanalysis of a new image encryption algorithm based on hyper-chaos. Phys Lett A 372:5973–5978
Rhouma R, Belghith S (2008) Cryptanalysis of a spatiotemporal chaotic image/video cryptosystem. Phys Lett A 372:5790–5794
Sathishkumar GA, Bhoopathybagan K, Sriraam N, Venkatachalam SP, Vignesh R (2011) A novel image encryption algorithm using two chaotic maps for medical application. Adv Comput Commun Comput Inf Sci 133:290–299, Berlin-Heidelberg: Springer-Verlag
Shannon CE (1949) Communication theory of secrecy system. Bell Syst Technol J 28:656–715
Sun F, Liu S, Li Z, Lü Z (2008) A novel image encryption algorithm based on spatial chaos map. Chaos, Solitons Fractals 38:631–640
Wang K, Pei L, Zou A, Song ZH (2005) On the security of 3D Cat map based symmetric image encryption scheme. Phys Lett A 343(6):432–439
Wong KW, Kwok BS, Lawk WS (2007) A fast image encryption scheme based on chaotic standard map. Phys Lett A. doi:10.1016/ j.physleta.2007.12.026
Xiang T, Wong KW, Liao X (2007) Selective image encryption using a spatiotemporal chaotic system. Chaos 17:023115-1–12
Zhang LH, Liao XF, Wang XB (2005) An image encryption approach based on chaotic maps. Chaos, Solitons Fractals 24:759–65
Zhou N, Wang Y, Gong L (2011) Novel optical image encryption scheme based on fractional Mellin transform. Opt Commun 284(13):3234–3242
Zhou N, Zhang A, Zheng F, Gong L (2014) Novel Image compression-encryption hybrid algorithm based on key-controlled measurement matrix in compressive sensing. Opt Laser Technol 62:152–160
Ziedan IE, Fouad MM, Salem DH (2003) Application of data encryption standard to bitmap and JPEG images. In Proc. 12th National Radio Science Conference (NRSC2003), pp. C16/1–C16
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Elgendy, F., Sarhan, A.M., Eltobely, T.E. et al. Chaos-based model for encryption and decryption of digital images. Multimed Tools Appl 75, 11529–11553 (2016). https://doi.org/10.1007/s11042-015-2883-z
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-015-2883-z