Abstract
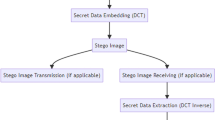
On the basis of the analysis of JPEG error and stegonoise, we propose a novel quantitative steganalyzer for spatial ±1 steganography in JPEG decompressed images. First, we present a particular theoretical argument that the cover images, which are originally stored in JPEG format, can be approximately estimated through JPEG recompression with the detected quantization table. Then, on the basis of the relationship between the message embedding rate and the variance of the stegonoise in the discrete cosine transformation (DCT) domain, we construct a polynomial regression model to estimate the secret message length. The extensive experimental results show that the proposed scheme is computationally feasible and that it significantly outperforms the existing state-of-the-art estimators, especially for the images with high quality factors and embedding rates. The order of magnitude of the prediction error using the proposed scheme can remain in the 10−4 range, as measured by the median absolute difference. Moreover, our estimator is stable and robust with respect to the embedding rate and quality factor.







Similar content being viewed by others
Abbreviations
- DCT:
-
Discrete Cosine Transform
- LSB:
-
Least Significant Bit
- RS:
-
Regular and Singular
- HCF-COM:
-
The Center of the Mass of the Histogram Characteristic Function
- AHCF-COM:
-
The Center Of the Mass of the Adjacency Histogram Characteristic Function
- ALE:
-
The amplitude of local extrema
- i.i.d.:
-
Independent identically distributed
- MAE:
-
Mean absolute error
- MAD:
-
Median absolute difference
- IQR:
-
Interquartile range
References
Bas P, Furon T (2007) BOWS-2 [Online]. http://bows2.gipsa-lab.inpg.fr. Accessed May 11 2010
Böhme R (2008) Weighted stego-image steganalysis for JPEG covers. In: Proceedings of 10th International Workshop on Information Hiding, Springer LNCS, 5284: 178–194. doi: 10.1007/978-3-540-88961-8_13
Doёrr G Image database for steganalysis studies [Online]. http://www.cs.ucl.ac.uk/staff/I.Cox/Content/Downloads.html. Accessed May 11 2009
Dumitrescu S, Wu X, Wang Z (2003) Detection of LSB steganography via sample pair analysis. IEEE Trans Signal Process 51(7):1995–2007. doi:10.1109/TSP.2003.812753
Fan Z, de Queiroz R (2003) Identification of bitmap compression history: JPEG detection and quantizer estimation. IEEE Trans Image Process 12(2):230–235. doi:10.1109/TIP.2002.807361
Fridrich J, Goljan M, Du R (2001) Detecting LSB steganography in color and gray-scale images. IEEE Multimedia 8(4):22–28. doi:10.1109/93.959097
Fridrich J, Goljan M, Du R (2001) Steganalysis based on JPEG compatibility. In: Proceedings of Special Session on Theoretical and Practical Issues in Digital Watermarking and Data Hiding, Multimedia Systems and Applications IV, pp 275–280
Fridrich J, Soukal D, Goljan M (2005) Maximum likelihood estimation of secret message length embedded using ±k steganography in spatial domain. In Proceedings of the SPIE, Electronic Imaging, Security, Steganography, and Watermarking of Multimedia Contents VII, San Jose, CA, 5681: 595–606
Fu D, Shi Y Q, Su W (2007) A generalized benford’s law for JPEG coefficients and its applications in image forensics. In: Proceedings of the SPIE Electronic Imaging, Security, Steganography, and Watermarking of Multimedia Contents IX, E. J. Delp and P. W. Wong, Eds., San Jose, CA, 6505: 1L1-1L11
Harmsen J, Pearlman W (2003) Steganalysis of additive noise modelable information hiding. In Proceedings of the SPIE, Electronic Imaging, Security and Watermarking of Multimedia Contents V, Sa-nta Clara, CA, 5020: 131–142
Huang HC, Chu SC, Pan JS, Huang CY, Liao BY (2011) Tabu search based multi-watermarks embedding algorithm with multiple description coding. Inform Sci 181(16):3379–3396. doi:10.1016/j.ins.2011.04.007
Huang HC, Fang WC (2010) Metadata-based image watermarking for copyright protection. Simul Model Pract Theory 18(4):436–445. doi:10.1016/j.bbr.2011.03.031
Ker AD (2005) Steganalysis of LSB matching in grayscale images. IEEE Signal Process Lett 12(6):441–444. doi:10.1109/LSP.2005.847889
Li X, Zhang T, Zhang Y, Li WX, Li KD (2012) A novel blind detector for additive noise steganography in JPEG decompressed images. Multimedia Tools and Applications. doi:10.1007/s11042-012-1112-2
Loukhaoukha K (2012) On the security of digital watermarking scheme based on singular value decomposition and tiny genetic algorithm. J Inf Hiding Multimedia Signal Process 3(2):135–141
Luo WQ, Huang FJ, Huang JW (2010) JPEG error analysis and its applications to digital image forensics. IEEE Trans Inf Forensic Secur 5(3):480–491. doi:10.1109/TIFS.2010. 2051426
Luo WQ, Wang Y, Huang JW (2011) Security analysis on spatial ±1 steganography for JPEG decompressed images. IEEE Signal Process Lett 18(1):39–42
NRCS Photo Gallery [Online]. http://photogallery.nrcs.usda.gov/. Accessed August 22 2009
Petitcolas FAP, Anderson RJ, Kuhn MG (1999) Information hiding-a survey. In: Proceedings of the IEEE, 87(7): 1062–1078. doi: S 0018-9219(99)04946-4
Pevný T, Fridrich J, Ker AD (2012) From blind to quantitative steganalysis. IEEE Transactions on Information Forensics and Security 7(2):445–454. doi:10.1109/TIFS.2011.2175918
Schaefer G, Stich M (2003) UCID: An uncompressed color image database. In Proceedings of the SPIE, Electronic Imaging, Storage and Retrieval Methods and Applications for Multimedia. 5307: 472–480
Sharp T (2001) An implementation of key-based digital signal steganography. In: Proceedings of the 4th International Workshop on Information Hiding, Springer LNCS, 2137: 13–26. doi:10.1007/3-540-45496-9_2
Zhang J, Cox IJ, Doёrr G (2007) Steganalysis for LSB matching in images with high-frequency noise. In: Proc. IEEE 9th Workshop on Multimedia Signal Processing, pp. 385–388. doi:10.1109/MMSP.2007.4412897
Zhang T, Li WX, Zhang Y, Zheng EG, Ping XJ (2010) Steganalysis of LSB matching based on statistical modeling of pixel difference distributions. Information Sciences 180:4685–4694. doi:10.1016/j.ins.2010.07.037
Zhang T, Ping XJ (2003) A new approach to reliable detection of LSB steganography in natural images. Signal Process 83(10):2085–2093. doi:10.1016/S0165-1684(03)00169-5
Zhang J, Zhang D (2010) Detection of LSB matching steganography in decompressed images. IEEE Signal Process Lett 17(2):141–144. doi:10.1109/LSP.2009.2035379
Zheng EG, Ping XJ, Zhang T (2011) Local linear transform and new features of histogram characteristic functions for steganalysis of least significant bit matching steganography. KSII Trans Internet Inf Syst 5(4):840–855. doi:10.3837/tiis.2011.04.012
Zhu X, Chen Y (2012) Performance analysis of dither modulation against composite attacks. J Inf Hiding Multimedia Signal Process 3(2):164–175
Acknowledgments
This work was supported by the National Natural Science Foundation of China (No. 60903221, No. 61272490) and the National High Technology Research and Development Program of China (“863” Program, No. 2011AA010603, No. 2011AA010605). The authors would like to thank the reviewers for their insightful comments and helpful suggestions.
Author information
Authors and Affiliations
Corresponding author
Appendix
Appendix
In the appendix, we show the proof of Theorem I. The process is as follows.
According to 2-D DCT and the values of u and v, three cases are discussed:
-
I.
When u 2 + v 2 = 0,
$$ F\left(0,0\right)=\frac{1}{8}{\displaystyle \sum_{i=0}^7{\displaystyle \sum_{j=0}^7f\left(i,j\right)}} $$(18)As known, the i.i.d. random variable f(i, j) possesses a mean of 0 and variance σ 2. According to the property of the mean and variance, we can easily obtain the mean of F(0, 0) is 0, and its variance is σ 2. According to the Central Limit Theorem, F(0, 0) approximately follows the Gaussian distribution with a mean of 0 and variance σ 2, which is denoted by F(0, 0) ~ N(0, σ 2).
-
II.
When uv = 0 and u 2 + v 2 ≠ 0, without loss of generality, we set u = 0, v ≠ 0. Then, we have
$$ F\left(0,v\right)=\frac{1}{4\sqrt{2}}{\displaystyle \sum_{i=0}^7{\displaystyle \sum_{j=0}^7f\left(i,j\right) \cos \frac{\left(2j+1\right) v\pi}{16}}},1\le v\le 7 $$(19)The mean of F(0, v) is 0. Setting its variance to B 21 , then
$$ \begin{array}{c}\hfill {B}_1{}^2=\frac{1}{32}{\displaystyle \sum_{i=0}^7{\displaystyle \sum_{j=0}^7{\sigma}^2{ \cos}^2\frac{\left(2j+1\right) v\pi}{16}}}\hfill \\ {}\hfill =\frac{\sigma^2}{32}{\displaystyle \sum_{i=0}^7\left(4+\frac{1}{2}{\displaystyle \sum_{j=0}^7 \cos \frac{\left(2j+1\right) v\pi}{8}}\right)}\hfill \\ {}\hfill =\frac{\sigma^2}{32}{\displaystyle \sum_{i=0}^7\left(4+{\displaystyle \sum_{j=0}^3 \cos \frac{\left(2j+1\right) v\pi}{8}}\right)}\hfill \end{array} $$(20)Let \( S={\displaystyle \sum_{j=0}^3 \cos \frac{\left(2j+1\right) v\pi}{8}}= \cos \frac{ v\pi}{8}+ \cos \frac{3 v\pi}{8}+ \cos \frac{5 v\pi}{8}+ \cos \frac{7 v\pi}{8} \). When v is an odd number, \( \cos \frac{7 v\pi}{8}= \cos \left( v\pi -\frac{ v\pi}{8}\right)=- \cos \frac{ v\pi}{8} \) and \( \cos \frac{5 v\pi}{8}=- \cos \frac{3 v\pi}{8} \), then S = 0; when v is an even number, \( \cos \frac{7 v\pi}{8}= \cos \frac{ v\pi}{8} \), \( \cos \frac{5 v\pi}{8}= \cos \frac{3 v\pi}{8} \), then \( S=2\left( \cos \frac{ v\pi}{8}+ \cos \frac{3 v\pi}{8}\right)=0 \). In sum, \( \begin{array}{cc}\hfill {\displaystyle \sum_{j=0}^3 \cos \frac{\left(2j+1\right) v\pi}{8}}=0,\hfill & \hfill 1\le v\le 7\hfill \end{array} \). Substituting it into Eq. (20), we obtain B 21 = σ 2.
According to the Central Limit Theorem, we have F(0, v) ~ N(0, σ 2), 1 ≤ v ≤ 7. Similarly, we can get F(u, 0) ~ N(0, σ 2) when v = 0 and 1 ≤ u ≤ 7.
-
III.
When uv ≠ 0,
$$ F\left(u,v\right)=\frac{1}{4}{\displaystyle \sum_{i=0}^7{\displaystyle \sum_{j=0}^7f\left(i,j\right) \cos \frac{\left(2i+1\right) u\pi}{16} \cos \frac{\left(2j+1\right) v\pi}{16}}},1\le u,v\le 7 $$(21)The mean of F(u,v) is 0, which can be easily obtained. Setting its variance to B 22 , we have
$$ \begin{array}{c}\hfill {B}_2{}^2=\frac{1}{16}{\displaystyle \sum_{i=0}^7{\displaystyle \sum_{j=0}^7{\sigma}^2{ \cos}^2\frac{\left(2i+1\right) u\pi}{16}{ \cos}^2\frac{\left(2j+1\right) v\pi}{16}}}\hfill \\ {}\hfill =\frac{\sigma^2}{16}\left({\displaystyle \sum_{i=0}^7{ \cos}^2\frac{\left(2i+1\right) u\pi}{16}}\right)\left({\displaystyle \sum_{j=0}^7{ \cos}^2\frac{\left(2j+1\right) v\pi}{16}}\right)\hfill \\ {}\hfill =\frac{\sigma^2}{16}\left(4+\frac{1}{2}{\displaystyle \sum_{i=0}^7 \cos \frac{\left(2i+1\right) u\pi}{8}}\right)\left(4+\frac{1}{2}{\displaystyle \sum_{j=0}^7 \cos \frac{\left(2j+1\right) v\pi}{8}}\right)\hfill \\ {}\hfill =\frac{\sigma^2}{16}\left(4+{\displaystyle \sum_{i=0}^3 \cos \frac{\left(2i+1\right) u\pi}{8}}\right)\left(4+{\displaystyle \sum_{j=0}^3 \cos \frac{\left(2j+1\right) v\pi}{8}}\right)\hfill \\ {}\hfill ={\sigma}^2\hfill \end{array} $$(22)According to the Central Limit Theorem, F(u, v) ~ N(0, σ 2), 1 ≤ u, v ≤ 7.
In conclusion, {F(u,v)|0 ≤ u, v ≤ 7} approximately follows a Gaussian distribution with a mean of 0 and a variance of σ 2, namely, F(u, v) ~ N(0, σ 2).
Rights and permissions
About this article
Cite this article
Li, X., Zhang, T., Zhang, Y. et al. Quantitative steganalysis of spatial ±1 steganography in JPEG decompressed images. Multimed Tools Appl 73, 1487–1506 (2014). https://doi.org/10.1007/s11042-013-1654-y
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-013-1654-y